Picture Resource: Toptal
The infamous Emotet malware has turned to deploy a new module developed to siphon credit card information and facts stored in the Chrome web browser.
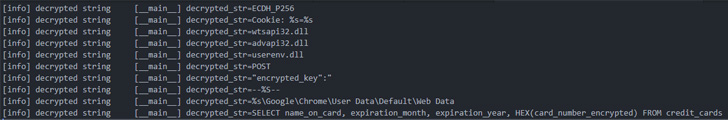
The credit rating card stealer, which exclusively singles out Chrome, has the capability to exfiltrate the collected information to various distant command-and-command (C2) servers, according to company security company Proofpoint, which observed the part on June 6.
The growth comes amid a spike in Emotet exercise since it was resurrected late very last yr subsequent a 10-thirty day period-extensive hiatus in the wake of a regulation enforcement procedure that took down its attack infrastructure in January 2021.
Emotet, attributed to a threat actor recognized as TA542 (aka Mummy Spider or Gold Crestwood), is an highly developed, self-propagating and modular trojan that is sent by means of email campaigns and is utilized as a distributor for other payloads these kinds of as ransomware.

As of April 2022, Emotet is still the most preferred malware with a worldwide influence of 6% of organizations throughout the world, followed by Formbook and Agent Tesla, per Check out Position, with the malware testing out new delivery approaches working with OneDrive URLs and PowerShell in .LNK attachments to get all-around Microsoft’s macro limits.
The continual advancement in Emotet-associated threats is substantiated further more by the truth that the quantity of phishing emails, generally hijacking now current correspondence, grew from 3,000 in February 2022 to about 30,000 in March focusing on corporations in various countries as part of a mass-scale spam marketing campaign.
Stating that Emotet exercise have “shifted to a bigger equipment” in March and April 2022, ESET mentioned that detections jumped a 100-fold, registering a expansion of above 11,000% for the duration of the 1st 4 months of the 12 months when when compared to the previous a few-month interval from September to December 2021.
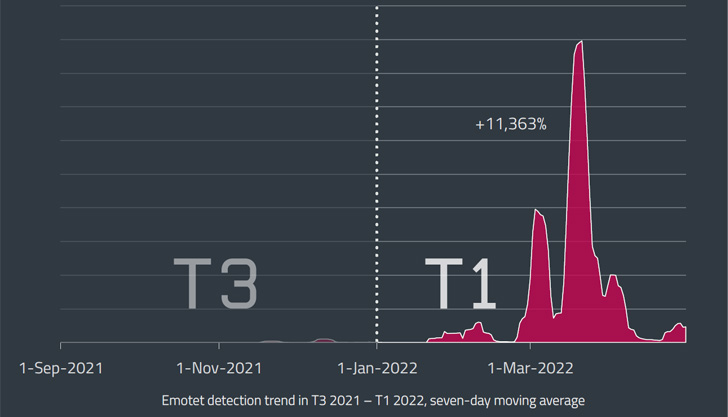
Some of the frequent targets due to the fact the botnet’s resurrection have been Japan, Italy, and Mexico, the Slovak cybersecurity enterprise pointed out, introducing the major wave was recorded on March 16, 2022.
“The measurement of Emotet’s most up-to-date LNK and XLL strategies was substantially scaled-down than individuals distributed by using compromised DOC files found in March,” Dušan Lacika, senior detection engineer at Dušan Lacika, stated.
“This suggests that the operators are only working with a fraction of the botnet’s opportunity whilst tests new distribution vectors that could substitute the now disabled-by-default VBA macros.”
The results also come as researchers from CyberArk shown a new method to extract plaintext credentials instantly from memory in Chromium-based mostly web browsers.
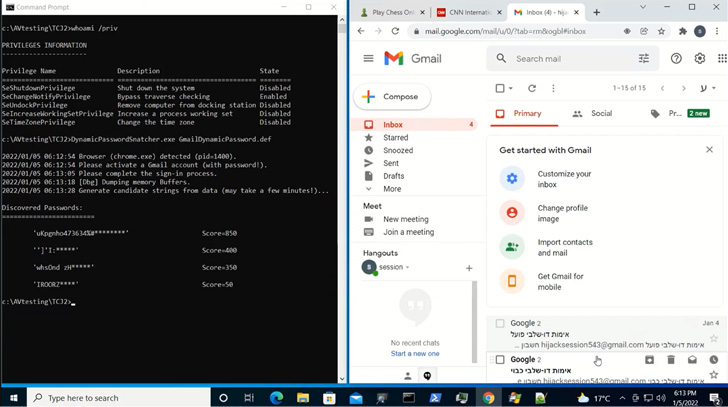
“Credential details is saved in Chrome’s memory in cleartext format,” CyberArk’s Zeev Ben Porat explained. “In addition to knowledge that is dynamically entered when signing into unique web apps, an attacker can bring about the browser to load into memory all the passwords that are saved in the password supervisor.”
This also contains cookie-similar information this sort of as session cookies, most likely enabling an attacker to extract the details and use it to hijack users’ accounts even when they are safeguarded by multi-aspect authentication.
Discovered this post attention-grabbing? Observe THN on Fb, Twitter and LinkedIn to examine much more unique information we post.
Some parts of this article are sourced from:
thehackernews.com


 The best camera and photography gift ideas for dad
The best camera and photography gift ideas for dad