An ever-evolving and rampant sort of cybercrime that targets e-mails as the possible medium to perform fraud is recognised as Business Email Compromise.
Focusing on professional, governing administration as perfectly as non-profit businesses, BEC can guide to enormous quantities of information loss, security breach, and compromised financial assets.
It is a common misunderstanding that cybercriminals ordinarily lay their concentrate on MNCs and organization-amount corporations. SMEs these times are just as considerably a concentrate on to email fraud as the greater market gamers.
How Can BEC Affect Corporations?
Illustrations of BEC contain complex social engineering assaults like phishing, CEO fraud, pretend invoices, and email spoofing, to title a number of. It can also be termed an impersonation attack whereby an attacker aims to defraud a corporation by posing persons in authoritarian positions. Impersonating men and women like the CFO or CEO, a enterprise associate, or anybody you will blindly place your belief in is what drives these attacks’ results.
February of 2021 captured the functions of the Russian cyber gang Cosmic Lynx as they took a subtle solution in the direction of BEC. The team had previously been linked to conducting in excess of 200 BEC campaigns due to the fact July 2019, concentrating on around 46 countries worldwide, concentrating on large MNCs that have a international presence. With very properly-penned phishing e-mails, they make it not possible for people to differentiate among real and phony messages.
Distant-functioning has manufactured online video conferencing purposes indispensable entities, submit-pandemic. Cybercriminals are having edge of this scenario by sending fraudulent emails that impersonate a notification from the online video conferencing platform, Zoom. This is aimed at stealing login qualifications to carry out enormous business information breaches.
It is crystal clear that the relevance of BEC is promptly surfacing and escalating in the latest occasions, with menace actors coming up with more refined and progressive approaches to get absent with fraud. BEC influences a lot more than 70% of organizations all over the world and qualified prospects to the reduction of billions of pounds every year.
This is why field authorities are coming up with email authentication protocols like DMARC to give a superior stage of safety versus impersonation.
What is Email Authentication?
Email authentication can be referred to as a bevy of procedures deployed to supply verifiable facts about the origin of email messages. This is done by authenticating the area ownership of the mail transfer agent(s) associated in the message transfer.
Very simple Mail Transfer Protocol (SMTP), which is the field typical for email transfer, has no these kinds of in-developed attribute for information authentication. This is why exploiting the lack of security gets exceedingly straightforward for cybercriminals to launch email phishing and area spoofing attacks.
This highlights the want for productive email authentication protocols like DMARC that in fact delivers its promises!
Ways to Avoid BEC with DMARC
Stage 1: Implementation
The to start with step to combating BEC is essentially configuring DMARC for your area. Domain-dependent Message Authentication, Reporting, and Conformance (DMARC) works by using SPF and DKIM authentication standards to validate e-mails sent from your domain.
It specifies to receiving servers how to answer to email messages that fall short both/the two of these authentication checks, giving the area owner management more than the receiver’s reaction. For this reason for Implementing DMARC, you would need to:
- Identify all legitimate email sources authorized for your area
- Publish SPF record in your DNS to configure SPF for your area
- Publish DKIM history in your DNS to configure DKIM for your domain
- Publish DMARC history in your DNS to configure DMARC for your domain
To steer clear of complexities, you can use PowerDMARC’s totally free resources ( free SPF document generator, totally free DKIM document generator, free DMARC file generator) to generate documents with the appropriate syntax promptly and publish in your domain’s DNS.
Step 2: Enforcement
Your DMARC policy can be set to:
- p=none (DMARC at checking only messages failing authentication would however be shipped)
- p=quarantine (DMARC at enforcement messages failing authentication would be quarantined)
- p=reject (DMARC at maximum enforcement messages failing authentication would not be sent at all)
We would suggest you to commence using DMARC with a coverage enabling checking only so that you can maintain a tab on the email movement and delivery issues. Having said that, this kind of a policy wouldn’t supply any security in opposition to BEC.
This is why you would sooner or later require to shift to DMARC enforcement. PowerDMARC helps you seamlessly shift from checking to enforcement in no time with a policy of p=reject, which will assistance specify to obtaining servers that an email sent from a malicious supply using your domain would not be delivered to your recipient’s inbox at all.
