The U.S. Cybersecurity and Infrastructure Security Company (CISA) issued an advisory on Thursday warning that the recently disclosed critical security flaw in Citrix NetScaler Software Supply Controller (ADC) and Gateway equipment is staying abused to fall web shells on susceptible methods.
“In June 2023, danger actors exploited this vulnerability as a zero-day to drop a web shell on a critical infrastructure organization’s non-creation atmosphere NetScaler ADC appliance,” the agency stated.
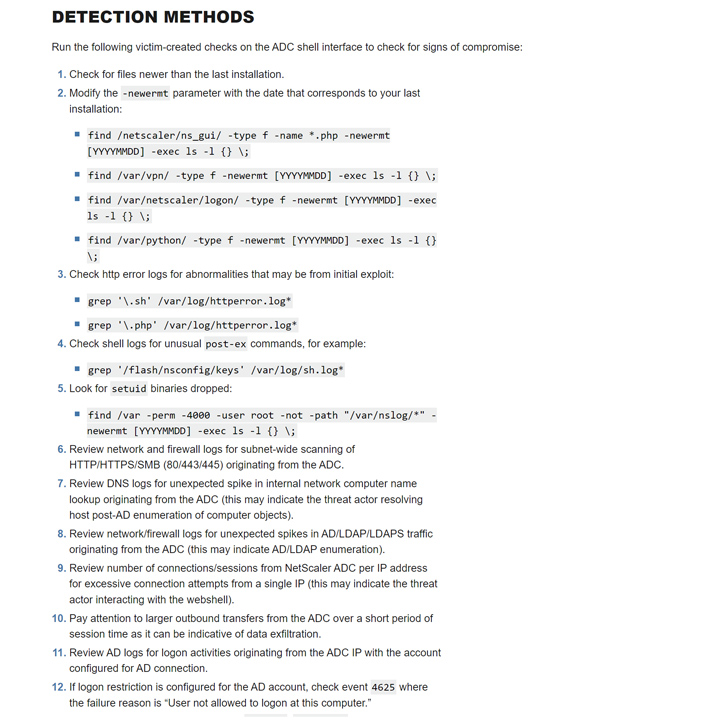
“The web shell enabled the actors to carry out discovery on the victim’s active listing (Advert) and accumulate and exfiltrate Advert facts. The actors tried to shift laterally to a area controller but network segmentation controls for the appliance blocked movement.”
The shortcoming in problem is CVE-2023-3519 (CVSS score: 9.8), a code injection bug that could consequence in unauthenticated distant code execution. Citrix, earlier this 7 days, produced patches for the issue and warned of active in-the-wild exploitation.
Productive exploitation needs the equipment to be configured as a Gateway (VPN digital server, ICA Proxy, CVPN, RDP Proxy) or authentication, authorization, and auditing (AAA) digital server.
CISA did not disclose the identify of the firm that was impacted by the incident. The danger actor or the state allegedly powering it is presently not known.
In the incident analyzed by CISA, the web shell is mentioned to have enabled the collection of NetScaler configuration files, NetScaler decryption keys, and Advert info, right after which the knowledge was transmitted as a PNG impression file (“medialogininit.png”).
Approaching WEBINARShield Towards Insider Threats: Master SaaS Security Posture Management
Nervous about insider threats? We’ve received you protected! Sign up for this webinar to check out simple approaches and the techniques of proactive security with SaaS Security Posture Management.
Join Right now
The adversary’s subsequent tries to laterally move across the network as perfectly as operate commands to identify available targets and verify outbound network connectivity were thwarted due to robust network segmentation tactics, the agency observed, including the actors also attempted to delete their artifacts to deal with up the tracks.
Vulnerabilities in gateway products these kinds of as NetScaler ADC and NetScaler Gateway have come to be common targets for threat actors searching to obtain privileged accessibility to targeted networks. This tends to make it critical that end users transfer promptly to utilize the most up-to-date fixes to protected in opposition to opportunity threats.
Discovered this short article intriguing? Observe us on Twitter and LinkedIn to study extra exceptional written content we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Mallox Ransomware Exploits Weak MS-SQL Servers to Breach Networks
Mallox Ransomware Exploits Weak MS-SQL Servers to Breach Networks