On August 13, 2016, a hacking device calling alone “The Shadow Brokers” introduced that it had stolen malware equipment and exploits made use of by the Equation Group, a advanced threat actor believed to be affiliated to the Personalized Accessibility Functions (TAO) unit of the U.S. Nationwide Security Agency (NSA).
Though the team has given that signed off pursuing the unparalleled disclosures, new “conclusive” proof unearthed by Check out Place Analysis displays that this was not an isolated incident.
The formerly undocumented cyber-theft took position a lot more than two a long time in advance of the Shadow Brokers episode, the American-Israeli cybersecurity company explained in an exhaustive report released now, ensuing in U.S.-made cyber resources reaching the fingers of a Chinese superior persistent danger which then repurposed them in purchase to attack U.S. targets.

“The caught-in-the-wild exploit of CVE-2017-0005, a zero-day attributed by Microsoft to the Chinese APT31 (aka Zirconium), is in fact a replica of an Equation Team exploit codenamed ‘EpMe,'” Verify Place researchers Eyal Itkin and Itay Cohen reported. “APT31 experienced entry to EpMe’s information, both of those their 32-bits and 64-bits versions, extra than two yrs right before the Shadow Brokers leak.”
The Equation Team, so-named by scientists from cybersecurity business Kaspersky in February 2015, has been linked to a string of attacks affecting “tens of hundreds of victims” as early as 2001, with some of the registered command-and-handle servers courting back again to 1996. Kaspersky known as the team the “crown creator of cyberespionage.”
An Unidentified Privilege Escalation Exploit
Initially disclosed in March 2017, CVE-2017-0005 is a security vulnerability in the Windows Gain32k part that could likely enable elevation of privileges (EoP) in devices operating Windows XP and up to Windows 8. The flaw was claimed to Microsoft by Lockheed Martin’s Laptop Incident Reaction Group.
Examine Level has named the cloned variant “Jian” following a double-edged straight sword utilised in China in the course of the very last 2,500 yrs, referencing its origins as an attack tool made by the Equation Group that was then weaponized to provide as a “double-edged sword” to attack U.S. entities.
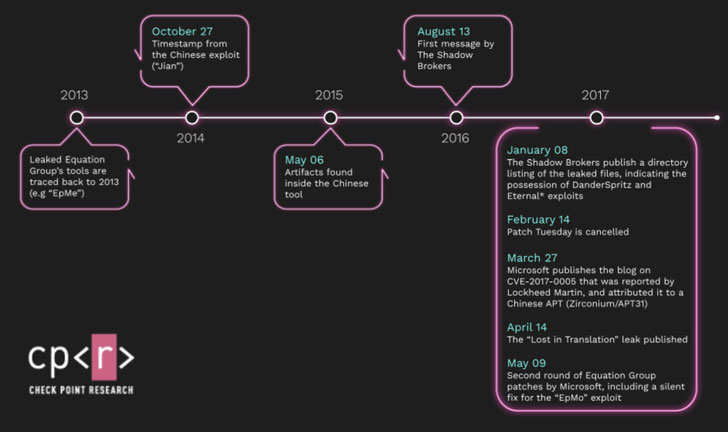 Timeline of the activities detailing the story of EpMe / Jian / CVE-2017-0005
Timeline of the activities detailing the story of EpMe / Jian / CVE-2017-0005
Jian is stated to have been replicated in 2014 and set in operation since at minimum 2015 right up until the fundamental flaw was patched by Microsoft in 2017.
APT31, a condition-sponsored hacking collective, is alleged to perform reconnaissance functions at the behest of the Chinese Federal government, specializing in mental home theft and credential harvesting, with recent strategies targeting U.S. election team with spear-phishing e-mail containing one-way links that would down load a Python-based mostly implant hosted on GitHub, permitting an attacker to upload and download documents as very well as execute arbitrary instructions.
Stating that the DanderSpritz publish-exploitation framework contained 4 different Windows EoP modules, two of which have been zero-days at the time of its improvement in 2013, Examine Issue claimed just one of the zero-days — dubbed “EpMo” — was silently patched by Microsoft “with no obvious CVE-ID” in Might 2017 in response to the Shadow Brokers leak. EpMe was the other zero-working day.
DanderSpritz was among the the a number of exploit equipment leaked by the Shadow Breakers on April 14, 2017, below a dispatch titled “Dropped in Translation.” The leak is most effective identified for publishing the EternalBlue exploit that would later on power the WannaCry and NotPetya ransomware bacterial infections that caused tens of billions of dollars’ worthy of of problems in about 65 countries.
This is the initially time a new Equation Team exploit has come to mild despite EpMo’s source code being publicly obtainable on GitHub because the leak pretty much four decades back.
For its section, EpMo was deployed in machines running Windows 2000 to Windows Server 2008 R2 by exploiting a NULL-Deref vulnerability in Graphics Unit Interface’s (GDI) Consumer Mode Print Driver (UMPD) element.
Jian and EpMe Overlap
“On top of our evaluation of both equally the Equation Team and APT31 exploits, the EpMe exploit aligns beautifully with the facts described in Microsoft’s web site on CVE-2017-0005,” the researchers pointed out. “And if that wasn’t ample, the exploit in truth stopped operating after Microsoft’s March 2017 patch, the patch that dealt with the stated vulnerability.”
Aside from this overlap, equally EpMe and Jian have been located to share an identical memory structure and the similar hard-coded constants, lending credence to the reality that a single of the exploits was most probably copied from the other, or that both parties have been motivated by an not known 3rd-bash.
But so far, there are no clues alluding to the latter, the scientists explained.
Apparently, though EpMe did not assist Windows 2000, Check Point’s evaluation uncovered Jian to have “specific circumstances” for the platform, increasing the possibility that APT31 copied the exploit from the Equation Group at some level in 2014, just before tweaking it to accommodate their needs and ultimately deploying the new version versus targets, like Lockheed Martin.
That Jian, a zero-working day exploit earlier attributed to APT31, is actually a cyber offensive tool made by the Equation Group for the similar vulnerability signifies the value of attribution for both of those strategic and tactical selection creating.
“Even although ‘Jian’ was caught and analyzed by Microsoft at the commencing of 2017, and even although the Shadow Brokers leak exposed Equation Group’s tools virtually 4 several years ago, there is even now a lot one particular can study from analyzing these past activities,” Cohen stated.
“The mere actuality that an overall exploitation module, containing 4 unique exploits, was just lying about unnoticed for 4 decades on GitHub, teaches us about the enormity of the leak close to Equation Group resources.”
Uncovered this posting exciting? Observe THN on Fb, Twitter and LinkedIn to read through a lot more exclusive content material we submit.
Some parts of this article are sourced from:
thehackernews.com


 Concern as Attacker “Breakout” Time Halves in 2020
Concern as Attacker “Breakout” Time Halves in 2020