As many as 7 security vulnerabilities have been disclosed in PTC’s Axeda program that could be weaponized to get unauthorized access to medical and IoT units.
Collectively termed “Access:7,” the weaknesses – 3 of which are rated Critical in severity – perhaps affect additional than 150 product designs spanning in excess of 100 diverse makers, posing a significant supply chain risk.
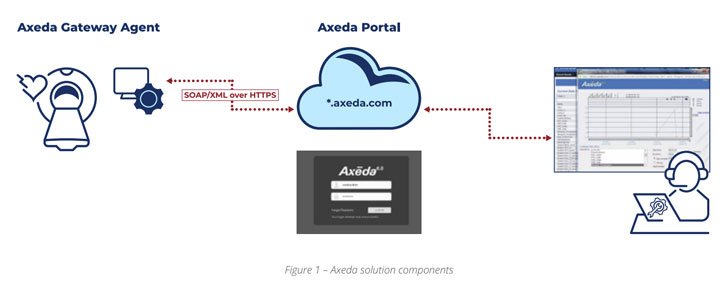
PTC’s Axeda remedy includes a cloud system that lets system makers to set up connectivity to remotely watch, regulate and services a vast vary of connected devices, sensors, and units by way of what is actually known as the agent, which is mounted by the OEMs before the equipment are marketed to prospects.
“Accessibility:7 could empower hackers to remotely execute destructive code, access sensitive facts, or change configuration on health care and IoT products operating PTC’s Axeda distant code and administration agent,” researchers from Forescout and CyberMDX reported in a joint report released nowadays.
Of the 100 impacted gadget suppliers, 55% belong to the health care sector, adopted by IoT (24%), IT (8%), economic expert services (5%), and production (4%) industries. No considerably less than 54% of the clients with equipment managing Axeda have been recognized in the health care sector.
Moreover healthcare imaging and laboratory devices, susceptible equipment include things like every thing from ATMs, vending equipment, money administration units, and label printers to barcode scanning devices, SCADA programs, asset monitoring and monitoring alternatives, IoT gateways, and industrial cutters.
The checklist of flaws is down below –
- CVE-2022-25246 (CVSS rating: 9.8) – The use of hard-coded qualifications in the AxedaDesktopServer.exe service that could empower remote takeover of a device
- CVE-2022-25247 (CVSS score: 9.8) – A flaw in ERemoteServer.exe that could be leveraged to ship specifically crafted commands to acquire Distant code execution (RCE) and whole file method entry
- CVE-2022-25251 (CVSS rating: 9.4) – Lacking authentication in the Axeda xGate.exe agent that could be applied to modify the agent’s configuration
- CVE-2022-25249 (CVSS score: 7.5) – A listing traversal flaw in the Axeda xGate.exe agent which could enable a distant unauthenticated attacker to get file technique browse accessibility on the web server
- CVE-2022-25250 (CVSS rating: 7.5) – A denial-of-support (DoS) flaw in the Axeda xGate.exe agent by injecting an undocumented command
- CVE-2022-25252 (CVSS rating: 7.5) – A buffer overflow vulnerability in the Axeda xBase39.dll ingredient that could result in a denial-of-service (DoS)
- CVE-2022-25248 (CVSS score: 5.3) – An details disclosure flaw in the ERemoteServer.exe assistance that exposes the dwell occasion textual content log to unauthenticated parties
Thriving exploitation of the flaws could equip attackers with capabilities to remotely execute destructive code to choose total regulate of devices, accessibility delicate data, modify configurations, and shut down unique expert services in the impacted devices.
The flaws, which have an effect on all versions of the Axeda Agent prior to 6.9.3, have been noted to PTC on August 10, 2021 as part of a coordinated disclosure approach that included the U.S. Cybersecurity and Infrastructure Security Agency (CISA), Health and fitness Facts Sharing and Analysis Heart (H-ISAC), and the Food items and Drug Administration (Fda).

To mitigate the flaws and prevent possible exploitation, buyers are suggested to improve to Axeda agent edition 6.9.1 make 1046, 6.9.2 construct 1049, or 6.9.3 create 1051.
This is not the to start with time critical security vulnerabilities mainly concentrating on healthcare programs have come to light-weight. In December 2020, CyberMDX disclosed “MDhex-Ray,” a intense flaw in GE Healthcare’s CT, X-Ray, and MRI imaging items that could outcome in the exposure of secured health information and facts.
“Accessibility:7 has an effect on a option bought to product suppliers that did not establish their in-house distant servicing process,” the scientists explained. “This can make it a offer chain vulnerability and that’s why it impacts several downstream suppliers and products.”
Discovered this posting interesting? Abide by THN on Fb, Twitter and LinkedIn to study a lot more distinctive information we write-up.
Some parts of this article are sourced from:
thehackernews.com

