An IRC (Internet Relay Chat) bot strain programmed in GoLang is staying made use of to launch distributed denial-of-services (DDoS) assaults targeting users in Korea.
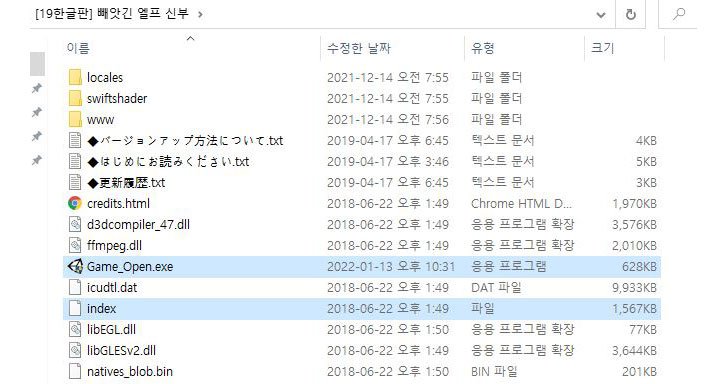
“The malware is being distributed underneath the guise of adult game titles,” scientists from AhnLab’s Security Emergency-response Heart (ASEC) reported in a new report printed on Wednesday. “Additionally, the DDoS malware was installed through downloader and UDP RAT was made use of.”

The attack works by uploading the malware-laced game titles to webhards, which refers to a web tough generate or a distant file hosting provider, in the sort of compressed ZIP archives that, when opened, involves an executable (“Game_Open.exe”) that’s orchestrated to operate a malware payload apart from launching the actual sport.
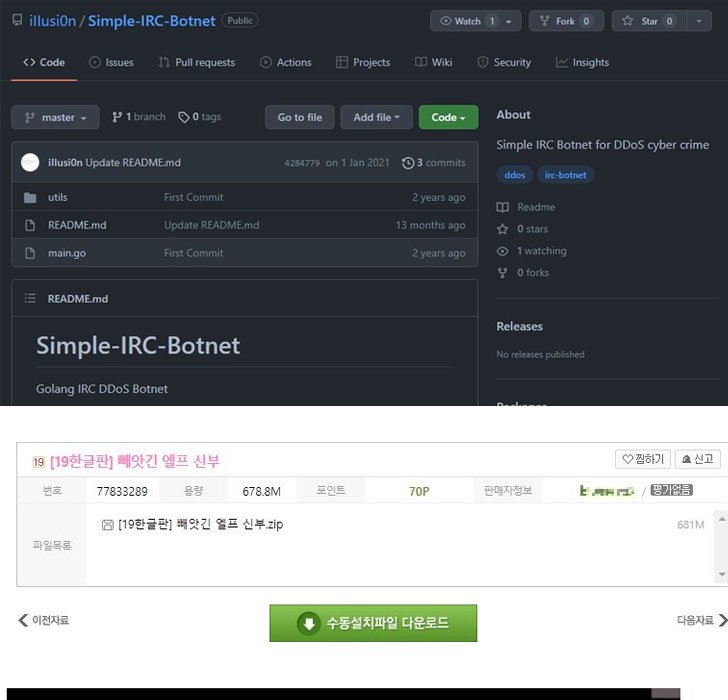
This payload, a GoLang-centered downloader, establishes connections with a remote command-and-handle (C&C) server to retrieve further malware, which include an IRC bot that can accomplish DDoS assaults.
“It is also a variety of DDoS Bot malware, but it works by using IRC protocols to connect with the C&C server,” the scientists thorough. “As opposed to UDP Rat that only supported UDP Flooding assaults, it can also assistance assaults this kind of as Slowloris, Goldeneye, and Hulk DDoS.”
GoLang’s small growth issues and its cross-system assistance have manufactured the programming language a preferred alternative for risk actors, the scientists added.
“The malware is becoming distributed actively by means of file sharing internet websites this kind of as Korean webhards,” AhnLab reported. “As this kind of, caution is encouraged when approaching executables downloaded from a file-sharing web-site. It is propose[ed] for the users to obtain products from the official web-sites of developers.”
Found this article exciting? Follow THN on Facebook, Twitter and LinkedIn to examine far more exclusive written content we submit.
Some parts of this article are sourced from:
thehackernews.com


 Ukraine: Recent Cyber Attacks Part of Wider Plot to Sabotage Critical Infrastructure
Ukraine: Recent Cyber Attacks Part of Wider Plot to Sabotage Critical Infrastructure