Check Position is warning of a zero-day vulnerability in its Network Security gateway products that menace actors have exploited in the wild.
Tracked as CVE-2024-24919, the issue impacts CloudGuard Network, Quantum Maestro, Quantum Scalable Chassis, Quantum Security Gateways, and Quantum Spark appliances.
“The vulnerability probably allows an attacker to read specific information on Internet-linked Gateways with distant entry VPN or cell entry enabled,” Examine Issue reported.

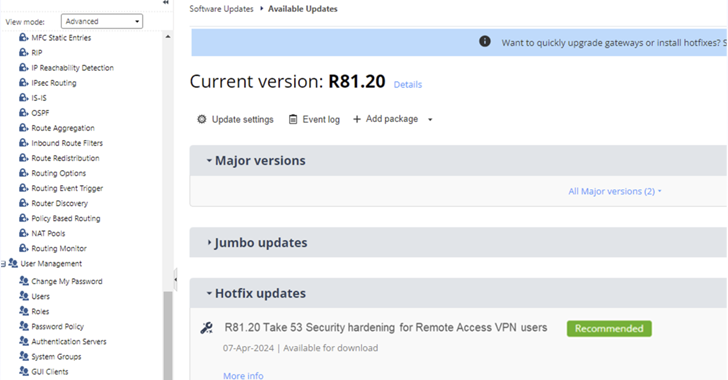
Hotfixes are obtainable in the subsequent versions –
- Quantum Security Gateway and CloudGuard Network Security Variations – R81.20, R81.10, R81, R80.40
- Quantum Maestro and Quantum Scalable Chassis – R81.20, R81.10, R80.40, R80.30SP, R80.20SP
- Quantum Spark Gateways Version – R81.10.x, R80.20.x, R77.20.x
The progress will come times just after the Israeli cybersecurity company warned of assaults concentrating on its VPN gadgets to infiltrate business networks.
“By Might 24, 2024, we discovered a small quantity of login attempts working with aged VPN area-accounts relying on unrecommended password-only authentication process,” it observed previously this week.
This has now been traced back again to a new substantial-severity zero-day discovered in Security Gateways with IPSec VPN, Remote Obtain VPN and the Cell Access program blade.

Test Place did not elaborate on the mother nature of the assaults, but pointed out in an FAQ that the exploitation attempts observed so much focus on “distant obtain on old community accounts with unrecommended password-only authentication” from a “compact quantity of consumers.”
The concentrating on of VPN gadgets represents just the hottest series of attacks to goal network perimeter apps, with related assaults impacting products from Barracuda Networks, Cisco, Fortinet, Ivanti, Palo Alto Networks, and VMware in latest yrs.
“Attackers are determined to gain access to companies more than distant-accessibility setups so they can attempt to explore appropriate business assets and consumers, trying to get for vulnerabilities in get to attain persistence on crucial company property,” Verify Level reported.
Identified this short article appealing? Follow us on Twitter and LinkedIn to examine far more exceptional content we post.
Some parts of this article are sourced from:
thehackernews.com


 Brazilian Banks Targeted by New AllaKore RAT Variant Called AllaSenha
Brazilian Banks Targeted by New AllaKore RAT Variant Called AllaSenha