A seven-yr-previous privilege escalation vulnerability found in the polkit program support could be exploited by a destructive unprivileged nearby attacker to bypass authorization and escalate permissions to the root consumer.
Tracked as CVE-2021-3560 (CVSS score: 7.8), the flaw influences polkit versions involving .113 and .118 and was found out by GitHub security researcher Kevin Backhouse, who reported the issue was introduced in a code dedicate designed on Nov. 9, 2013. Pink Hat’s Cedric Buissart pointed out that Debian-based distributions, centered on polkit .105, are also susceptible.
Polkit (née PolicyKit) is a toolkit for defining and handling authorizations in Linux distributions, and is employed for letting unprivileged processes to converse with privileged processes.
“When a requesting course of action disconnects from dbus-daemon just right before the connect with to polkit_system_bus_title_get_creds_sync begins, the procedure are unable to get a exclusive uid and pid of the procedure and it are unable to verify the privileges of the requesting procedure,” Pink Hat mentioned in an advisory. “The highest threat from this vulnerability is to data confidentiality and integrity as nicely as program availability.”
RHEL 8, Fedora 21 (or later on), Debian “Bullseye,” and Ubuntu 20.04 are some of the common Linux distributions impacted by the polkit vulnerability. The issue has been mitigated in version .119, which was unveiled on June 3.
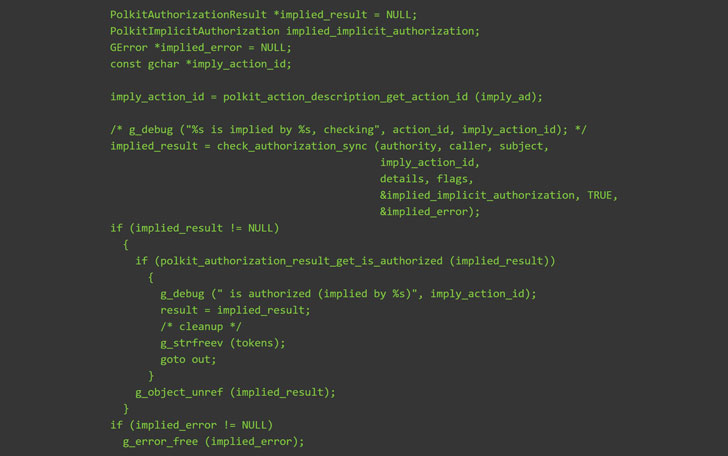
“The vulnerability is astonishingly simple to exploit. All it can take is a handful of instructions in the terminal applying only typical equipment like bash, destroy, and dbus-ship,” explained Backhouse in a generate-up revealed yesterday, incorporating the flaw is brought on by sending a dbus-mail command (say, to produce a new user) but terminating the course of action when polkit is still in the middle of processing the ask for.

“dbus-ship” is a Linux inter-course of action communication (IPC) system which is used to mail a message to D-Bus information bus, permitting communication concerning several processes working concurrently on the similar device. Polkit’s coverage authority daemon is applied as a service linked to the system bus to authenticate qualifications securely.
In killing the command, it triggers an authentication bypass simply because polkit mishandles the terminated information and treats the ask for as while it arrived from a process with root privileges (UID ), thus immediately authorizing the request.
“To result in the susceptible codepath, you have to disconnect at just the right instant,” Backhouse stated. “And due to the fact there are a number of processes included, the timing of that ‘right moment’ may differ from just one run to the future. That is why it commonly will take a number of attempts for the exploit to thrive. I’d guess it can be also the purpose why the bug was not earlier learned.”
Users are inspired to update their Linux installations as shortly as possible to remediate any probable risk arising out of the flaw.
Located this post exciting? Abide by THN on Fb, Twitter and LinkedIn to study additional exceptional written content we post.
Some parts of this article are sourced from:
thehackernews.com

 Microsoft preps for its big Windows event with an 11-minute startup sound remix
Microsoft preps for its big Windows event with an 11-minute startup sound remix