A beforehand undocumented threat actor dubbed YoroTrooper has been focusing on governing administration, electricity, and international organizations throughout Europe as aspect of a cyber espionage campaign that has been active considering that at the very least June 2022.
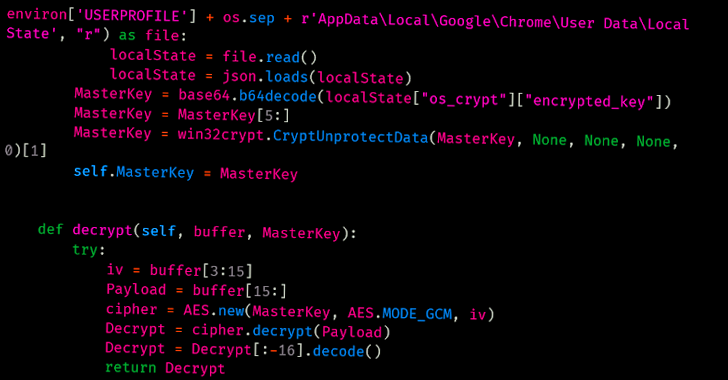
“Information and facts stolen from profitable compromises incorporate qualifications from various purposes, browser histories and cookies, system info and screenshots,” Cisco Talos scientists Asheer Malhotra and Vitor Ventura claimed in a Tuesday evaluation.
Well known nations around the world targeted consist of Azerbaijan, Tajikistan, Kyrgyzstan, Turkmenistan, and other Commonwealth of Unbiased States (CIS) nations.
The danger actor is thought to be Russian-talking owing to the victimology patterns and the presence of Cyrillic snippets in some of the implants.
That reported, the YoroTrooper intrusion set has been uncovered to exhibit tactical overlaps with the PoetRAT workforce that was documented in 2020 as leveraging coronavirus-themed baits to strike govt and strength sectors in Azerbaijan.
YoroTrooper’s info accumulating objectives are recognized through a combination of commodity and open source stealer malware these kinds of as Ave Maria (aka Warzone RAT), LodaRAT, Meterpreter, and Stink, with the an infection chains making use of destructive shortcut information (LNKs) and decoy files wrapped in ZIP or RAR archives that are propagated through spear-phishing.
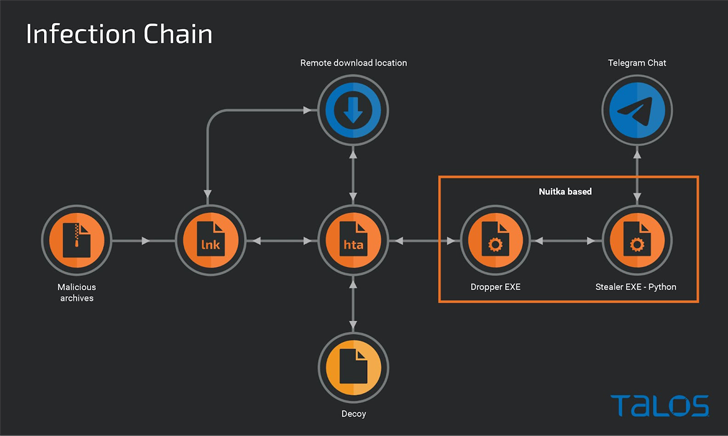
The LNK documents function as simple downloaders to execute an HTA file retrieved from a remote server, which is then employed to screen a entice PDF doc, though stealthily launching a dropper to supply a custom stealer that utilizes Telegram as an exfiltration channel.
WEBINARDiscover the Concealed Hazards of Third-Celebration SaaS Applications
Are you aware of the pitfalls connected with 3rd-occasion app accessibility to your firm’s SaaS applications? Be a part of our webinar to study about the types of permissions staying granted and how to decrease risk.
RESERVE YOUR SEAT
The use of LodaRAT is noteworthy as it suggests that the malware is being utilized by numerous operators in spite of its attribution to an additional group referred to as Kasablanka, which has also been noticed distributing Ave Maria in new campaigns concentrating on Russia.
Other auxiliary resources deployed by YoroTrooper consist of reverse shells and a C-based customized keylogger that’s able of recording keystrokes and preserving them to a file on disk.
“It is value noting that although this marketing campaign commenced with the distribution of commodity malware this kind of as Ave Maria and LodaRAT, it has evolved substantially to contain Python-centered malware,” the researchers explained.
“This highlights an raise in the attempts the menace actor is placing in, likely derived from effective breaches all through the course of the marketing campaign.”
Uncovered this article interesting? Follow us on Twitter and LinkedIn to go through extra distinctive written content we article.
Some parts of this article are sourced from:
thehackernews.com

 Microsoft Patches Two Zero Days This Month
Microsoft Patches Two Zero Days This Month