An espionage-centered menace actor recognised for targeting China, Pakistan, and Saudi Arabia has expanded to set its sights on Bangladeshi government corporations as aspect of an ongoing marketing campaign that commenced in August 2021.
Cybersecurity organization Cisco Talos attributed the activity with average assurance to a hacking team dubbed the Bitter APT centered on overlaps in the command-and-regulate (C2) infrastructure with that of prior strategies mounted by the same actor.
“Bangladesh suits the profile we have defined for this threat actor, beforehand targeting Southeast Asian countries which include China, Pakistan, and Saudi Arabia,” Vitor Ventura, lead security researcher at Cisco Talos, advised The Hacker Information.
“And now, in this most recent marketing campaign, they have widened their get to to Bangladesh. Any new country in southeast Asia being focused by Bitter APT should not be of surprise.”
Bitter (aka APT-C-08 or T-APT-17) is suspected to be a South Asian hacking team enthusiastic largely by intelligence gathering, an procedure that’s facilitated by indicates of malware this sort of as BitterRAT, ArtraDownloader, and AndroRAT. Distinguished targets include things like the strength, engineering, and federal government sectors.
The earliest attacks ended up distributing the cell model of BitterRAT date back again to September 2014, with the actor obtaining a history of leveraging zero-day flaws — CVE-2021-1732 and CVE-2021-28310 — to its benefit and achieve its adversarial targets.
The most current marketing campaign, targeting an elite entity of the Bangladesh authorities, consists of sending spear-phishing emails to large-rating officers of the Fast Action Battalion Unit of the Bangladesh law enforcement (RAB).
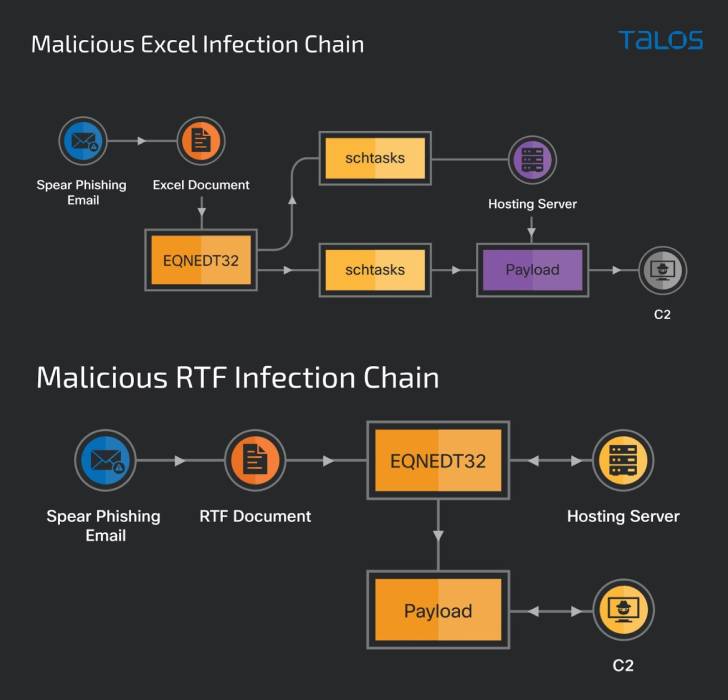
As is normally noticed in other social engineering assaults of this sort, the missives are designed to lure the recipients into opening a weaponized RTF doc or a Microsoft Excel spreadsheet that exploits earlier known flaws in the computer software to deploy a new trojan dubbed “ZxxZ.”
ZxxZ, named so following a separator utilized by the malware when sending details back to the C2 server, is a 32-little bit Windows executable compiled in Visible C++.
“The trojan masquerades as a Windows Security update provider and enables the
destructive actor to complete distant code execution, making it possible for the attacker to complete any other pursuits by putting in other instruments,” the scientists defined.
Though the malicious RTF document exploits a memory corruption vulnerability in Microsoft Office’s Equation Editor (CVE-2017-11882), the Excel file abuses two distant code execution flaws, CVE-2018-0798 and CVE-2018-0802, to activate the an infection sequence.
“Actors typically transform their instruments to keep away from detection or attribution, this is portion of the lifecycle of a menace actor exhibiting its capability and perseverance,” Ventura stated.
Observed this report attention-grabbing? Adhere to THN on Facebook, Twitter and LinkedIn to go through much more exclusive material we publish.
Some parts of this article are sourced from:
thehackernews.com


 Intel Memory Bug Poses Risk for Hundreds of Products
Intel Memory Bug Poses Risk for Hundreds of Products