With breaches building the headlines on an practically weekly basis, the cybersecurity difficulties we encounter are getting obvious not only to large enterprises, who have developed security abilities around the several years, but also to compact to medium corporations and the broader public. While this is generating greater consciousness amongst lesser companies of the have to have to improve their security posture, SMBs are typically still left facing a hole in the industry, not able to find security tooling that is each quick for them to use and which they can afford to pay for.
When we consider the desires of SMBs, we need to emphasis both on the growth of menace intelligence, which is needed to realize and discover the threats currently being faced, as very well as the resources employed to supply defense. NTTSH has created a pedigree of around 20 years’ expertise in the investigation and curation of risk intelligence as effectively as the enhancement of capabilities and goods which leverage its danger intelligence to defend customers. Right after many yrs of target on bigger enterprises, NTTSH is transferring to democratize cybersecurity and offer lesser firms with the defense they require.
World Menace Intelligence Heart
All of NTTSH’s efforts are underpinned by the abilities of its Worldwide Menace Intelligence Heart (GTIC). The attempts of the GTIC go past all those of a pure investigation organization by taking menace study and combining it with NTTSH proprietary detective technology to produce utilized risk intelligence.
The GTIC’s mission is to shield customers by delivering highly developed menace exploration and security intelligence, enabling NTTSH to reduce, detect, and reply to cyber threats. To give a really special vantage issue in NTTSH’s merchandise and expert services, GTIC leverages proprietary intelligence abilities and NTT’s situation as the operator of just one of the world’s best 5 tier 1 Internet backbones, furnishing unequaled visibility of Internet telemetry to achieve an understanding of and insight into the a variety of danger actors, exploit equipment and malware – and the practices, tactics, and methods employed by attackers. In addition to curating its own threat intelligence research, GTIC also maintains relationships with other important gamers in this area, such as the Cyber Danger Alliance, Microsoft, CISA, and the Nationwide Cyber Forensics and Coaching Alliance (NCFTA).
NTTSH’s once-a-year International Threat Intelligence Report (GTIR) provides a window into the operate finished by GTIC, giving a synopsis of the essential worries in the security landscape experiencing businesses of all dimensions, alongside one another with actionable insights to assist corporations far better adapt to the evolving threat landscape. In the Q3 update of the 2023 GTIR, a particular aim was positioned on essential field verticals, giving insights into the threats they facial area.
Danger focus by sector
The healthcare sector faces a exclusive established of problems, not only because of to the higher value of the information and facts owned by healthcare companies but also as a outcome of steep advancement in the adoption of technology in healthcare in a context the place a lot of providers, in particular smaller sized kinds, lack recognition of cybersecurity and also do not have the means to deploy and maintain the varieties of controls enjoyed by big enterprises. Ransomware is however proving notably problematic. Healthcare ransomware breaches are proving to be specifically concentrated throughout a couple of geographies, with the United states, Australia, and the British isles accounting for shut to 80% of these breaches.
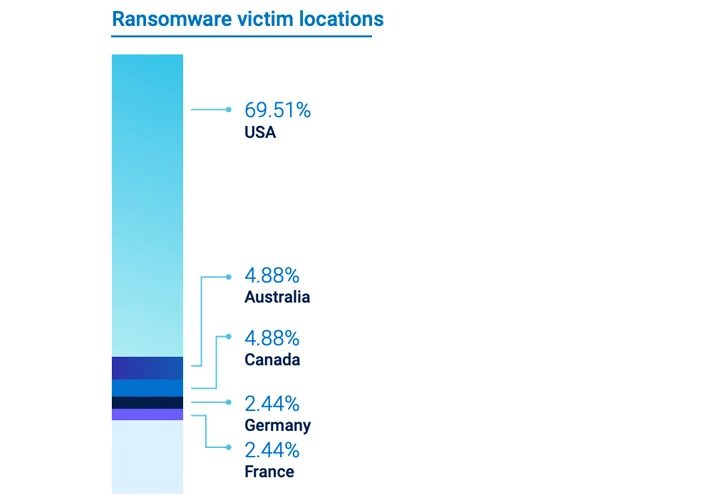 Determine 1: Ransomware target spots in the Health care sector.
