After backlash more than bogus marketing around its encryption insurance policies, Zoom will ultimately roll out close-to-end encryption subsequent 7 days.
Video clip-conferencing huge Zoom is rolling out a technical preview of its conclusion-to-conclusion encryption (E2EE) next 7 days.
Zoom has confronted several controversies all over its encryption procedures in excess of the past calendar year, including several lawsuits alleging that the organization falsely told end users that it gives full encryption. Then, the platform arrived below fire in May possibly when it announced that it would in truth provide E2EE — but to paid consumers only. The company later backtracked right after backlash from privacy advocates, who argued that security steps ought to be out there to all. Zoom will now give the feature to free of charge/”Basic” end users.
The 1st phase of the E2EE rollout aims to solicit feedback when it comes to its guidelines. End users will be in a position to weigh in throughout the very first 30 times. Of be aware, customers will need to have to transform on the element manually (see underneath for information).
“We’re happy to roll out Stage 1 of 4 of our E2EE supplying, which delivers robust protections to aid prevent the interception of decryption keys that could be used to observe meeting content material,” mentioned Max Krohn, head of security engineering with Zoom, in a Wednesday write-up.
Conclude-To-Stop Encryption Mistakes
The topic of encryption is critical for Zoom as it ramps up its security and privacy steps – notably following various security flaws and privacy issues exposed weaknesses in the online conference platform, as its consumer base spiked all through the coronavirus pandemic.
Zoom previously claimed that it supplied E2EE, but that advertising assert arrived into dilemma following a March report from The Intercept said that Zoom’s platform essentially employs transport layer security (TLS) encryption, supplying only encryption involving unique customers and company vendors, as an alternative of immediately involving the customers of a process.
When “encryption” signifies that in-transit messages are encrypted, legitimate E2EE happens when the concept is encrypted at the resource user’s gadget, stays encrypted though its routed by means of servers, and then is decrypted only at the destination user’s unit.
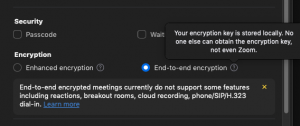
Zoom conclusion-to-end encryption enablement in settings. Credit: Zoom
On the heels of this backlash, Zoom in May well obtained a compact startup known as Keybase, with the aim of supplying additional sturdy encryption for Zoom calls.
In the situation of upcoming week’s rollout, Zoom’s E2EE providing will use public-critical cryptography, this means that the keys for just about every Zoom assembly are produced by participants’ equipment (as opposed to Zoom’s servers).
“While this is nevertheless confined throughout the capabilities it’s enabled for, it represents a substantial stage in the correct direction with regards to making certain user security and privateness on the platform,” Jack Mannino, CEO at nVisium, instructed Threatpost. “Distributing keys to the customers and decentralizing trust offers end users amplified assurance that their communications are less most likely to be intercepted through compromised keys or infrastructure.”
According to Krohn, “Encrypted knowledge relayed via Zoom’s servers is indecipherable by Zoom, given that Zoom’s servers do not have the required decryption important. This key administration method is equivalent to that employed by most conclude-to-end encrypted messaging platforms nowadays.”
Subsequent Week’s Rollout
Zoom hosts can enable E2EE at the account, team or user stage in their options. Zoom reported that in section 1 of its rollout, all conference contributors must sign up for from the Zoom desktop customer, cellular application or Zoom Rooms. In order to see that E2EE is enabled, individuals can look for a inexperienced defend logo in the upper left corner of their assembly display screen with a padlock in the middle.
Enabling the characteristic may possibly disable sure other characteristics, this kind of as “join in advance of host,” cloud recording, streaming, stay transcription, Breakout Rooms, polling, 1:1 non-public chat and conference reactions, mentioned Zoom.
“Zoom’s top precedence is the have faith in and security of our customers, and our implementation of E2EE will permit us to continue to enrich safety on our platform,” reported Zoom. “Free/Primary buyers in search of accessibility to E2EE will take part in a just one-time verification method that will prompt the consumer for further items of data, this sort of as verifying a phone range by way of textual content information.”
Zoom reported the 2nd stage of the rollout, which will contain greater id administration and E2EE solitary indicator-on (SSO) integration, is roadmapped for 2021.
Some parts of this article are sourced from:
threatpost.com


 Xiaomi Mi 10T vs Mi 10T Pro: What buyers get by paying Rs 4,000 extra
Xiaomi Mi 10T vs Mi 10T Pro: What buyers get by paying Rs 4,000 extra