Google’s Risk Evaluation Group sheds extra gentle on specific credential phishing and malware attacks on the crew of Joe Biden’s presidential marketing and advertising campaign.
Hackers despatched Joe Biden’s presidential internet marketing campaign staffers malicious email messages that impersonated anti-virus computer software method organization McAfee, and built use of a combine of respectable skilled companies (this kind of as Dropbox) to steer obvious of detection. The email messages finished up an endeavor to steal staffers’ skills and infect them with malware.
The unsuccessful advanced persistent threat workforce (APT) assaults on Biden’s marketing marketing campaign ended up first uncovered in June, together with cyberattacks concentrating on Donald Trump’s marketing campaign. On the other hand, the factors of the attacks them selves, and the techniques applied, ended up scant right until at last Google Danger Analysis Group’s (TAG) Friday investigation.
“In 1 individual illustration, attackers impersonated McAfee,” documented experts on Friday. “The targets would be prompted to established up a highly regarded variation of McAfee anti-virus computer software package from GitHub, when malware was concurrently silently set in to the system.”

The marketing campaign was mainly based mostly on email centered again back links that would finally attain malware hosted on GitHub, experts documented. The malware was specially a python-dependent implant using Dropbox for command and management (C2), which right after downloaded would empower the attacker to upload and download info and execute arbitrary directions.
Every and every damaging piece of this attack was hosted on reliable alternatives – earning it much more sturdy for defenders to rely on network alerts for detection, researchers noted.

The McAfee lure produced use of in the Biden cyberattack. Credit ranking: Google
Google attributed the attack on Biden’s marketing campaign workforce to APT 31 (also recognised as Zirconium). In accordance to encounters, this threat actor is tied to the Chinese governing administration.
Outside the house of staffers on the “Joe Biden for President” marketing campaign, APT 31 has also been concentrating on “prominent folks in the throughout the world affairs group, lecturers in intercontinental affairs from far more than 15 universities,” in accordance to earlier Microsoft research.
The risk group’s TTPs incorporate issues like working with web “beacons” that are tied to an attacker-managed area. The group then sends the URL of the domain to targets by making use of email textual content material (or attachment) and persuades them to merely click the relationship through social engineering.
“Although the domain by itself may not have malicious content material, [this] permits Zirconium [APT 31] to check out if a person attempted to accessibility the web internet site,” claimed Microsoft. “For region-issue actors, this is a very very simple way to conduct reconnaissance on skilled accounts to come to a decision if the account is legitimate or the user is lively.”
On the other facet of the coin, the personal email accounts of staffers linked with the “Donald J. Trump for President” marketing marketing campaign have also been specific by a unique menace group named APT 35 (also regarded as Phosphorus and Charming Kitten), which researchers stated operates out of Iran. The Iran-connected hacking group has been acknowledged to use phishing as an attack vector, and in February was uncovered concentrating on community figures in phishing assaults that stole victims’ email-account specifics.
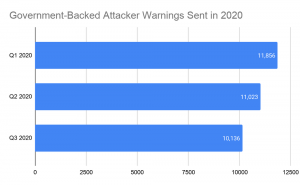
Federal federal government backed attacker warnings sent in 2020. Credit rating score: Google
On the other hand, researchers documented the exceptional news is that there is elevated notice on the threats posed by APTs in the context of the U.S. election. Google for its component stated it removed 14 Google accounts that have been linked to Ukrainian Parliament member Andrii Derkach quickly straight away soon after the U.S. Treasury sanctioned Derkach for attempting to impact the U.S. elections.
“U.S authorities companies have warned about distinctive risk actors, and we have labored cautiously with all these businesses and many others in the tech enterprise to share profits possibilities and intelligence about what we’re viewing in the course of the ecosystem,” stated Google scientists.
With the 2020 U.S. Presidential Election just shut to the corner, cybersecurity issues are beneath the highlight – which include anxieties about the integrity of voting equipment, the expected expansion of mail-in voting due to COVID-19 and disinformation strategies.
Some components of this report are sourced from:
threatpost.com


 The best GPS for your car
The best GPS for your car