4 months following security researchers uncovered a “Tetrade” of 4 Brazilian banking Trojans targeting economic establishments in Brazil, Latin The usa, and Europe, new results display that the criminals powering the operation have expanded their practices to infect mobile units with spyware.
According to Kaspersky’s World-wide Analysis and Investigation Team (Good), the Brazil-based danger group Guildma has deployed “Ghimob,” an Android banking Trojan targeting monetary applications from banks, fintech organizations, exchanges, and cryptocurrencies in Brazil, Paraguay, Peru, Portugal, Germany, Angola, and Mozambique.
“Ghimob is a complete-fledged spy in your pocket: at the time an infection is finished, the hacker can access the infected unit remotely, completing the fraudulent transaction with the victim’s smartphone, so as to keep away from device identification, security steps applied by financial institutions and all their anti-fraud behavioral systems,” the cybersecurity business mentioned in a Monday investigation.
In addition to sharing the similar infrastructure as that of Guildma, Ghimob carries on the modus operandi of applying phishing email messages as a mechanism to distribute the malware, luring unsuspecting consumers into clicking malicious URLs that downloads the Ghimob APK installer.
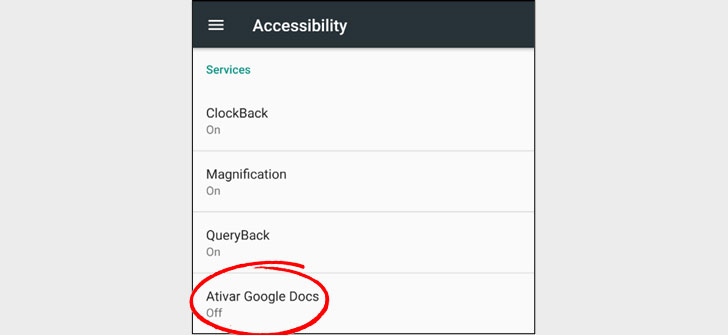
The Trojan, after set up on the unit, features a great deal similar to other cell RATs in that it masks its presence by hiding the icon from the app drawer and abuses Android’s accessibility characteristics to achieve persistence, disable handbook uninstallation and let the banking trojan to seize keystrokes, manipulate screen material and supply whole remote control to the attacker.
“Even if the consumer has a monitor lock pattern in location, Ghimob is in a position to report it and later on replay it to unlock the system,” the scientists claimed.
“When the cybercriminal is prepared to conduct the transaction, they can insert a black display as an overlay or open some website in whole screen, so even though the person seems at that screen, the felony performs the transaction in the history by employing the monetary application managing on the victim’s smartphone that the person has opened or logged in to.”
What is actually more, Ghimob targets as numerous as 153 cell applications, 112 of which are economic establishments based mostly in Brazil, with cryptocurrency and banking applications in Germany, Portugal, Peru, Paraguay, Angola, and Mozambique accounting for the relaxation.
“Ghimob is the first Brazilian mobile banking trojan ready to expand and goal economic establishments and their customers dwelling in other nations around the world,” Kaspersky researchers concluded. “The Trojan is nicely well prepared to steal qualifications from banks, fintechs, exchanges, crypto-exchanges, and credit score playing cards from monetary institutions functioning in a lot of countries.”
Located this article fascinating? Abide by THN on Facebook, Twitter and LinkedIn to browse much more exceptional information we post.
Some parts of this article are sourced from:
thehackernews.com


 Housing Group Struck by Sodinokibi Data Thieves
Housing Group Struck by Sodinokibi Data Thieves