Step 3: Monitoring and Reporting
You have set your DMARC coverage at enforcement and have efficiently minimized BEC, but is that enough? The reply is no. You however need an comprehensive and successful reporting mechanism to observe email flow and answer to any shipping and delivery issues. PowerDMARC’s multi-tenant SaaS platform assists you:
- keep in manage of your area
- visually observe authentication results for just about every email, person, and domain registered for you
- acquire down abusive IP addresses that try impersonating your brand
DMARC reports are out there on the PowerDMARC dashboard in two major formats:
- DMARC aggregate stories (out there in 7 diverse sights)
- DMARC forensic reviews (with encryption for increased privateness)
A end result of DMARC implementation, enforcement, and reporting help you substantially minimize the odds of falling prey to BEC frauds and impersonation.
With Anti-Spam Filters, Do I Even now Need to have DMARC?
Indeed! DMARC operates pretty otherwise from your regular anti-spam filters and email security gateways. While these methods generally arrive integrated with your cloud-based mostly email exchanger products and services, they can only provide protection against inbound phishing makes an attempt.
Messages despatched from your area continue to continue to be below the danger of impersonation. This is wherever DMARC techniques in.
Added Ideas for Increased Email Security
Constantly stay less than the 10 DNS Lookup Restrict.
Exceeding the SPF 10 lookup limit can absolutely invalidate your SPF record and cause even authentic e-mails to fail authentication.
In these conditions, if you have your DMARC established to reject, authentic e-mails will fall short to get sent. PowerSPF is your automatic and dynamic SPF document flattener that mitigates SPF permerror by supporting you keep underneath the SPF really hard restrict.
It vehicle-updates netblocks and scans for modifications produced by your email provider suppliers to their IP addresses continuously, with no any intervention from your side.
Be certain TLS Encryption of E-mail in Transit
Whilst DMARC can secure you from social engineering attacks and BEC, you even now will need to gear up in opposition to pervasive checking assaults like Male-in-the-center (MITM).
This can be accomplished by guaranteeing that a link secured about TLS is negotiated involving SMTP servers each individual time an email is sent to your domain.
PowerDMARC’s hosted MTA-STS helps make TLS encryption required in SMTP and will come with a easy implementation process.
Get Experiences on Issues in Email Shipping
You can also enable SMTP TLS reporting to get diagnostic reviews on email shipping issues right after configuring MTA-STS for your domain. TLS-RPT assists you attain visibility into your email ecosystem and far better respond to issues in negotiating a secured relationship primary to shipping failures.
TLS stories are accessible in two sights (mixture reports for each end result and for every sending source) on the PowerDMARC dashboard.
Amplify Your Brand name Recall with BIMI
With BIMI (Manufacturer Indicators for Information Identification), you can acquire your brand name recall to a complete new degree by supporting your recipients visually detect you in their inboxes.
BIMI functions by attaching your unique model logo to just about every email you mail out from your domain. PowerDMARC would make BIMI implementation quick with just 3 easy measures on the user’s aspect.
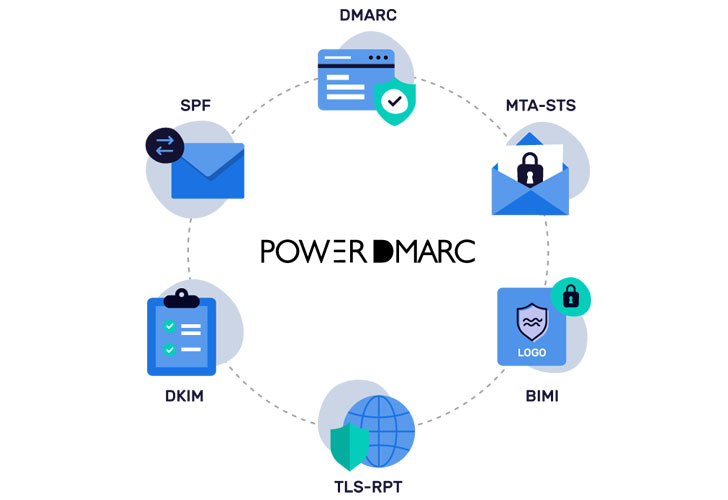
PowerDMARC is your a single-halt place for an array of email authentication protocols, which include DMARC, SPF, DKIM, BIMI, MTA-STS, and TLS-RPT. Indicator up these days to get your absolutely free DMARC Analyzer trial!
Identified this write-up attention-grabbing? Follow THN on Fb, Twitter and LinkedIn to browse extra exceptional content material we post.
Some parts of this article are sourced from:
thehackernews.com


 Chinese Hackers Had Access to a U.S. Hacking Tool Years Before It Was Leaked Online
Chinese Hackers Had Access to a U.S. Hacking Tool Years Before It Was Leaked Online