Determine 1: Ransomware target spots in the Health care sector.
A identical geographic trend is obvious in the telecommunications sector, where by the United states of america, United kingdom, and Australia account for about 52% of ransomware attacks, even though in training, the Usa, British isles, and Canada account for around 83%.
Across all of the emphasis sectors, Lockbit 3. remains the most prolific ransomware menace actor. Some ransomware actors are, even so, focusing on certain sectors, this kind of as the Bl00dy ransomware gang, which specifically targets instruction.
 Figure 2: Leading ransomware actors in the telecommunications sector
Figure 2: Leading ransomware actors in the telecommunications sector
Security Difficulties of SaaS
A latest location of focus for GTIC has been the way in which the speedily accelerating adoption of SaaS is presenting its individual set of challenges. SaaS is rapidly getting to be an integral element of the working day-to-working day functions of both equally compact and substantial businesses, with once-a-year progress envisioned to carry on at a level of shut to 20% as a result of 2027. In this context, it is crucial to note that 99% of cloud security breaches are expected to be the customer’s fault, in accordance to Gartner.
The shared responsibility product for cloud services has been anything that larger enterprises have been familiar with for some time already. More compact businesses are, nonetheless, however coming to grips with this product. In respect of SaaS, this signifies that though the cloud supplier is responsible for the software, SMBs are still adapting to the actuality that they retain accountability for their data and, crucially, control their accounts and identities. Risk actors are, as a outcome, focusing on strategies to compromise identities, specially applying methods such as credential stuffing and phishing.
Struggling with up to the Troubles of Hybrid IT
Even though SMBs were being earlier in a position to rely on antivirus software and firewalls to shield the technology assets on their premises, most have now moved into the world of hybrid IT as they ever more depend on cloud-shipped products and services. Even though the security controls delivered by most cloud products and services are good, SMBs experience a selection of problems in employing the security performance that is available to them.
As the attack surface area of even smaller corporations expands, the number of sources of security alerting grows. That is not the only challenge: danger actors will frequently not confine their pursuits to just one section of your technology estate. They may get started in 1 region, for instance, by compromising a person or far more endpoints (these kinds of as laptops) and then use the data they assemble (these kinds of as qualifications) to transfer laterally, for instance, to compromise a SaaS software. Whilst substantial enterprises have invested the final 10 a long time or extra developing devoted SecOps groups and intricate security toolchains, SMBs absence the assets for this variety of investment.
Democratizing Security Operations with XDR
What SMBs require is the capability to bring alerting from all of their IT infrastructure and purposes into a single tool, which can evaluate all of an organization’s telemetry, apply menace intelligence, and then deliver a uncomplicated interface that functions as a one pane of glass for handling alerting, accomplishing investigations and responding to threats. This is wherever XDR gives a remedy that combines the essential elements of a regular SecOps toolchain in a one cloud-hosted application, which can be delivered affordably. This is the next vital location where NTTSH has turned its aim towards SMBs by concentrating the enhancement of its Samurai XDR product on the demands and budgets of SMBs when nonetheless offering the performance that large enterprises have develop into accustomed to. Even though GTIC’s investigate delivers the intelligence wanted to recognize and detect the threats experiencing contemporary businesses, Samurai XDR tends to make GTIC’s perform obtainable and actionable even for organizations that absence committed SecOps sources. It is essential to recall that when threat intelligence is important to be ready to detect threats, every group requirements resources in order to use it.
A quick journey by way of Samurai XDR
From the start, Samurai XDR is created to be simple to use and, most importantly, to be obtainable to all IT personnel, not only to security analysts. The starting off issue of all workflows in Samurai XDR is the alerts dashboard. This is where the method offers security alerts which have been prioritized primarily based on severity and self-assurance.
