Days soon after the Conti ransomware team broadcasted a pro-Russian information pledging its allegiance to Vladimir Putin’s ongoing invasion of Ukraine, a disgruntled member of the cartel has leaked the syndicate’s interior chats.
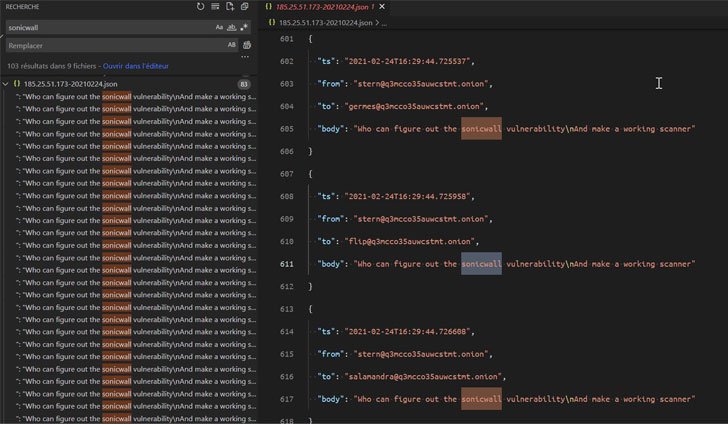
The file dump, posted by malware research team VX-Underground, is claimed to contain 13 months of chat logs involving affiliate marketers and directors of the Russia-affiliated ransomware team from January 2021 to February 2022, in a shift that is anticipated to offer you unparalleled insight into the gang’s workings.
“Glory to Ukraine,” the leaker explained in their message.
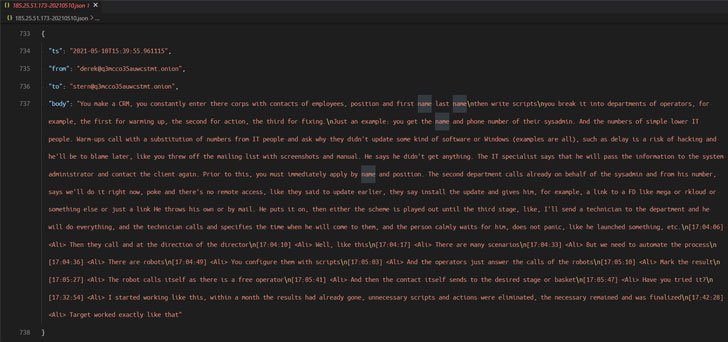
The leaked discussions display that Conti made use of phony entrance firms to try to program product demos with security firms like CarbonBlack and Sophos to get hold of code signing certificates, with the operators operating in scrum sprints to complete the program growth duties.

Also, the messages ensure the shutdown of the TrickBot botnet very last week as perfectly as emphasize the Conti group’s shut partnership with the TrickBot and Emotet malware gangs, the latter of which was resurrected late past year as a result of TrickBot.
A message despatched by one of the associates of the group on February 14, 2022 goes: “TrickBot does not function. The project was closed.”
On top of that, the leaker is also considered to have unveiled the source code related with TrickBot’s command dispatcher and data collector modules, not to point out the ransomware group’s interior documentation.
The growth arrives as the Russo-Ukrainian conflict has splintered the cybercrime underground into two warring factions, with a escalating number of hacking actors buying sides concerning the two nations around the world on the digital front.
The Conti crew, in a site article on its dark web portal very last week, avowed its “complete guidance” to the Russian invasion, and threatened to retaliate in opposition to critical infrastructure if Russia is strike with cyber or military services attacks.
It, nonetheless, later backtracked, stating, “we do not ally with any governing administration and we condemn the ongoing war,” but reiterated that “We will use our sources in purchase to strike again if the nicely getting and security of peaceful citizens will be at stake due to American cyber aggression.”

The ContiLeaks saga is element of a broader exertion by hacktivists and security allies, together with Ukraine’s “IT army,” to strike Russian web-sites, products and services and infrastructure as a counter to Kremlin’s army strikes. The volunteer hacking team, in messages shared on its Telegram channel, claimed that various Russian internet websites and state on the net portals have been felled by a barrage of DDoS attacks.
Individually, a team of Belarusian hackers recognized as the Cyber Partisans mentioned they staged an attack on the country’s teach network in an energy to disrupt Russian troop movements into Ukraine, although another group termed AgainstTheWest_ reported was “standing against Russia” and that it breached a quantity of internet sites and corporations.
The Nameless, for its portion, also claimed duty for disrupting the web-sites of point out news companies RT, TASS, and RIA Novosti, as effectively as websites of newspapers Kommersant, Izvestiya, and Forbes Russia magazine and the Russian oil giant Gazprom.
If anything at all, the quickly evolving cyber war appears to have place other teams on warn, what with LockBit ransomware operators submitting a neutral message, stating “For us it is just company and we are all apolitical. We are only intrigued in income for our harmless and valuable function.”
Uncovered this article exciting? Comply with THN on Facebook, Twitter and LinkedIn to browse additional special content we article.
Some parts of this article are sourced from:
thehackernews.com

 Airbnb offers free housing for up to 100,000 Ukrainian refugees
Airbnb offers free housing for up to 100,000 Ukrainian refugees