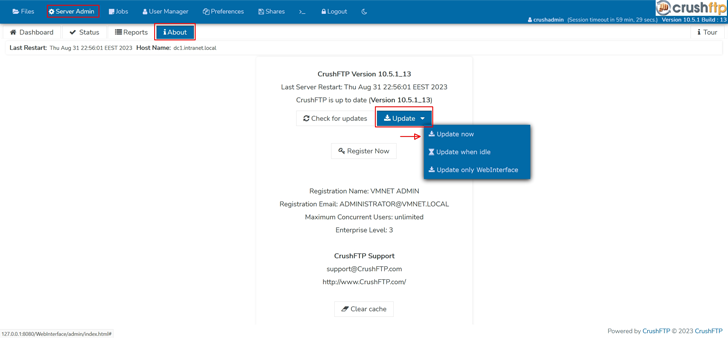
People of the CrushFTP business file transfer software program are getting urged to update to the most recent version adhering to the discovery of a security flaw that has arrive below focused exploitation in the wild.
“CrushFTP v11 versions below 11.1 have a vulnerability exactly where users can escape their VFS and obtain system files,” CrushFTP stated in an advisory unveiled Friday. “This has been patched in v11.1..”
That claimed, customers who are operating their CrushFTP instances within just a DMZ (demilitarized zone) restricted ecosystem are shielded towards the attacks.

Simon Garrelou of Airbus CERT has been credited with identifying and reporting the flaw. It has however to be assigned a CVE identifier.
Cybersecurity corporation CrowdStrike, in a publish shared on Reddit, mentioned it has observed an exploit for the flaw being utilized in the wild in a “specific vogue.”
These intrusions are said to have largely focused U.S. entities, with the intelligence gathering exercise suspected to be politically motivated.
“CrushFTP customers should really proceed to observe the vendor’s internet site for the most up-to-date guidance and prioritize patching,” CrowdStrike reported.
Discovered this short article intriguing? Stick to us on Twitter and LinkedIn to read much more exclusive material we put up.
Some parts of this article are sourced from:
thehackernews.com

 BlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
BlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool