A patch in the NextGen Gallery WordPress plugin fixes critical and significant-severity cross-internet site ask for forgery flaws.
Researchers are urging WordPress web sites that employ the NextGen Gallery plugin to implement a patch addressing critical and high-severity flaws.
The NextGen Gallery plugin, which is installed on 800,000 WordPress websites, lets web-sites to add pictures in batch quantities, import metadata and edit image thumbnails. Researchers identified two cross-web page request forgery (CSRF) flaws – just one critical and one particular substantial-severity – in the plugin.
A patch was unveiled for flaws in model 3.5., on Dec. 17. In the 1st community disclosure of particulars of the flaw, unveiled Monday, scientists urged website homeowners who use the plugin to guarantee they are up to date.
“Exploitation of these vulnerabilities could lead to a web-site takeover, destructive redirects, spam injection, phishing and much a lot more,” said Ram Gall with Wordfence, on Monday.
What is a Cross-Site Request Forgery Flaw?
CSRF is a type of web flaw that permits an attacker to trick web browsers into carrying out destructive, unauthorized instructions. Normally, CSRF assaults are carried out by attackers with a link sent to the victim – and making use of social engineering to persuade them to simply click on it. When victims click on on the link, they are inadvertently sending a forged ask for to a server – resulting in the attacker currently being capable to execute different commands.
Critical NextGen Gallery Security Flaw
The much more significant of the two flaws is a critical-severity vulnerability (CVE-2020-35942). The flaw stems from NextGen Gallery’s security perform (is_licensed_ask for) that is made use of to defend its numerous options. This aspect integrates both of those a capability verify and a nonce test into a one function for easier software all through the plugin.
“Unfortunately, a logic flaw in the is_authorized_ask for purpose intended that the nonce verify would allow requests to continue if the $_Ask for[‘nonce’] parameter was lacking, relatively than invalid,” said scientists.
This could have authorized poor actors to have out several assaults. To exploit this flaw, an attacker would have to trick an administrator into clicking a hyperlink. This would then submit crafted requests to perform various malicious actions, explained scientists.
A profitable attack “would demand two different requests, nevertheless this would be trivial to implement and we ended up equipped to do so for the duration of our testing,” scientists reported. And, “the internet site would require at minimum a single album to be published and accessible to the attacker.”
If an attacker correctly persuaded an admin to simply click on a connection, the subsequent uploaded file would then be involved and executed any time the latter chosen album kind was seen on the web site. Any JavaScript incorporated in the uploaded file would then also be executed, reported scientists.
“As a reminder, the moment an attacker achieves remote code execution on a web-site, they have correctly taken around that web page,” claimed researchers. “XSS can furthermore be employed to get above a internet site if a logged-in administrator visits a website page functioning a malicious injected script.”
Superior-Severity File-Add Security Flaw
A 2nd, similar logic flaw (CVE-2020-35943) stemmed from a individual security purpose, validate_ajax_request, applied for a variety of AJAX actions such as those people utilised to upload images.
“This function had a identical logic flaw that would let requests to progress if the $_Request[‘nonce’] parameter was lacking, relatively than invalid,” claimed scientists.
Attackers could trick an administrator into distributing a ask for crafted to upload an arbitrary image file. Though the uploaded file experienced to be a valid impression file, it is feasible to cover a webshell or other destructive, executable PHP code within just this sort of an image file, they mentioned.
“This could also be blended with the former vulnerability, and the image file could be set as a ‘Legacy Template,’ at which position it would be incorporated and the code in just would be executed,” explained researchers. “Again, this would involve some degree of social engineering, as an attacker would have to trick an administrator into clicking a connection that resulted in these requests being sent.”
Update to NextGen Gallery Edition 3.5.
The developer of NextGen Gallery, Imagely, has issued patches for these flaws in edition 3.5.. In accordance to the NextGen Gallery plugin website page, only 26.2 % of consumers are using version 3.5. Threatpost has reached out to Imagely for further more remark.
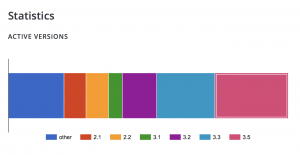
The selection of installs for each version of NextGen Gallery. Credit rating: Imagely
“If you know a close friend or colleague who is employing this plugin on their internet site, we remarkably suggest forwarding this advisory to them to assist maintain their web sites shielded as these are critical and substantial severity vulnerabilities that can direct to full web-site takeover,” stated researchers.
The flaw is only the most current to plague a WordPress plugin. Past 7 days, a security bug in Speak to Form 7 Style, a WordPress plugin set up on above 50,000 web-sites, was noted that could allow for for malicious JavaScript injection on a target website. And in January, two flaws (a person critical) in a WordPress plugin termed Orbit Fox ended up uncovered that could enable attackers to inject malicious code into vulnerable internet websites, or consider control of a website.
Download our exclusive Free Threatpost Insider Ebook, Healthcare Security Woes Balloon in a Covid-Era Environment, sponsored by ZeroNorth, to discover much more about what these security challenges suggest for hospitals at the day-to-working day stage and how health care security groups can implement most effective methods to protect companies and sufferers. Get the total tale and Obtain the Ebook now – on us!
Some parts of this article are sourced from:
threatpost.com


 Facebook is finally banning vaccine misinformation
Facebook is finally banning vaccine misinformation