Analysts warn that the attack group, now recognized as ‘Earth Centaur,’ is honing its assaults to go following transportation and governing administration organizations.
They’ve been an active risk team given that 2011, but a modern uptick in action from Earth Centaur – formerly acknowledged as Tropic Trooper – aimed precisely at transportation and govt companies is setting off alarm bells among the industry experts.
Trend Micro scientists have been monitoring Tropic Trooper’s resurgence, which started in July 2020 and has lately incorporated troubling attempts to breach delicate transportation-connected data like flight schedules and financial arranging paperwork.
The analysts had been capable to attribute the new Earth Centaur exercise to Tropic Trooper right after locating related code in configuration decoding, they noted.
“Currently, we have not identified significant injury to these victims as caused by the menace team,” Development Micro’s analysts spelled out. “However, we imagine that it will carry on amassing internal info from the compromised victims and that it is simply just waiting for an prospect to use this details.”
Earth Centaur’s Methods
The group’s hallmark practices, tactics and treatments (TTPs) include things like savvy purple teamwork, the researchers noted. Earth Centaur is proficient at bypassing security and lingering undetected, the report added.
“Depending on the concentrate on, it takes advantage of backdoors with various protocols, and it can also use the reverse proxy to bypass the checking of network security programs. The utilization of the open up-source frameworks also allows the group to establish new backdoor variants proficiently. ”
Typically, the risk team breaches the target units by means of a vulnerable Trade or Internet Facts Products and services (IIS) server, followed by dropping backdoors like ChiserClient and SmileSvr, the report reported. Pattern Micro in-depth the intrusion levels in the chart shown down below.
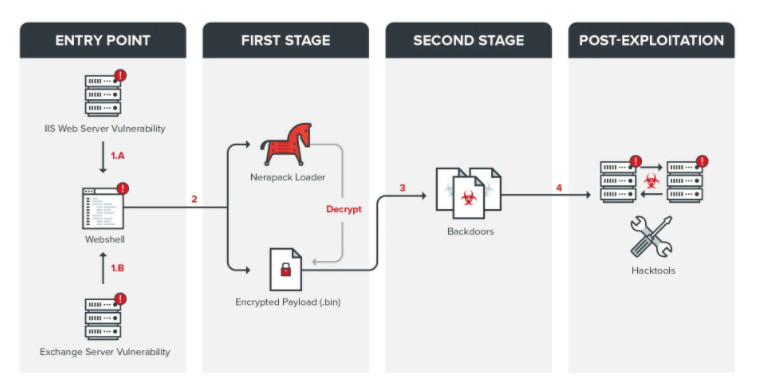
Supply: Trend Micro.
From there, a custom variation of Gh0st RAT sets out to assemble data from active periods on the host, according to the researchers. Immediately after that is accomplished, the attackers go by means of the compromised organization’s intranet and exfiltrate beneficial knowledge.
Trend Micro mentioned Earth Centaur utilised PowerShell to down load Rclone, an exfiltration software that copies data to various clouds.
“Based on past knowledge, Rclone has often been applied in ransomware attacks to exfiltrate stolen information,” the report added. “However, it appears to be that at this time, it is not only applied in ransomware attacks but also in [advanced persistent threat, or APT] assaults.”
Credential dumping was another widespread tactic Development Micro observed with the Tropic Troopers transportation marketing campaign.
“We also noticed that the team utilized a number of legitimate applications to dump credentials on compromised machines,” the report extra. “It created excellent use of these resources to realize its purpose and retain its procedure concealed and unobstructive.”
Tropic Trooper/Earth Centaur has also made its possess, bespoke resource for cleaning up its tracks that deletes event logs on the focused computer.
Tropic Trooper “uses backdoors with unique protocols, which are deployed relying on the target,” Trend Micro’s scientists found. “It also has the capability to establish customized equipment to evade security checking in different environments, and it exploits susceptible web-sites and utilizes them as C&C servers. ”
The rise of the menace actor’s curiosity in the transportation and government sector coincides with the November passage of the Infrastructure Deal, which claims gargantuan investments throughout the transportation sector, such as $39 billion to modernize transit, $89.9 billion for public transit, $25 billion for airports, $66 billion in rail funding and substantially a lot more.
Billions in hard cash are about to flood the transportation sector by way of the government, and Earth Centaur seems correctly poised to hard cash in.
Check out our free of charge future are living and on-demand from customers on the net city halls – one of a kind, dynamic conversations with cybersecurity specialists and the Threatpost neighborhood.
Some parts of this article are sourced from:
threatpost.com


 TikTok is testing a desktop livestreaming app
TikTok is testing a desktop livestreaming app