Various security vulnerabilities disclosed in Brocade SANnav storage place network (SAN) management application could be exploited to compromise vulnerable appliances.
The 18 flaws impression all variations up to and like 2.3., in accordance to unbiased security researcher Pierre Barre, who found and reported them.
The issues selection from incorrect firewall policies, insecure root accessibility, and Docker misconfigurations to deficiency of authentication and encryption, hence letting an attacker to intercept qualifications, overwrite arbitrary data files, and totally breach the gadget.

Some of the most severe flaws are mentioned underneath –
- CVE-2024-2859 (CVSS score: 8.8) – A vulnerability that could permit an unauthenticated, remote attacker to log in to an afflicted unit making use of the root account and execute arbitrary instructions
- CVE-2024-29960 (CVSS rating: 7.5) – The use of tricky-coded SSH keys in the OVA image, which could be exploited by an attacker to decrypt the SSH website traffic to the SANnav equipment and compromise it.
- CVE-2024-29961 (CVSS rating: 8.2) – A vulnerability that can enable an unauthenticated, distant attacker to phase a offer chain attack by getting advantage of the actuality the SANnav support sends ping commands in the qualifications at periodic intervals to the domains gridgain[.]com and ignite.apache[.]org to test for updates
- CVE-2024-29963 (CVSS score: 8.6) – The use of hard-coded Docker keys in SANnav OVA to reach distant registries in excess of TLS, therefore letting an attacker to have out adversary-in-the-center (AitM) attack on the visitors
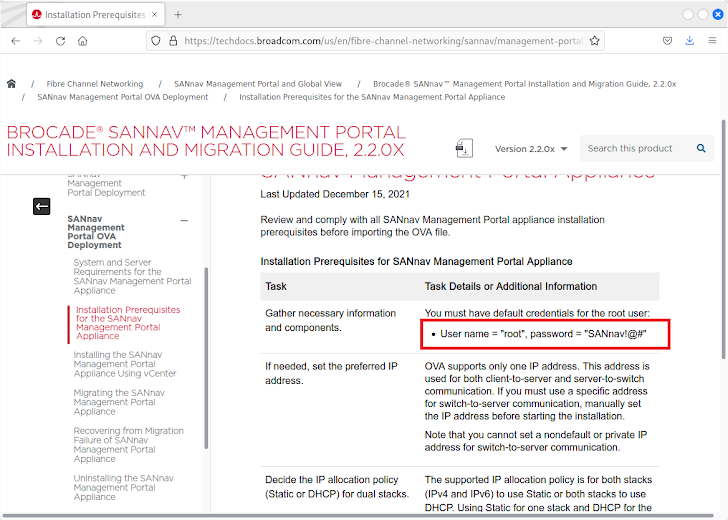
- CVE-2024-29966 (CVSS rating: 7.5) – The presence of difficult-coded credentials for root buyers in publicly-available documentation that could permit an unauthenticated attacker entire accessibility to the Brocade SANnav equipment.
Adhering to responsible disclosure two times in August 2022 and May perhaps 2023, the flaws have been resolved in SANnav edition 2.3.1 released in December 2023. Brocade’s mum or dad enterprise Broadcom, which also owns Symantec and VMware, introduced advisories for the flaws before this month.
Hewlett Packard Business has also delivered patches for a subset of these vulnerabilities in HPE SANnav Administration Portal variations 2.3.0a and 2.3.1 as of April 18, 2024.
Discovered this short article intriguing? Follow us on Twitter and LinkedIn to study far more exclusive material we submit.
Some parts of this article are sourced from:
thehackernews.com


 10 Critical Endpoint Security Tips You Should Know
10 Critical Endpoint Security Tips You Should Know