In past year’s edition of the Security Navigator we pointed out that the Producing Sector appeared to be totally in excess of-represented in our dataset of Cyber Extortion victims. Neither the range of businesses nor their normal income specifically stood out to explain this.
Manufacturing was also the most represented Market in our CyberSOC dataset – contributing extra Incidents than any other sector.
We found this development confirmed in 2023 – so a great deal in reality that we determined to acquire a nearer look. So let us look at some attainable explanations.
And debunk them.
Looking for probable explanations
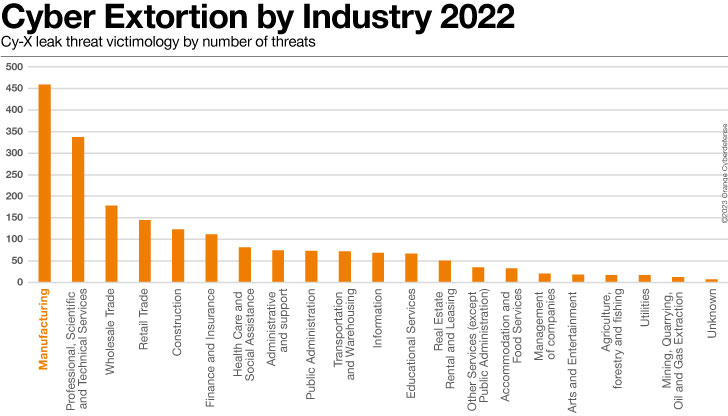
Production is continue to the most impacted business in our Cyber Extortion dataset in 2023, as tracked by checking double-extortion leak web sites. In fact, this sector now represents more than 20% of all victims considering that we started observing the leak sites in the beginning of 2020.
Approximately 28% of all our customers are from Production, contributing with an general share of 31% of all likely incidents we investigated.
We observe that 58% of the Incidents this sector bargains with are internally induced, 32% had been externally caused, 1% was categorised as “Lover” or 3rd parties. When external menace actors had brought about the security incident, we observed the top 3 threat steps ended up Web Assaults, Port Scanning and Phishing.
On the other hand, Manufacturing has the most affordable apparent quantity of confirmed security vulnerabilities for every IT Asset in our Vulnerability scanning dataset. Our pentesting groups on the other hand report 4.81 CVSS results per working day, which is pretty a bit previously mentioned the typical of 3.61 throughout all other industries.
Numerous issues present by themselves, which we will endeavor to analyze listed here:
What portion does OT play?
A tempting assumption to make is that corporations in the Manufacturing sector are compromised more typically by using notoriously insecure Operational Technology (OT) or Internet of Items (IoT) devices. Vegetation and factories can usually not afford to pay for to be disrupted or shut down and that Production is hence a comfortable target for extortionists.
It certain sounds plausible. The capture is: we really don’t see these theories supported in our info.
The attack in opposition to US Power huge Colonial Pipeline was probably the most noteworthy recent illustration of a prosperous attack in opposition to an industrial facility.
Discover the most recent in cybersecurity with extensive “Security Navigator 2023” report. This research-driven report is based mostly on 100% first-hand info from 17 worldwide SOCs and 13 CyberSOCs of Orange Cyberdefense, the CERT, Epidemiology Labs and Environment Check out and supplies a prosperity of useful facts and insights into the present-day and upcoming menace landscape.
In July this year US intelligence companies even warned of a hacking toolset dubbed ‘Pipedream’ that is intended focus on particular Industrial Regulate Devices. But it is not apparent to us if or when these tools have at any time been encountered in the wild. Apart from the infamous Stuxnet attack from 2010, 1 struggles to recall a solitary cyber security incident where by the entry point was an OT system.
At Colonial Pipeline the backend ‘conventional’ administrative methods were compromised first. Wanting additional closely, this is the scenario for practically all claimed incidents at industrial amenities.
Are enterprises in the Producing sector additional susceptible to attacks?
To reply this queries we examined a established of 3 million vulnerability scan findings, and a sample of 1,400 Ethical Hacking stories.
We derived three metrics that facilitate relatively normalized comparisons throughout the industries in our customer base:
VOC scanning conclusions per asset, time to patch, Pentest results for each day of screening.
If we rank industries for their efficiency on each individual of these metrics and sort from worst to best, then our purchasers in the Producing sector comes in 5th put out of 12 equivalent industries.
The chart down below demonstrates the total *ranking* of our Producing consumers out of equivalent industries.

VOC exceptional findings/asset
On this metric there have been seven other industries that executed far better than Manufacturing.
Although we have a comparatively higher quantity of property from Production clientele in our scanning dataset, we report significantly less Results per Asset than the normal across all industries. Nearly 10 times less, in point.
Time to patch
On this metric 6 other industries ranked much better than Producing. The normal age of all results for this field is 419 days, which is a concerning amount and worse than recorded for 8 other industries in this dataset.
