Researchers have issued a warning about an rising and state-of-the-art sort of voice phishing (vishing) identified as “Letscall.” This method is at this time focusing on people today in South Korea.
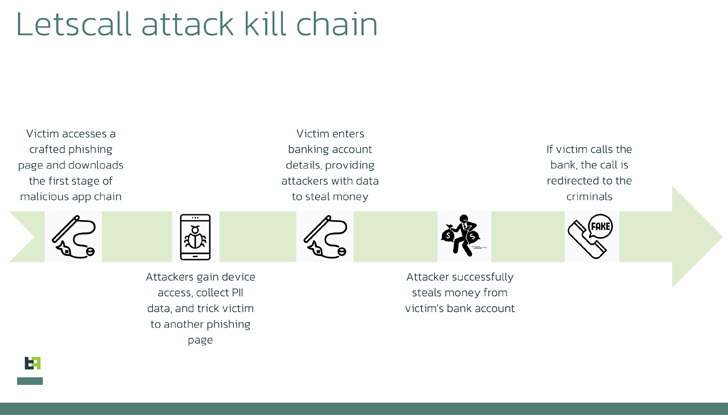
The criminals driving “Letscall” utilize a multi-move attack to deceive victims into downloading malicious apps from a counterfeit Google Participate in Keep web page.
After the destructive software is set up, it redirects incoming phone calls to a call centre beneath the control of the criminals. Experienced operators posing as financial institution personnel then extract delicate details from unsuspecting victims.
To aid the routing of voice traffic, “Letscall” utilizes slicing-edge systems these as voice around IP (VOIP) and WebRTC. It also tends to make use of Session Traversal Utilities for NAT (STUN) and Traversal Working with Relays all-around NAT (Switch) protocols, together with Google STUN servers, to make sure higher-top quality phone or video calls and bypass NAT and firewall restrictions.
The “Letscall” group is composed of Android developers, designers, frontend and backend builders, as perfectly as connect with operators specializing in voice social engineering attacks.
The malware operates in a few levels: to start with, a downloader app prepares the victim’s product, paving the way for the set up of potent spyware. This spy ware then triggers the ultimate phase, which lets the rerouting of incoming calls to the attackers’ get in touch with heart.
“The third phase has its have established of commands, which also includes Web socket commands. Some of these instructions relate to the manipulation of the address e book, these types of as producing and eradicating contacts. Other commands relate to generating, modifying, and eliminating the filters that ascertain which calls need to be intercepted and which should be ignored,” Dutch cell security agency ThreatFabric mentioned in its report.
What sets “Letscall” aside is its utilization of superior evasion methods. The malware incorporates Tencent Legu and Bangcle (SecShell) obfuscation through the preliminary down load. In later on phases, it employs intricate naming structures in ZIP file directories and deliberately corrupts the manifest to confuse and bypass security techniques.

Criminals have created systems that quickly get in touch with victims and enjoy pre-recorded messages to even more deceive them. By combining mobile phone bacterial infections with vishing tactics, these fraudsters can ask for micro-financial loans in the victims’ names whilst assuring them of suspicious pursuits and redirecting phone calls to their facilities.
Upcoming WEBINAR🔐 Privileged Accessibility Administration: Understand How to Conquer Vital Issues
Learn unique methods to conquer Privileged Account Administration (PAM) issues and stage up your privileged obtain security approach.
Reserve Your Spot
The outcomes of these types of assaults can be significant, leaving victims burdened with sizeable loans to repay. Monetary establishments frequently underestimate the severity of these invasions and fail to look into opportunity fraud.
Whilst this menace is presently minimal to South Korea, scientists caution that there are no technological boundaries protecting against these attackers from expanding to other regions, like the European Union.
This new variety of vishing attack underscores the constant evolution of criminal tactics and their potential to exploit technology for destructive applications. The team liable for the “Letscall” malware demonstrates intricate information of Android security and voice routing technologies.
Uncovered this article intriguing? Abide by us on Twitter and LinkedIn to browse a lot more exclusive content we post.
Some parts of this article are sourced from:
thehackernews.com


 Another Critical Unauthenticated SQLi Flaw Discovered in MOVEit Transfer Software
Another Critical Unauthenticated SQLi Flaw Discovered in MOVEit Transfer Software