A formerly undocumented espionage device has been deployed versus selected governments and other critical infrastructure targets as portion of a lengthy-jogging espionage campaign orchestrated by China-linked threat actors since at least 2013.
Broadcom’s Symantec Risk Hunter team characterised the backdoor, named Daxin, as a technologically highly developed malware, enabling the attackers to have out a selection of communications and details-gathering functions aimed at entities in the telecom, transportation, and manufacturing sectors that are of strategic desire to China.
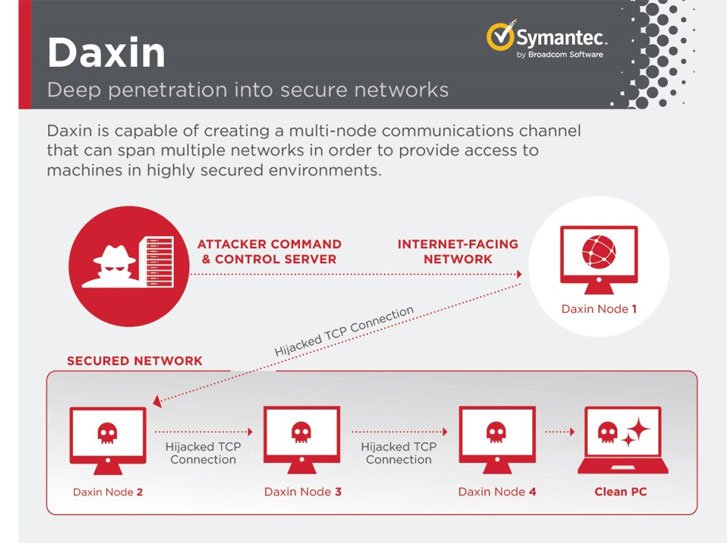
“Daxin malware is a very advanced rootkit backdoor with advanced, stealthy command-and-control (C2) functionality that allows distant actors to talk with secured gadgets not connected specifically to the internet,” the U.S. Cybersecurity and Infrastructure Security Agency (CISA) mentioned in an impartial advisory.

The implant will take the sort of a Windows kernel driver that implements an elaborate communications mechanism that affords the malware a superior diploma of stealth and the ability to discuss to equipment that are bodily disconnected from the internet.
It achieves this by expressly keeping away from launching its personal network expert services, alternatively opting to acquire advantage of genuine TCP/IP companies presently managing on the infected pcs to mix its communications with usual targeted visitors on the target’s network and receive commands from a distant peer.
“These capabilities are reminiscent of Regin,” the scientists pointed out, referring to another complex malware and hacking toolkit attributed to the U.S. Countrywide Security Agency (NSA) for governing administration spying functions back in 2014.
Between the unusual areas of Daxin, moreover producing no suspicious network traffic to keep on being unseen, is its means to relay commands throughout a network of contaminated pcs within the attacked firm, creating a “multi-node communications channel” that permits recurring accessibility to the compromised desktops for extended periods of time.
Although latest intrusions involving the backdoor are stated to have transpired in November 2021, Symantec said it uncovered code-stage commonalities with an more mature piece of malware called Exforel (aka Zala), indicating that Daxin may possibly have been constructed by an actor with entry to the latter’s codebase or that they are the function of the exact team.

The strategies have not been attributed to a single adversary, but a timeline of the attacks demonstrates that Daxin was installed on some of the identical systems where instruments connected with other Chinese espionage actors like Slug were observed. This includes the deployment of both of those Daxin and Owprox malware on a solitary pc belonging to a tech organization in Might 2020.
“Daxin is with no question the most state-of-the-art piece of malware […] utilized by a China-joined actor,” the scientists mentioned. “Thinking about its abilities and the mother nature of its deployed assaults, Daxin seems to be optimized for use against hardened targets, permitting the attackers to burrow deep into a target’s network and exfiltrate details with no increasing suspicions.”
The disclosure comes a 7 days just after China-dependent Pangu Lab outed a “top rated-tier” backdoor known as Bvp47 put to use by the U.S. Nationwide Security Agency for above a 10 years concentrating on as quite a few as 287 organizations in 45 nations located mainly in China, Korea, Japan, Germany, Spain, India, and Mexico.
Located this short article interesting? Follow THN on Facebook, Twitter and LinkedIn to examine a lot more unique material we submit.
Some parts of this article are sourced from:
thehackernews.com


 TikTok is extending the maximum video length to 10 minutes
TikTok is extending the maximum video length to 10 minutes