Scientists have pulled back the curtain on an updated edition of an Apple macOS malware called Rustbucket that will come with improved abilities to set up persistence and stay clear of detection by security application.
“This variant of Rustbucket, a malware family members that targets macOS methods, provides persistence abilities not earlier noticed,” Elastic Security Labs scientists reported in a report printed this week, including it is really “leveraging a dynamic network infrastructure methodology for command-and-command.”
RustBucket is the do the job of a North Korean risk actor acknowledged as BlueNoroff, which is section of a more substantial intrusion established tracked less than the identify Lazarus Team, an elite hacking device supervised by the Reconnaissance Common Bureau (RGB), the country’s major intelligence company.
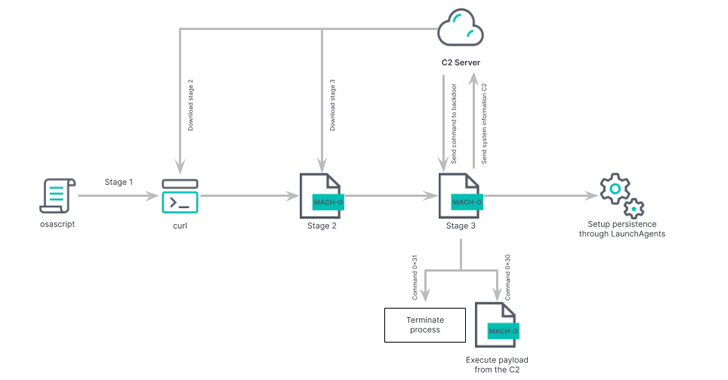
The malware came to light-weight in April 2023, when Jamf Danger Labs explained it as an AppleScript-dependent backdoor able of retrieving a 2nd-phase payload from a distant server. Elastic is monitoring the exercise as REF9135.

The second-phase malware, compiled in Swift, is developed to download from the command-and-control (C2) server the primary malware, a Rust-based binary with functions to gather comprehensive information as perfectly as fetch and run extra Mach-O binaries or shell scripts on the compromised process.
It is the initial instance of BlueNoroff malware particularly concentrating on macOS customers, even though a .NET version of RustBucket has given that surfaced in the wild with a related established of attributes.
“This new Bluenoroff activity illustrates how intrusion sets flip to cross-system language in their malware growth endeavours, further more increasing their capabilities extremely probable to broaden their victimology,” French cybersecurity corporation Sekoia reported in an analysis of the RustBucket marketing campaign in late May possibly 2023.
The infection chain is composed of a macOS installer file that installs a backdoored, but purposeful, PDF reader. A substantial component of the assaults is that the destructive action is induced only when a weaponized PDF file is launched working with the rogue PDF reader. Preliminary intrusion vector includes phishing e-mails, as perfectly as employing bogus personas on social networks these kinds of as LinkedIn.

The observed attacks are highly qualified and focused on finance-relevant institutions in Asia, Europe, and the U.S., suggesting that the exercise is geared toward illicit income generation to evade sanctions.
What would make the freshly recognized edition noteworthy is its uncommon persistence system and the use of dynamic DNS domain (docsend.linkpc[.]net) for command-and-regulate, alongside incorporating actions focused on remaining less than the radar.
“In the scenario of this up-to-date RUSTBUCKET sample, it establishes its own persistence by adding a plist file at the path /Buyers/
Located this posting intriguing? Abide by us on Twitter and LinkedIn to study more special written content we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Iranian Hackers Charming Kitten Utilize POWERSTAR Backdoor in Targeted Espionage Attacks
Iranian Hackers Charming Kitten Utilize POWERSTAR Backdoor in Targeted Espionage Attacks