The wormable malware spread from Android to Android by sending messages presenting cost-free Netflix Premium for 60 days.
Malware disguised as a Netflix application, lurking on the Google Engage in retailer, unfold by means of WhatsApp messages, researchers have uncovered.
According to a Test Stage Investigate analysis introduced on Wednesday, the malware masqueraded as an application known as “FlixOnline,” which marketed by means of WhatsApp messages promising “2 Months of Netflix High quality Totally free Any place in the Globe for 60 times.” But when mounted, the malware sets about thieving details and qualifications.
The malware was created to pay attention for incoming WhatsApp messages and automatically respond to any that the victims acquire, with the content of the response crafted by the adversaries. The responses tried to entice other folks with the offer of a free of charge Netflix assistance, and contained back links to a fake Netflix web site that phished for qualifications and credit history card facts, researchers mentioned.
“The app turned out to be a pretend company that claims to allow for buyers to watch Netflix content from about the environment on their mobiles,” according to the analysis. “However, instead of making it possible for the mobile user to see Netflix material, the software is basically intended to keep track of a user’s WhatsApp notifications, sending automated replies to a user’s incoming messages using written content that it receives from a distant server.”
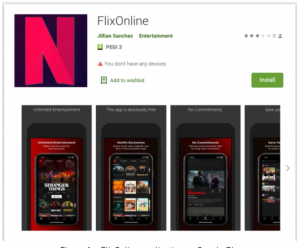
The phony app in Google Perform, featuring the Netflix symbol. Resource: Check out Place.
The malware was also capable to self-propagate, sending messages to users’ WhatsApp contacts and teams with back links to the bogus application. To that conclude, the automated messages go through, “2 Months of Netflix High quality Totally free at no value For Motive OF QUARANTINE (CORONA VIRUS)* Get 2 Months of Netflix Quality Cost-free everywhere in the environment for 60 times. Get it now Here [Bitly link].”
Around the system of two months that the application was reside on Google Engage in, the malware racked up 500 victims, according to Test Level. The organization alerted Google to the malware, which took the app down. Having said that, “the malware family is most likely listed here to continue to be and may possibly return hidden in a different app,” researchers warned.
“The malware’s procedure is fairly new and ground breaking,” Aviran Hazum, supervisor of Cell Intelligence at Verify Point, reported in the assessment. “The technique listed here is to hijack the connection to WhatsApp by capturing notifications, along with the capacity to get predefined actions, like ‘dismiss’ or ‘reply’ via the Notification Manager. The reality that the malware was capable to be disguised so simply and ultimately bypass Play Store’s protections raises some critical red flags.”
FlixOnline Intercepts WhatsApp Notifications
As soon as the software is downloaded from the Perform Shop and mounted, it requests a few distinct permissions, according to the Check out Point analysis: Overlay, Battery Optimization Dismiss and Notification Listener.
Overlay allows a malicious application to produce new windows on prime of other apps, observed the scientists.
“This is normally requested by malware to make a faux log-in screen for other applications, with the goal of stealing victim’s credentials,” they discussed.
The Dismiss Battery Optimizations authorization in the meantime stops the malware from remaining shut down when the phone goes into idle mode, as Android apps commonly do in get to preserve battery power. This allowed the “FlixOnline” app to repeatedly operate, listening and sending pretend messages in the track record even if the phone is dormant.
Most importantly, the Notification Listener permission makes it possible for the malware to entry all notifications related to messages despatched to the product, with “the means to routinely carry out selected actions these kinds of as ‘dismiss’ and ‘reply’ to messages been given on the product,” in accordance to Test Level.
Soon after the permissions are granted, the malware shows a landing webpage it gets from the command-and-regulate server (C2), and it deletes its icon off the home monitor. From there, it periodically pings the C2 for configuration updates.
“The assistance can attain these plans by making use of numerous procedures,” according to the assessment. “For instance, the support can be activated by the installation of the software and by an alarm registered as the BOOT_Done motion, which is named following the gadget has concluded the boot process.”
When it arrives to parsing the WhatsApp messages, the malware takes advantage of a purpose known as OnNotificationPosted to verify for the package title of the application generating a offered notification. If that application is WhatsApp, the malware will then “process” the notification, in accordance to Look at Place. That is composed of canceling the notification (to cover it from the user), and then reading the title and information of the notification received.
“Next, it searches for the ingredient that is responsible for inline replies, which is employed to send out the reply working with the payload gained from the C2 server,” scientists spelled out.
Malware-Laced Apps on Google Play
The official Android app retailer is sad to say no stranger to destructive and trojanized apps. In March for instance, 9 malicious apps had been identified on Google Participate in, harboring a malware dropper that paves the way for attackers to remotely steal fiscal information from Android telephones. And in January, Google booted 164 apps, collectively downloaded a whole of 10 million situations, simply because they ended up providing disruptive ads.
Meanwhile past yr, the Joker malware ongoing to plague Google Play applications. Joker, which has been all around considering that 2017, is a cell trojan specializing in a kind of billing fraud acknowledged as “fleeceware.” The Joker applications publicize on their own as reputable applications (like online games, wallpapers, messengers, translators and picture editors, primarily). When put in, they simulate clicks and intercept SMS messages to subscribe victims to undesirable, paid premium services. The apps also steal SMS messages, contact lists and gadget data.
How Can Android Customers Defend On their own?
To guard from this style of malware, customers should really be cautious of down load inbound links or attachments obtained through WhatsApp or other messaging applications, even when they appear to appear from reliable contacts or messaging groups, Look at Place observed.
If end users find on their own with a phony app, they ought to right away get rid of the suspect software from the product, and continue to change all passwords.
At any time surprise what goes on in underground cybercrime forums? Find out on April 21 at 2 p.m. ET for the duration of a FREE Threatpost occasion, “Underground Marketplaces: A Tour of the Dark Economic system.” Industry experts will acquire you on a guided tour of the Dark Web, including what’s for sale, how much it expenses, how hackers get the job done jointly and the newest instruments accessible for hackers. Register here for the Wed., April 21 Stay occasion.
Some parts of this article are sourced from:
threatpost.com


 Chemical Weapon Shopping Sends Dark Web User to Prison
Chemical Weapon Shopping Sends Dark Web User to Prison