A China-connected authorities-sponsored menace actor has been observed concentrating on Russian speakers with an up to date version of a remote entry trojan known as PlugX.
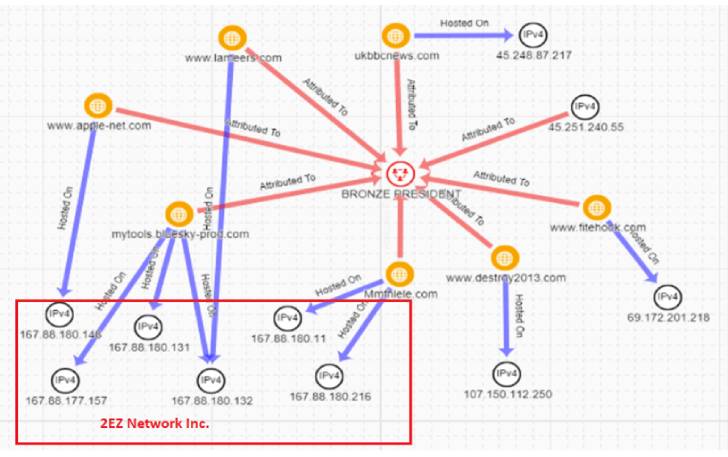
Secureworks attributed the tried intrusions to a danger actor it tracks as Bronze President, and by the broader cybersecurity local community under the monikers Mustang Panda, TA416, HoneyMyte, RedDelta, and PKPLUG.
“The war in Ukraine has prompted numerous countries to deploy their cyber abilities to acquire perception about worldwide events, political machinations, and motivations,” the cybersecurity agency stated in a report shared with The Hacker Information. “This drive for situational recognition often extends to accumulating intelligence from allies and ‘friends.'”
Bronze President, energetic considering that at the very least July 2018, has a record of conducting espionage functions by leveraging custom and publicly accessible tools to compromise, sustain extensive-term access, and acquire info from targets of interest.

Main among the its applications is PlugX, a Windows backdoor that enables menace actors to execute a wide range of commands on infected techniques and which has been used by a number of Chinese state-sponsored actors over the years.
The most up-to-date results from Secureworks recommend an expansion of the exact marketing campaign beforehand specific by Proofpoint and ESET last thirty day period, which has included the use of a new variant of PlugX codenamed Hodur, so labeled owing to its overlaps with a different edition identified as THOR that emerged on the scene in July 2021.
The attack chain commences with a malicious executable named “Blagoveshchensk – Blagoveshchensk Border Detachment.exe” that masquerades as a seemingly legit document with a PDF icon, which, when opened, leads to the deployment of an encrypted PlugX payload from a remote server.
“Blagoveshchensk is a Russian metropolis close to the China border and is home to the 56th Blagoveshchenskiy Pink Banner Border Guard Detachment,” the scientists reported. “This connection implies that the filename was preferred to goal officers or navy personnel common with the area.”
The truth that Russian officers may well have been the focus on of the March 2022 marketing campaign signifies that the menace actor is evolving its techniques in response to the political scenario in Europe and the war in Ukraine.

“Targeting Russian-speaking consumers and European entities suggests that the danger actors have been given current tasking that displays the changing intelligence selection specifications of the [People’s Republic of China],” the scientists stated.
The findings arrive weeks just after one more China-based mostly country-point out team recognised as Nomad Panda (aka RedFoxtrot) was connected with medium self confidence to assaults towards defense and telecom sectors in South Asia by leveraging still an additional version of PlugX dubbed Talisman.
“PlugX has been associated with different Chinese actors in current decades,” Trellix observed last month. “This point raises the query if the malware’s code base is shared amongst diverse Chinese condition-backed teams.”
“On the other hand, the alleged leak of the PlugX v1 builder, as noted by Airbus in 2015, suggests that not all occurrences of PlugX are necessarily tied to Chinese actors,” the cybersecurity enterprise included.
Located this short article appealing? Observe THN on Facebook, Twitter and LinkedIn to browse much more exceptional articles we article.
Some parts of this article are sourced from:
thehackernews.com

 Millions of Java Apps Remain Vulnerable to Log4Shell
Millions of Java Apps Remain Vulnerable to Log4Shell