The American Rescue Act is the most recent zeitgeisty lure staying circulated in an email campaign.
Cybercriminals have wasted no time in hopping on the American Rescue Plan – the COVID-19 relief legislation just signed into legislation – as a entice for email-dependent frauds.
According to researchers at Cofense, a marketing campaign commenced circulating in March that capitalized on Americans’ desire in the forthcoming $1,400 aid payments and other aid. The e-mail impersonate the IRS, utilizing the agency’s official brand and a spoofed sender area of IRS[.]gov – and declare to provide an application for financial support. In truth, the e-mail give the Dridex banking trojan.
The email claims, “It is doable to get assist from the federal government of your choice” and then features “quotes” for a pie-in-the-sky litany of terrific (and nonexistent) items – these kinds of as a $4,000 look at, the ability to “skip the queue for vaccination” and free of charge food.
There is a button that states, “Get implement form” – if clicked, end users are taken to a Dropbox account exactly where they see an Excel document that says, “Fill this sort underneath to accept Federal Point out Help.” Having said that, to see this supposed IRS type in its entirety, victims are prompted to help information. If they do, they cause macros that established off the infection chain indirectly, according to Cofense.
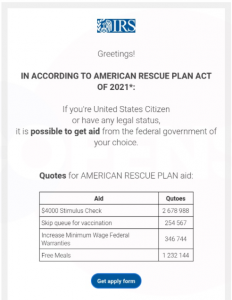
The email lure. Resource: Cofense.
“While static evaluation simply identifies the URLs made use of to download malware in this situation, automatic behavioral investigation could have trouble recognizing the activity as malicious simply because it does not use macros to right download malware or operate a PowerShell script,” Cofense scientists defined, in a putting up on Tuesday. “The macros applied by the .XLSM information drop an .XSL file to disk, and then use a Windows Management Instrumentation (WMI) question to get technique info.”
WMI is a subsystem of PowerShell that offers admins obtain to system monitoring equipment, including the potential to ask for information and facts about nearly anything that exists on a given personal computer – this kind of as which documents and applications are present. It can also ask for responses to these queries to be presented in a particular structure.
“The WMI query used in this case…demands that the dropped .XSL file be employed to structure the reaction to the question,” researchers wrote. “This formatting directive makes it possible for JavaScript contained in the .XSL file to be executed by way of WMI and obtain malware, preventing the much more commonly found strategies by using PowerShell.”
What is the Dridex Banking Trojan?
Considering the fact that its initial physical appearance in 2011, the Dridex malware (a.k.a. Bugat and Cridex) has been deployed by using phishing e-mails and generally targets banking information and facts. Right after capturing banking credentials, it endeavors to make unauthorized digital resources transfers from unknowing victims’ financial institution accounts.
By 2015, the malware was one of the most prevalent money trojans in the wild, specifically when it came to focusing on company employees while later versions of the malware ended up built with the added perform of aiding in the set up of ransomware. It has also enhanced its obfuscation capabilities above time.
In December 2019, authorities cracked down on Russian-speaking cybercrime group Evil Corp. with sanctions and prices versus its leader, Maksim Yakubets, known for his lavish life-style. U.S. authorities are nonetheless offering up to $5 million for facts major to his arrest they allege that Yakubets and Evil Corp. have stolen millions of bucks from victims utilizing the Dridex banking trojan and Zeus malware.
How to Reduce the Phish
This newest marketing campaign is convincing, scientists stated – to a sure extent. One particular sneaky trick the attackers use is that the email area is lRS[.]gov – but with a decrease-case ‘L’ instead than an higher-scenario ‘I.’
Nonetheless, phrasing like “Federal Point out Aid” (federal and condition aid are two distinctive points) and off grammar these kinds of as “the federal governing administration of your choice” ought to established off warning bells.
“A near evaluation of the email reveals a couple suspicious features,” according to Cofense. “The phrasing inside the document, while not clearly as undesirable as anything car-translated from a further language, however has some faults that are unexpected from what purports to be a federal government conversation.”
They added, “Despite individuals issues, this campaign is probable to entice the common user who’s in a hurry to find out more about the rescue plan.”
To keep away from getting a sufferer, users must hone their phishing-recognition competencies, these as scanning for slight differences in between reputable and spoofed domains. And for firms, “as a standard rule, WMI and PowerShell should be thoroughly monitored on most workstations,” Cofense recommended.
Examine out our free upcoming live webinar events – exclusive, dynamic discussions with cybersecurity experts and the Threatpost local community:
- March 24: Economics of -Day Disclosures: The Superior, Undesirable and Unsightly (Discover extra and register!)
- April 21: Underground Marketplaces: A Tour of the Dark Overall economy (Find out additional and register!)
Some parts of this article are sourced from:
threatpost.com


 Dropbox to Make Password Manager Feature Free for All Users
Dropbox to Make Password Manager Feature Free for All Users