Apple on Monday introduced a security update for iOS and iPad to handle a critical vulnerability that it states is remaining exploited in the wild, building it the 17th zero-day flaw the company has resolved in its products due to the fact the start off of the yr.’
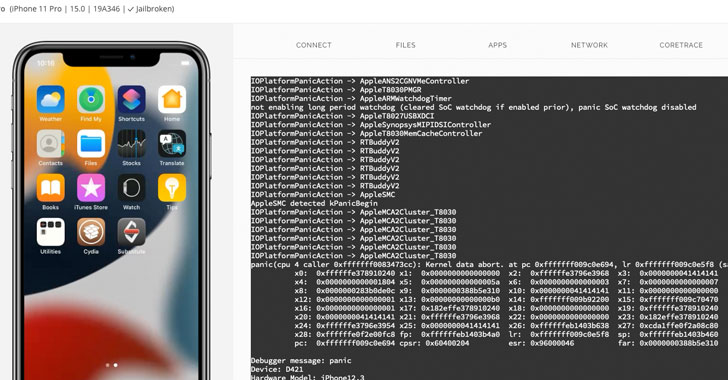
The weakness, assigned the identifier CVE-2021-30883, fears a memory corruption issue in the “IOMobileFrameBuffer” component that could allow an application to execute arbitrary code with kernel privileges. Crediting an nameless researcher for reporting the vulnerability, Apple stated it is “knowledgeable of a report that this issue might have been actively exploited.”
Technical particulars about the flaw and the character of the attacks remain unavailable as however, as is the identification of the danger actor, so as to make it possible for a greater part of the people to apply the patch and prevent other adversaries from weaponizing the vulnerability. The iPhone maker explained it addressed the issue with enhanced memory managing.

Security researcher Saar Amar shared supplemental particulars, and a proof-of-idea (PoC) exploit, noting that “this attack floor is remarkably exciting because it can be available from the app sandbox (so it can be terrific for jailbreaks) and many other procedures, making it a very good candidate for LPEs exploits in chains.”
CVE-2021-30883 is also the next zero-day impacting IOMobileFrameBuffer after Apple tackled a related, anonymously documented memory corruption issue (CVE-2021-30807) in July 2021, elevating the probability that the two flaws could be relevant. With the most recent deal with, the firm has settled a record 17 zero-days to day in 2021 by itself —
- CVE-2021-1782 (Kernel) – A destructive application may well be in a position to elevate privileges
- CVE-2021-1870 (WebKit) – A distant attacker may well be equipped to cause arbitrary code execution
- CVE-2021-1871 (WebKit) – A distant attacker may possibly be ready to bring about arbitrary code execution
- CVE-2021-1879 (WebKit) – Processing maliciously crafted web material may possibly direct to common cross-website scripting
- CVE-2021-30657 (Method Tastes) – A malicious software may bypass Gatekeeper checks
- CVE-2021-30661 (WebKit Storage) – Processing maliciously crafted web content material may direct to arbitrary code execution
- CVE-2021-30663 (WebKit) – Processing maliciously crafted web content material may well direct to arbitrary code execution
- CVE-2021-30665 (WebKit) – Processing maliciously crafted web content material may perhaps guide to arbitrary code execution
- CVE-2021-30666 (WebKit) – Processing maliciously crafted web information may perhaps guide to arbitrary code execution
- CVE-2021-30713 (TCC framework) – A destructive software may well be equipped to bypass Privateness choices
- CVE-2021-30761 (WebKit) – Processing maliciously crafted web material may possibly direct to arbitrary code execution
- CVE-2021-30762 (WebKit) – Processing maliciously crafted web information might guide to arbitrary code execution
- CVE-2021-30807 (IOMobileFrameBuffer) – An application might be able to execute arbitrary code with kernel privileges
- CVE-2021-30858 (WebKit) – Processing maliciously crafted web information may guide to arbitrary code execution
- CVE-2021-30860 (CoreGraphics) – Processing a maliciously crafted PDF may direct to arbitrary code execution
- CVE-2021-30869 (XNU) – A destructive application may be equipped to execute arbitrary code with kernel privileges
Apple iPhone and iPad buyers are really encouraged to update to the newest variation (iOS 15..2 and iPad 15..2) to mitigate the security vulnerability.
Discovered this post intriguing? Stick to THN on Fb, Twitter and LinkedIn to read through far more distinctive written content we write-up.
Some parts of this article are sourced from:
thehackernews.com

 California could ban gas-powered generators and mowers by 2024
California could ban gas-powered generators and mowers by 2024