Pentesting conclusions
We notice that the typical CVSS For each Day was 4.81, as opposed to 3.61 on typical for shoppers in all other sectors in the dataset – 33% better.
Is the Production sector remaining targeted additional by extortionists?
We use the North American Field Classification Procedure – NAICS – classification procedure when categorizing our shoppers.
A thing to consider of double-extortion victim counts for every industry reveals a quite exciting pattern: Of the 10 industries with the most recorded victims in the dataset, 7 are also counted amongst the biggest industries by entity depend.
Production on the other hand, is a crystal clear craze-breaker.
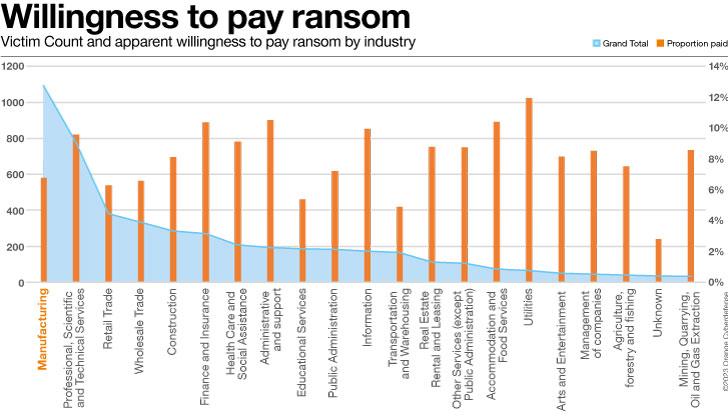
A further variable raises inquiries: if firms in the Manufacturing sector were being more ready to fork out ransom that would make them extra beautiful as victims. But then we would assume to see these kinds of enterprises that includes on the ‘name and shame’ leak website considerably less frequently, not extra.
Do our Manufacturing consumers working experience a lot more incidents?
The Manufacturing field as soon as again generated the maximum variety of Incidents as a proportion of the full in our CyberSOC dataset. 31% of all Incidents are produced for the 28% of our shoppers that are from this sector.
The Incident knowledge lacks context, nonetheless. To establish a baseline for comparison, we assign shoppers a ‘Coverage Score’ between and 5 in 8 distinctive ‘domains’ of Danger Detection, accounting for a highest full detection rating of 40.
We use the coverage score to normalize the incident rely. Set simply, the lessen a client’s assessed coverage score is, the more this adjustment will ‘boost’ the number of Incidents in this comparison. The logic is that a very low quantity of coverage will just not show us a good deal of incidents, while they quite likely occurr.
If we modify the Genuine Favourable and Phony Beneficial Incidents as described above, we nevertheless see more than 7 times as several Incidents for every shoppers from Production than the common for all industries.
In a related comparison, restricted only to Perimeter Security, and only Medium Sized business enterprise, Production ranks 1st with the most Incidents per Client out of 7 similar Industries.
Summary
We ruled out a large influence of OT security vulnerabilities, and therefore emphasis on common IT programs. Our scanning teams assessed a massive amount of targets but documented comparatively several vulnerabilities for every asset. Over-all, we rank the Producing sector as 5th or 6th weakest of all industries from a vulnerability place of see.
The dilemma of why we regularly document such a large proportion of victims from the Production market is not commonly answered with the details we have. We believe that that in the finish it still comes down to the level of vulnerability, finest reflected in our Penetration Screening, and Conclusions Age facts.
All of our details factors to the simple fact that attackers are primarily opportunistic. Somewhat than deliberately singling industries out, they just compromise businesses that are vulnerable.
The prospects represented in our datasets have engaged with us for Vulnerability Evaluation or Managed Detection, and thus represent somewhat ‘mature’ illustrations of that field. We can deduce that ordinary companies in this sector would benchmark even worse in terms of vulnerabilities. No matter whether the higher range of victims we notice on attacker leak-sites is a immediate reflection of the high amount of over-all victims in this sector, or the skewed reflection of an field that refuses to concede to initial ransom needs, is not totally crystal clear.
What does look probably, on the other hand, is that vulnerability is the primary element that decides which enterprises get compromised and extorted – in this sector as a lot as any other.
This is just an excerpt of the investigation. More details on how distinct Industries performed in comparison to other individuals, as very well as extra CyberSOC, Pentesting and VOC information (together with plenty of other interesting study subject areas) can be identified in the Security Navigator. It’s free of charge, so have a appear. It is really worthy of it!
Take note: This article has been written and contributed by Charl van der Walt, Head of Security Analysis at Orange Cyberdefense.
Identified this short article exciting? Stick to us on Twitter and LinkedIn to study extra exclusive content material we post.
Some parts of this article are sourced from:
thehackernews.com


 Multiple Hacker Groups Exploit 3-Year-Old Vulnerability to Breach U.S. Federal Agency
Multiple Hacker Groups Exploit 3-Year-Old Vulnerability to Breach U.S. Federal Agency