Cybersecurity scientists have found an ongoing phishing marketing campaign that helps make use of a special attack chain to deliver the XWorm malware on qualified techniques.
Securonix, which is tracking the action cluster under the title MEME#4CHAN, reported some of the attacks have mostly targeted manufacturing companies and health care clinics situated in Germany.
“The attack marketing campaign has been leveraging rather unconventional meme-filled PowerShell code, followed by a closely obfuscated XWorm payload to infect its victims,” security scientists Den Iuzvyk, Tim Peck, and Oleg Kolesnikov explained in a new examination shared with The Hacker Information.
The report builds on the latest findings from Elastic Security Labs, which uncovered the threat actor’s reservation-themed lures to deceive victims into opening destructive files capable of delivering XWorm and Agent Tesla payloads.

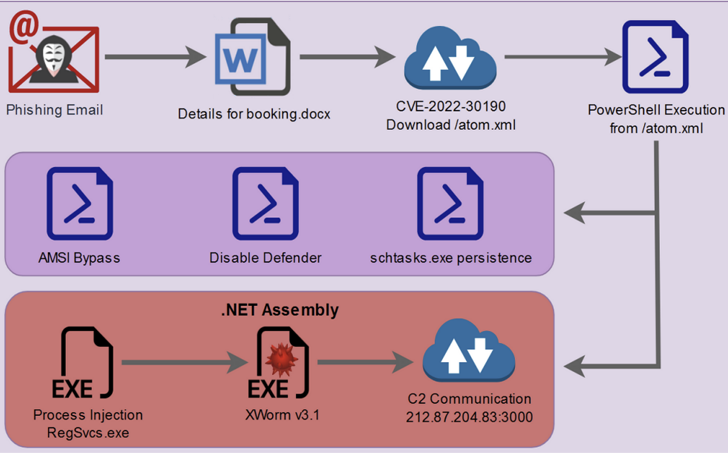
The attacks commence with phishing attacks to distribute decoy Microsoft Term files that, as a substitute of employing macros, weaponize the Follina vulnerability (CVE-2022-30190, CVSS rating: 7.8) to fall an obfuscated PowerShell script.
From there, the danger actors abuse the PowerShell script to bypass Antimalware Scan Interface (AMSI), disable Microsoft Defender, establish persistence, and in the end start the .NET binary made up of XWorm.
Interestingly, a person of the variables in the PowerShell script is named “$CHOTAbheem,” which is likely a reference to Chhota Bheem, an Indian animated comedy experience tv sequence.
“Primarily based on a brief verify, it seems that the individual or team accountable for the attack could have a Center Japanese/Indian track record, while the final attribution has not however been verified,” the scientists explained to The Hacker Information, pointing out that such key terms could also be made use of as a go over.
XWorm is a commodity malware which is advertised for sale on underground community forums and comes with a huge assortment of characteristics that allows it to siphon sensitive information and facts from contaminated hosts.
Impending WEBINARLearn to Quit Ransomware with Serious-Time Security
Be part of our webinar and find out how to prevent ransomware assaults in their tracks with real-time MFA and provider account defense.
Help save My Seat!
The malware is also a Swiss Army knife in that it can execute clipper, DDoS, and ransomware operations, distribute through USB, and fall supplemental malware.
The actual origins of the menace actor are at the moment unclear, even though Securonix said the attack methodology shares artifacts equivalent to that of TA558, which has been observed striking the hospitality business in the past.
“However phishing e-mails hardly ever use Microsoft Business office files since Microsoft produced the choice to disable macros by default, currently we’re viewing proof that it is nonetheless vital to be vigilant about malicious document data files, especially in this case where there was no VBscript execution from macros,” the researchers mentioned.
Observed this post attention-grabbing? Abide by us on Twitter and LinkedIn to go through a lot more exceptional written content we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Essential Addons Plugin Flaw Exposes One Million WordPress Websites
Essential Addons Plugin Flaw Exposes One Million WordPress Websites