The decryptor spilled by ContiLeaks won’t perform with the latest victims. Conti couldn’t care less: It’s however operating just fantastic. Nonetheless, the dump is a bouquet’s worth of intel.
The pro-Ukraine member of the Conti ransomware gang who promised to eviscerate the extortionists right after they pledged help for the Russian federal government has spilled but much more Conti guts: The most up-to-date dump contains supply code for Conti ransomware, TrickBot malware, a decryptor and the gang’s administrative panels, among the other core insider secrets.
On Monday, vx-underground – an internet selection of malware source code, samples and papers which is typically regarded as to be a benign entity – shared on Twitter a information from a Conti member declaring that “This is a welcoming heads-up that the Conti gang has just dropped all their sh•t.”
The 1st of what ContiLeaks promised would be a collection of “very interesting” leaks involved 60,000 of the Conti gang’s inner chat messages.
The Conti Intel Treasure Trove
Then, on Tuesday, ContiLeaks leaked even extra of Conti’s widespread ways, procedures and treatments (TTPs), which were being shared by vx-underground.
In a Wednesday evaluation, CyberArk scientists enumerated the leaked written content and why it is vital. This intel is very important as Russian tanks roll by means of Ukraine and cyberattacks fly in support of either aiding the besieged region or tripping up the aggressor, CyberArk researchers asserted.
Its evaluation pointed to a cybersecurity bulletin issued jointly above the weekend by the Cybersecurity and Infrastructure Company (CISA) and the FBI: an advisory that warned that Russia’s attack on Ukraine – which has included cyberattacks on Ukrainian governing administration and critical infrastructure companies – may spill more than Ukraine’s borders, significantly in the wake of sanctions imposed by the United States and its allies.
“As cybersecurity scientists, we imagine insight received from these leaks is very important to the cybersecurity neighborhood at large. Ongoing consciousness and visibility into the leaked tools when supporting the need for ongoing vigilance is critical through this time, and strengthened by [the CISA/FBI alert].”
What’s in the 2nd Dump
The documents shared by ContiLeaks have a slew of refreshing meat, with some dated as not long ago as yesterday, March 1.
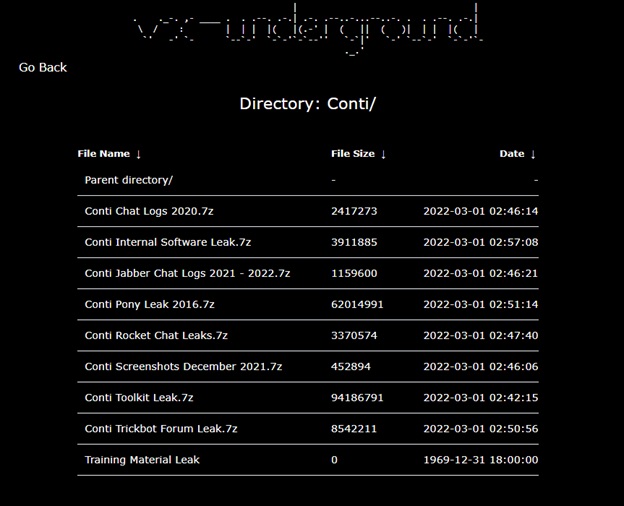
ContiLeaks’ info dump content material as of March 1. Source: vx-underground.
Here’s a assortment of the repositories and what scientists can do with them:
Chats
As considerably as the leaked chats go, they span inside communications of the Conti gang amongst June and November 2020. CyberArk noted that 1 person in particular “frequently spams all the other consumers.”
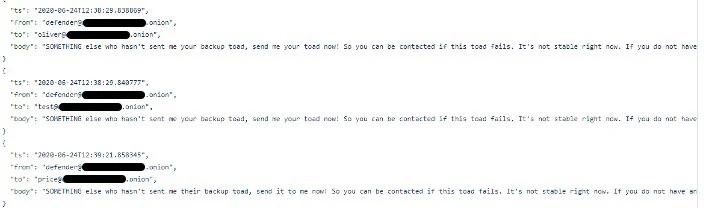
This can also be a handy resource for us to examine considering that we can see probably even all the usernames in one put, allowing us to enumerate all the men and women in the Conti team.
The chats will permit researchers to see a superior chunk of Conti gang usernames in a single put, scientists mentioned, “allowing us to enumerate all the people today in the Conti group.”
Admin Panel Code
A brief search at the cache’s repositories led the scientists to surmise that most of the code Conti employs appears to be open up-resource computer software. They pointed to two illustrations: the two PHP frameworks yii2 and Kohana, which are “used as element of (what would seem to be) the admin panel,” they stated.
“The code is mostly composed in PHP and is managed by Composer, with the exception of one repository of a software published in Go,” they stated. The repositories also consist of some config documents that record local databases usernames and passwords, as effectively as a couple of community IP addresses.
Qualifications Ripped Off by Pony Malware
The Conti Pony Leak 2016 repository is made up of a assortment of email accounts and passwords – such as from mail products and services these kinds of as gmail.com, mail.ru and yahoo.com – that have been apparently stolen from a variety of resources by the Pony credential-stealing malware: a credential stealer that, at minimum as of 2018, was crooks’ most loved stealer.
It also is made up of qualifications from FTP/ RDP and SSH solutions, additionally qualifications from unique sites.
TTPs
The Conti Rocket Chat Leaks consists of a chat historical past of Conti members swapping guidelines about targets and carrying out attacks by means of crooks’ most loved: Cobalt Strike, the respectable, commercially obtainable instrument utilised by network penetration testers and by crooks to sniff out vulnerabilities.