 Figure 3: Samurai XDR Alerts Dashboard
Figure 3: Samurai XDR Alerts Dashboard
The alerts dashboard provides jointly alerts from all of the systems made use of by the organization into a single prioritized check out, with a aim on delivering an intuitive interface that can be employed by most IT staff, not only by professional security analysts.
The moment the person has determined that an inform warrants additional investigation, the Investigations look at supplies a equally basic and intuitive interface for handling the lifecycle of an investigation of a possible security incident.
After gatherings and alerts are processed, they are saved in Samurai XDR’s info lake. The details lake offers the potential for end users to question and review all of the situations ingested into Samurai XDR, going back up to one particular entire yr. This makes it doable to interrogate a whole year’s historical info for uses these kinds of as menace searching – allowing Samurai XDR buyers to perform detailed analyses of historic gatherings for any indications of threats that may perhaps have been dwelling for for a longer time periods of time. Querying the situations in the details lake is manufactured possible by Samurai XDR’s Superior Question operate, which enables consumers to research the details lake each graphically and employing Microsoft’s Kusto Query Language (KQL).
Integrations
Integrations offer the mechanism to ingest telemetry (this sort of as logs) from your IT infrastructure and programs into Samurai XDR. NTTSH has concentrated on bringing jointly the suitable mix of capabilities to ingest telemetry from both on-premises infrastructure and cloud providers, mirroring the variety of hybrid IT natural environment that has turn out to be standard for even most SMBs now. Some illustrations of integrations presently available consist of:
- Cloud: Azure Management Plane and Microsoft 365 (coming quickly), Google Workspace (coming before long)
- Endpoint Detection and Reaction: Microsoft Defender for Endpoint, VMWare Carbon Black and Crowdstrike Falcon Perception
- Following-Technology Firewalls: Cisco Protected Firewall (ASA and Firepower Menace Protection), Fortinet Fortigate, and Palo Alto Networks NGFW.
Over the coming months, NTTSH will be occupied incorporating extra integrations, including but not confined to Meraki, Bitdefender, Sophos, Zoom, MalwareBytes, OneLogin, OKTA, Zscaler, AWS, and a lot of additional!
Producing it Quick
A essential area of focus for NTTSH in the improvement of Samurai XDR has been that of generating it straightforward to use and easy to afford. For instance, the configuration of integrations is supported by simple “level and simply click” workflows. For infrastructure that supplies logs via syslog, all that is desired is to place the log supply at Samurai XDR’s safe syslog collector, and Samurai XDR will do the function of detecting the type of system that is sending logs. Obviously, it truly is the similar for cloud integrations. Samurai XDR retains the ways to a least and guides the user by interactive steps and accessibility to know-how-foundation articles.
Samurai XDR also follows a basic pricing model – primarily based entirely on the variety of endpoints that the customer has, removing the want to consider to estimate the data volumes of the telemetry that will be ingested into the platform. Common pricing for 50 endpoints or a lot more is only $3.33 for each endpoint per month, and for more compact buyers, there is a Starter Pack for up to 25 endpoints, which is priced at $750 for a 12 months.
To make it simple to check out out Samurai XDR, NTTSH is supplying all new consumers with a cost-free 30-day trial, earning it probable to knowledge all of its functionality without having any commitments, providing even the smallest SMBs a risk-no cost route to building an sophisticated SecOps ability.
Discovered this post interesting? This post is a contributed piece from 1 of our valued associates. Stick to us on Twitter and LinkedIn to read through additional exceptional information we put up.
Some parts of this article are sourced from:
thehackernews.com


 Malicious ‘SNS Sender’ Script Abuses AWS for Bulk Smishing Attacks
Malicious ‘SNS Sender’ Script Abuses AWS for Bulk Smishing Attacks