The cyber espionage team recognised as Bahamut has been attributed as at the rear of a highly targeted campaign that infects buyers of Android units with destructive applications made to extract delicate data.
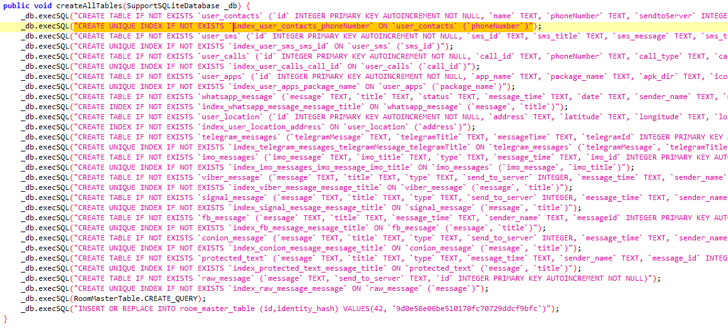
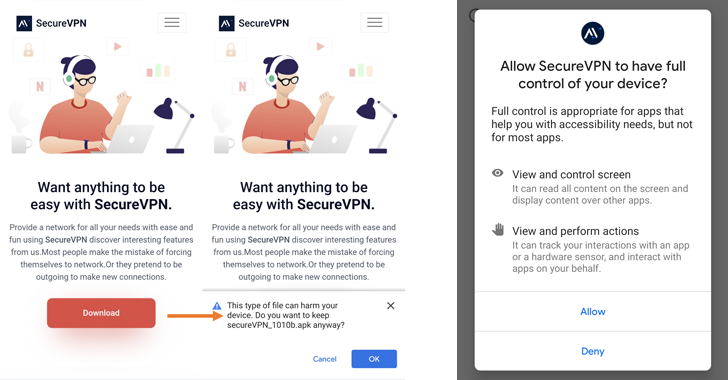
The exercise, which has been active given that January 2022, entails distributing rogue VPN apps through a bogus SecureVPN website established up for this objective, Slovak cybersecurity company ESET explained in a new report shared with The Hacker Information.
At minimum eight distinct variants of the spyware apps have been identified to day, with them staying trojanized variations of legit VPN applications like SoftVPN and OpenVPN.
The tampered applications and their updates are pushed to people through the fraudulent web site. It is really also suspected that the targets are thoroughly chosen, due to the fact launching the application needs the sufferer to enter an activation vital to help the attributes.
This implies the use of an undetermined distribution vector, despite the fact that previous proof demonstrates that it could choose the variety of spear-phishing emails, SMS messages, or direct messages on social media applications.
The activation important system is also created to connect with an actor-managed server, effectively avoiding the malware from staying unintentionally triggered ideal right after launch on a non-qualified user machine.
Bahamut was unmasked in 2017 by Bellingcat as a hack-for-retain the services of operation focusing on authorities officers, human rights groups, and other higher-profile entities in South Asia and the Center East with destructive Android and iOS applications to spy on its victims.
“Possibly the most unique part of Bahamut’s tradecraft that BlackBerry discovered is the group’s use of authentic, painstakingly crafted internet sites, applications and personas,” BlackBerry observed in Oct 2020.
Earlier this yr, Cyble detailed two sets of phishing attacks orchestrated by the team to press counterfeit Android apps masquerading as chat purposes.
The latest wave follows a similar trajectory, tricking customers into installing seemingly innocuous VPN apps that can exfiltrate a huge swathe of information and facts, including documents, speak to lists, SMSes, phone get in touch with recordings, areas, and messages from WhatsApp, Facebook Messenger, Sign, Viber, Telegram, and WeChat.
“The data exfiltration is accomplished by using the keylogging operation of the malware, which misuses accessibility solutions,” ESET researcher Lukáš Štefanko claimed.
In a indicator that the campaign is nicely managed, the menace actor at first packaged the destructive code in just the SoftVPN application, right before transferring to OpenVPN, a change spelled out by the truth that the actual SoftVPN application stopped working and it was no for a longer period doable to set up a VPN connection.
“The cellular marketing campaign operated by the Bahamut APT team is nonetheless energetic it employs the exact approach of distributing its Android spy ware apps through web-sites that impersonate or masquerade as legitimate products and services, as has been viewed in the previous,” Štefanko added.
Found this write-up fascinating? Stick to THN on Facebook, Twitter and LinkedIn to browse extra exceptional content material we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Russian DDoS Briefly Downs European Parliament Site
Russian DDoS Briefly Downs European Parliament Site