The Conti gang chatters talked about these procedures:
- Lively Directory Enumeration
- SQL Databases Enumeration via sqlcmd.
- How to gain obtain to Shadow Defend SPX (StorageCraft) backups.
- How to make NTDS dumps vs vssadmin
- How to open up New RDP Port 1350
And these tools:
- Cobalt Strike
- Metasploit
- PowerView
- ShareFinder
- AnyDesk
- Mimikatz
Conti Locker v2 & the Decryptor That Most likely De-Will not
The dump also incorporates the resource code for Conti Locker v2, which was initially leaked as a password-shielded zip file but then once again without having any password.
Moreover the resource code for v2 of the ransomware encryption resource code, the leak also contained source code for the decryptor – a decryptor that reportedly won’t get the job done, as pointed out on Twitter.
Just a heads up: The decryptor code contained inside of this offer is not the newest model and will not work for the most current Conti victims.
— Fabian Wosar (@fwosar) March 1, 2022
“I had heard it’s not the most current variation and does not function,” Marcus confirmed.
The introduced decryptor might be a version that Conti sends to victims who’ve compensated the ransom, he suggested.
Decryptors act sort of like unzipping a password-protected file, he recommended, other than that they are a lot more sophisticated, presented that they change by the ransomware spouse and children.
“Some are constructed into a standalone binary, some others can be remote-enabled. Generally they have keys developed into them,” Marcus described.
Conti Coaching Components
The leaked documents also consist of schooling elements, together with films of online classes in Russian, as effectively as how-tos about this checklist of TTPs:
- Cracking
- Metasploit
- Network Pentesting
- Cobalt Strike
- PowerShell for Pentesters
- Windows Crimson Teaming
- WMI Attacks (and Defenses)
- SQL Server
- Lively Listing
- Reverse Engineering

Conti schooling in Russia. Course: CyberArk.
TrickBot Leaks
A person of the leaked data files is a dump of chats from the community forums utilized by the operators of the TricKBot trojan/malware, spanning forum messages from 2019 until 2021.
Most of the chats are about how to shift laterally across networks and how to use specific applications, but CyberArk also uncovered out very a little bit about the TrickBot and Conti gang’s TTPs.
“For occasion in just one of the correspondences a member shares his web shell of option, ‘he lightest and most sturdy webshell I use,’” scientists stated.
Also incorporated are evidence from early July 2021 that the team used exploits this kind of as Zerologon: Not shocking, supplied that starting off in September 2020, at least four community proof-of-strategy (PoC) exploits for the flaw were being released on Github, along with complex particulars of the vulnerability.
Other TrickBot leaks incorporate server-aspect components published in Erlang, a trickbot-command-dispatcher-backend and trickbot-details-collector-backend, dubbed lero and dero.
Thank heavens for the readable code, explained a single Twitter commenter: “That’s ultimately a thing truly worth examining (Conti Trickbot Leaks.7z file) – clean up, reusable implementation in Erlang, better than several open source Erlang server examples.”
Which is last but not least some thing value examining (Conti Trickbot Leaks.7z file) – cleanse, reusable implementation in Erlang, greater than several open source Erlang server illustrations.
— PAYLOAD – magazyn o ofensywnym bezpieczeństwie IT (@PayloadPl) March 1, 2022
TrickBot Code Could Lead to … Much better TrickBot
Will the leak slow down TrickBot operators? Effectively, it did not actually have to, given that the operators currently seem to have taken a handful of hits of Zanax.
Last 7 days, scientists at Intel 471 posted a report about how the team guiding the TrickBot malware is back again soon after an unusually very long lull between strategies. If not a whole stop, they’ve been functioning pretty languidly: from Dec. 28, 2021 until Feb. 17, Intel 471 researchers hadn’t found any new TrickBot strategies.
Researchers stated at the time that the pause could be due to the TrickBot gang generating an operational shift to concentrate on partner malware, this sort of as Emotet.
The ContiLeaks source code leak could, even so, change the scene, and not for the much better. David Marcus, senior director of risk intelligence at danger-intel security enterprise LookingGlass, instructed Threatpost on Wednesday that the leaks will have “a enormous impact” prolonged phrase as security researchers continue to exploration the fresh new facts. “The total we will find out about their practices, code growth, monetization efforts, prospective users and this kind of can not be overstated,” he reported by using email.
But as considerably as the supply code leak is concerned, that will be a double-edged sword, he cautioned. “It will gain researchers from a defensive level-of-see, as a greater knowledge of how TrickBot operates will allow for for improved defensive actions,” he mentioned. “The flip aspect of that is that it will also make it possible for for much more TrickBot enhancement by additional malware writers.”
Conti Couldn’t Treatment Less
As far as the leak of Conti code goes, it would be good to imagine that the gang’s operators ended up howling in pain at the disclosures, but that is not accurately what is going on.
Yelisey Boguslavskiy, head of exploration at the threat intel business Advanced Intelligence (AdvInt), told Threatpost on Wednesday that none of the firm’s main resource intel demonstrates that this will affect Conti.
“The leak was linked to only just one team out of 6, and even although this group was likely the most important just one, the relaxation of the groups were not impacted at all,” he explained. “Conti relaunched all of its infrastructural capacities and hold functioning.”
Shifting to the cloud? Discover rising cloud-security threats together with reliable advice for how to defend your belongings with our No cost downloadable Ebook, “Cloud Security: The Forecast for 2022.” We check out organizations’ best dangers and problems, best practices for protection, and advice for security good results in these kinds of a dynamic computing natural environment, such as handy checklists.
Some parts of this article are sourced from:
threatpost.com


