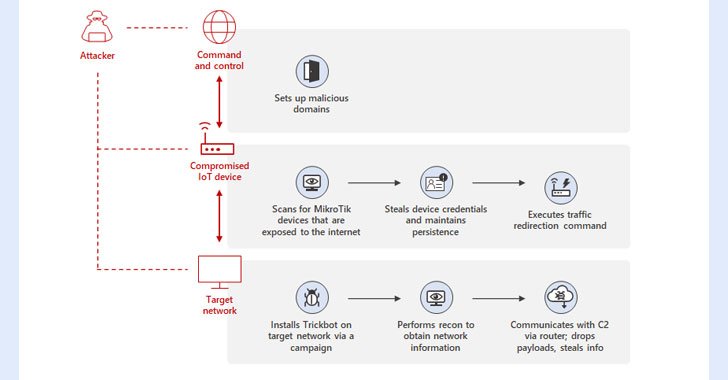
Microsoft on Wednesday in-depth a earlier undiscovered method place to use by the TrickBot malware that consists of making use of compromised Internet of Matters (IoT) devices as a go-in between for establishing communications with the command-and-control (C2) servers.
“By utilizing MikroTik routers as proxy servers for its C2 servers and redirecting the targeted visitors through non-typical ports, TrickBot adds yet another persistence layer that aids malicious IPs evade detection by standard security programs,” Microsoft’s Defender for IoT Analysis Staff and Danger Intelligence Centre (MSTIC) reported.

TrickBot, which emerged as a banking trojan in 2016, has progressed into a advanced and persistent threat, with its modular architecture enabling it to adapt its practices to accommodate diverse networks, environments, and gadgets as properly as provide entry-as-a-service for up coming-phase payloads like Conti ransomware.
The expansion to TrickBot’s capabilities will come amid stories of its infrastructure heading offline, even as the botnet has continuously refined its attributes to make its attack framework tough, evade reverse engineering, and keep the security of its C2 servers.

Specifically, the new process determined by MSTIC consists of leveraging hacked IoT gadgets this kind of as routers from MikroTik to “build a line of communication amongst the TrickBot-influenced gadget and the C2 server.”

This also entails breaking into the routers by making use of a blend of techniques, specifically default passwords, brute-power assaults, or exploiting a now-patched flaw in MikroTik RouterOS (CVE-2018-14847), adopted by changing the router’s password to sustain obtain.
In the upcoming step, the attackers then issue a network tackle translation (NAT) command which is made to redirect targeted traffic in between ports 449 and 80 in the router, creating a path for the TrickBot-infected hosts to communicate with the C2 server.
“As security options for standard computing products continue on to evolve and boost, attackers will explore alternate ways to compromise focus on networks,” the scientists claimed. “Attack tries versus routers and other IoT products are not new, and getting unmanaged, they can effortlessly be the weakest back links in the network.”
Observed this write-up fascinating? Adhere to THN on Facebook, Twitter and LinkedIn to browse a lot more special material we publish.
Some parts of this article are sourced from:
thehackernews.com

 Google Classroom will help teachers monitor progress with practice sets
Google Classroom will help teachers monitor progress with practice sets