Researchers have demonstrated a novel class of assaults that could enable a negative actor to potentially circumvent existing countermeasures and split the integrity defense of digitally signed PDF documents.
Called “Shadow attacks” by teachers from Ruhr-University Bochum, the approach utilizes the “monumental adaptability supplied by the PDF specification so that shadow documents stay regular-compliant.”
The conclusions have been introduced yesterday at the Network and Dispersed Method Security Symposium (NDSS), with 16 of the 29 PDF viewers tested — together with Adobe Acrobat, Foxit Reader, Great PDF, and Okular — uncovered vulnerable to shadow assaults.
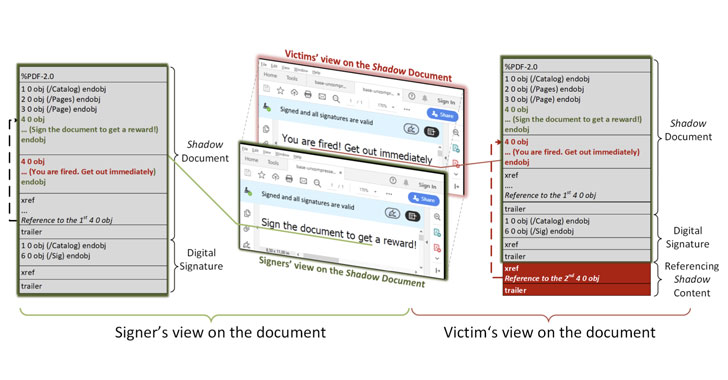
To have out the attack, a destructive actor generates a PDF document with two different contents: just one which is the material that is predicted by the bash signing the document, and the other, a piece of hidden articles that receives shown as soon as the PDF is signed.
“The signers of the PDF receive the document, evaluate it, and sign it,” the researchers outlined. “The attackers use the signed document, modify it slightly, and send out it to the victims. After opening the signed PDF, the victims check no matter whether the digital signature was properly confirmed. Having said that, the victims see diverse content than the signers.”

In the analog earth, the attack is equivalent to deliberately leaving vacant spaces in a paper document and obtaining it signed by the anxious party, finally making it possible for the counterparty to insert arbitrary information in the areas.
Shadow attacks develop on a equivalent risk devised by the researchers in February 2019, which found that it was feasible to alter an current signed document without the need of invalidating its signature, therefore creating it probable to forge a PDF doc.
Although vendors have due to the fact applied security actions to take care of the issue, the new analyze aims to prolong this attack design to ascertain the likelihood that an adversary can modify the visible content material of a digitally signed PDF without having invalidating its signature, assuming that they can manipulate the PDF ahead of it is signed.
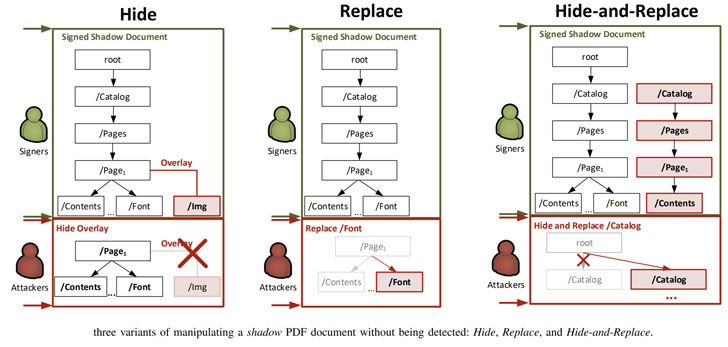
At its core, the attacks leverage “harmless” PDF characteristics which do not invalidate the signature, these as “incremental update” that will allow for producing alterations to a PDF (e.g., filling out a type) and “interactive types” (e.g., text fields, radio buttons, and so on.) to hide the malicious written content behind seemingly innocuous overlay objects or directly swap the authentic information after it is really signed.
A 3rd variant named “hide and exchange” can be utilized to merge the aforementioned strategies and modify the contents of an complete document by merely changing the item references in the PDF.
“The attacker can establish a complete shadow document influencing the presentation of just about every site, or even the complete quantity of pages, as nicely as each individual object contained therein,” the scientists mentioned.
Put simply just, the notion is to generate a kind, which exhibits the identical value prior to and following signing, but a fully unique set of values write-up an attacker’s manipulation.
To exam the assaults, the researchers have revealed two new open up-source instruments called PDF-Attacker and PDF-Detector that can be utilized to crank out shadow documents and check a PDF for manipulation in advance of it really is signed and right after it’s been altered.
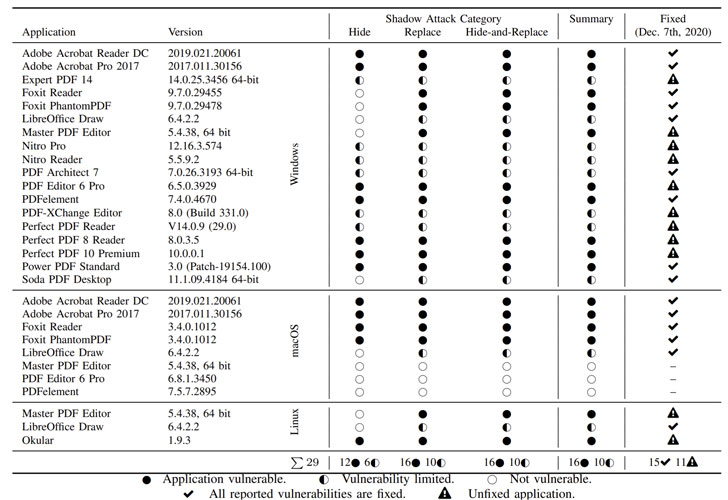
The flaws — tracked as CVE-2020-9592 and CVE-2020-9596 — have been considering that dealt with by Adobe in an update unveiled on Might 12, 2020. As of December 17, 2020, 11 of the 29 analyzed PDF applications remain unpatched.
This is not the first time PDF security has occur underneath the lens. The researchers have formerly shown procedures to extract contents of a password-safeguarded PDF file by taking benefit of partial encryption supported natively by the PDF specification to remotely exfiltrate material as soon as a user opens that doc.
Individually, the researchers final month uncovered another set of 11 vulnerabilities impacting the PDF common (CVE-2020-28352 by way of CVE-2020-28359, and from CVE-2020-28410 to CVE-2020-28412) that could lead to denial-of-support, data disclosure, info manipulation assaults, and even arbitrary code execution.
Identified this report intriguing? Abide by THN on Fb, Twitter and LinkedIn to read through more unique articles we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Instagram adds more help to support those with eating disorders
Instagram adds more help to support those with eating disorders