An evolving phishing marketing campaign noticed at the very least considering the fact that May well 2020 has been uncovered to target significant-position organization executives throughout producing, actual estate, finance, government, and technological sectors with the objective of getting delicate information and facts.
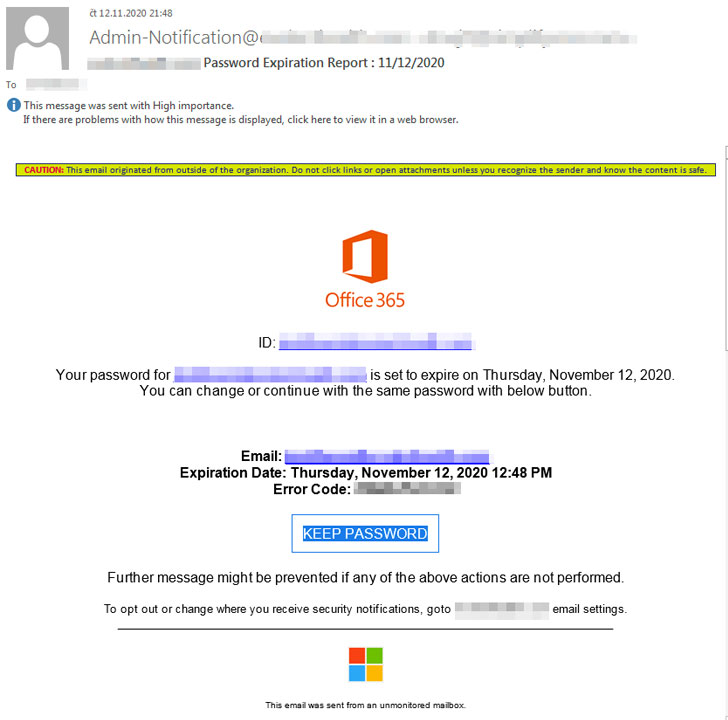
The marketing campaign hinges on a social engineering trick that entails sending email messages to opportunity victims containing bogus Business 365 password expiration notifications as lures. The messages also consist of an embedded backlink to keep the exact password that, when clicked, redirects customers to a phishing website page for credential harvesting.
“The attackers goal substantial profile workforce who may well not be as technically or cybersecurity savvy, and may be additional likely to be deceived into clicking on malicious links,” Trend Micro researchers explained in a Monday analysis.

“By selectively concentrating on C-degree staff, the attacker significantly will increase the worth of obtained qualifications as they could lead to more accessibility to sensitive particular and organizational information and facts, and applied in other attacks.”
According to the researchers, the specific email addresses were being mostly collected from LinkedIn, whilst noting that the attackers could have procured such goal lists from advertising web sites that present CEO/CFO email and social media profile details.
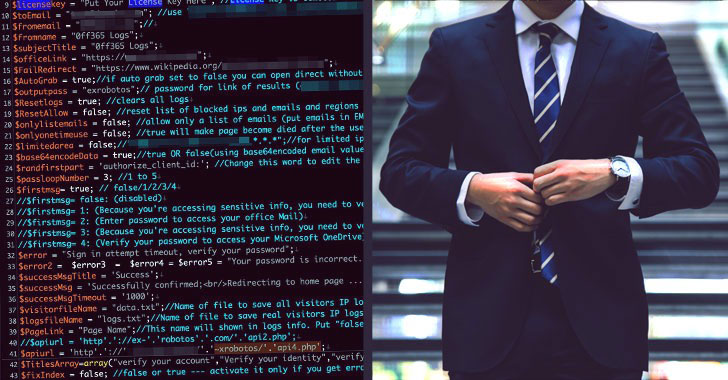
The Business office 365 phishing package, at this time in its fourth iteration (V4), is reported to have been initially launched in July 2019, with added functions included to detect bot scanning or crawling tries and provide alternative content material when bots are detected. Curiously, the alleged developer driving the malware declared V4’s availability on their “business” Fb web page in mid-2020.
Apart from providing the phishing kit, the actor has also been observed to peddle account credentials of CEOs, chief monetary officers (CFOs), finance office customers, and other higher-profile executives on social media internet pages.
What’s a lot more, Trend Micro’s investigation unearthed a doable website link to a user cope with on underground discussion boards that was spotted promoting a credential harvester instrument as nicely as stolen C-Stage account passwords everywhere in between $250 to $500, echoing preceding reports late very last 12 months.
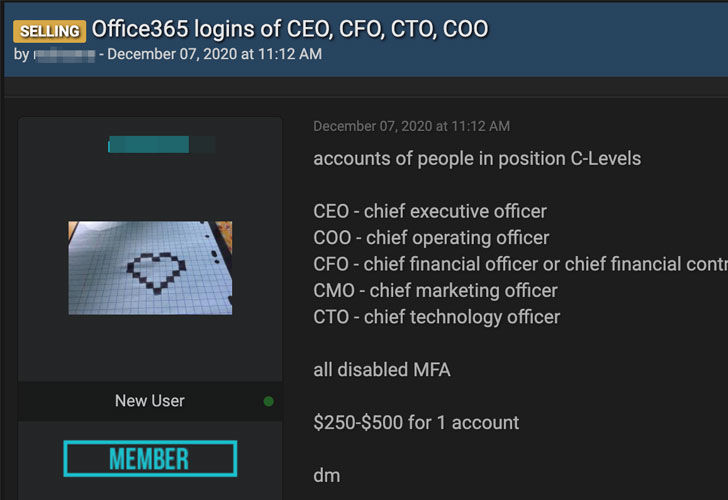
The researchers uncovered at minimum 8 compromised phishing sites hosting the V4 phishing package, raising the chance that they have been used by diverse actors for a extensive assortment of phishing campaigns directed in opposition to CEOs, presidents, board customers, and founders of corporations positioned in the U.S., the U.K., Canada, Hungary, the Netherlands, and Israel.
“Though corporations are conscious and wary of the facts they include things like in public-experiencing sites and platforms, their respective staff ought to be continually reminded to be aware of the information they disclose on individual webpages,” the scientists concluded. “These can be quickly employed versus them for attacks making use of social engineering strategies.”
Identified this post interesting? Observe THN on Fb, Twitter and LinkedIn to browse much more exclusive material we article.
Some parts of this article are sourced from:
thehackernews.com

 Apple's 'Time to Walk' stories arrive today for Fitness+ users
Apple's 'Time to Walk' stories arrive today for Fitness+ users