A new strain of malicious software that’s engineered to penetrate and disrupt critical systems in industrial environments has been unearthed.
Google-owned risk intelligence organization Mandiant dubbed the malware COSMICENERGY, incorporating it was uploaded to a public malware scanning utility in December 2021 by a submitter in Russia. There is no proof that it has been put to use in the wild.
“The malware is intended to cause electric powered ability disruption by interacting with IEC 60870-5-104 (IEC-104) devices, this sort of as distant terminal models (RTUs), that are normally leveraged in electrical transmission and distribution operations in Europe, the Center East, and Asia,” the company said.
COSMICENERGY is the newest addition to specialized malware like Stuxnet, Havex, Triton, IRONGATE, BlackEnergy2, Industroyer, and PIPEDREAM, which are able of sabotaging critical techniques and wreaking havoc.
Mandiant said that there are circumstantial hyperlinks that it may well have been formulated as a purple teaming resource by Russian telecom agency Rostelecom-Solar to simulate electric power disruption and crisis reaction workouts that have been held in Oct 2021.
This raises the probability that the malware was both formulated to recreate sensible attack scenarios in opposition to electrical power grid assets to exam defenses or a further occasion reused code affiliated with the cyber selection.
The second substitute is not unheard of, primarily in light of the simple fact that danger actors are acknowledged to adapt and repurpose reputable pink staff and submit-exploitation instruments for destructive ends.
COSMICENERGY’s capabilities are equivalent to that of Industroyer – which has been attributed to the Kremlin-backed Sandworm team – owing to its potential to exploit an industrial conversation protocol termed IEC-104 to issue commands to RTUs.
“Leveraging this access, an attacker can ship remote instructions to influence the actuation of ability line switches and circuit breakers to trigger electric power disruption,” Mandiant explained.
Upcoming WEBINARZero Have faith in + Deception: Discover How to Outsmart Attackers!
Discover how Deception can detect advanced threats, quit lateral motion, and enrich your Zero Belief tactic. Join our insightful webinar!
Help you save My Seat!
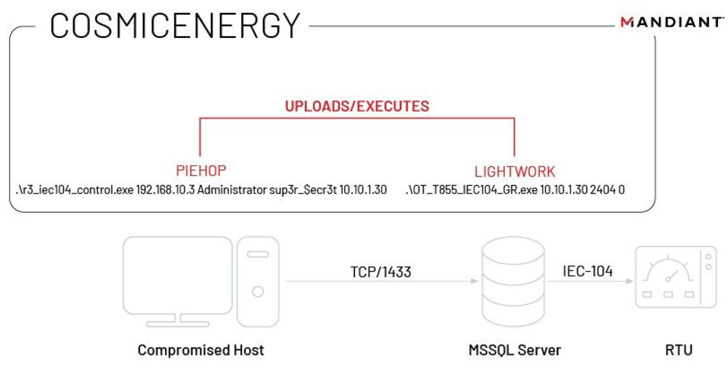
This is accomplished by usually means of two factors called PIEHOP and LIGHTWORK, which are two disruption tools composed in Python and C++, respectively, to transmit the IEC-104 commands to the related industrial machines.
Another notable aspect of the industrial regulate process (ICS) malware is the lack of intrusion and discovery capabilities, this means it necessitates the operator to execute an interior reconnaissance of the network to establish the IEC-104 system IP addresses to be targeted.
To pull off an attack, a threat actor would therefore have to infect a computer within just the network, come across a Microsoft SQL Server that has accessibility to the RTUs, and attain its credentials.
PIEHOP is then run on the device to upload LIGHTWORK to the server, which sends disruptive commands to linked industrial units. It also instantly deletes the executable right after issuing the commands.
“Though COSMICENERGY’s capabilities are not drastically distinct from preceding OT malware families’, its discovery highlights a number of noteworthy developments in the OT menace landscape,” Mandiant said.
“The discovery of new OT malware provides an rapid threat to impacted businesses, because these discoveries are rare and simply because the malware principally takes gain of insecure by design functions of OT environments that are not likely to be remedied any time before long.”
Uncovered this posting exciting? Comply with us on Twitter and LinkedIn to read through far more special content we article.
Some parts of this article are sourced from:
thehackernews.com


 Barracuda Warns of Zero-Day Exploited to Breach Email Security Gateway Appliances
Barracuda Warns of Zero-Day Exploited to Breach Email Security Gateway Appliances