The threat actor powering the information-thieving malware recognized as Typhon Reborn has resurfaced with an up to date version (V2) that packs in enhanced abilities to evade detection and resist examination.
The new model is provided for sale on the criminal underground for $59 for every month, $360 for each 12 months, or alternatively, for $540 for a life span membership.
“The stealer can harvest and exfiltrate delicate facts and works by using the Telegram API to ship stolen info to attackers,” Cisco Talos researcher Edmund Brumaghin said in a Tuesday report.
Typhon was first documented by Cyble in August 2022, detailing its myriad options, like hijacking clipboard written content, capturing screenshots, logging keystrokes, and stealing info from crypto wallet, messaging, FTP, VPN, browser, and gaming apps.
Based on a different stealer malware known as Prynt Stealer, Typhon is also able of offering the XMRig cryptocurrency miner. In November 2022, Palo Alto Networks Device 42 unearthed an current edition dubbed Typhon Reborn.
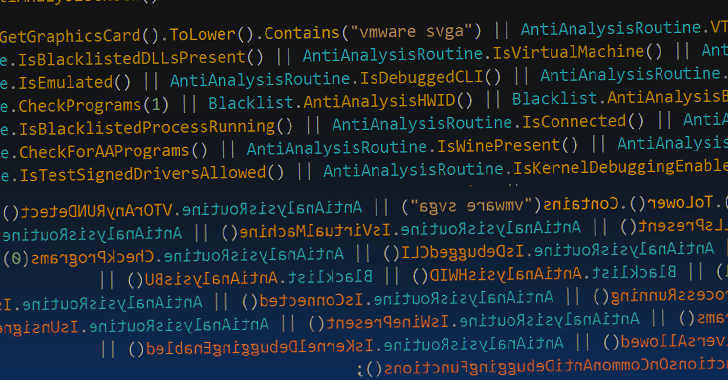
“This new variation has enhanced anti-investigation approaches and it was modified to boost the stealer and file grabber capabilities,” Device 42 explained, pointing out the removal of present options like keylogging and cryptocurrency mining in an apparent endeavor to reduced the likelihood of detection.
The most current V2 variant, per Cisco Talos, was promoted by its developer on January 31, 2023, on the Russian language dark web forum XSS.
“Typhon Reborn stealer is a heavily refactored and improved edition of the more mature and unstable Typhon Stealer,” the malware creator stated, in addition to touting its economical value and the absence of any backdoors.
Like other malware, V2 comes with alternatives to stay away from infecting units that are found in the Commonwealth of Unbiased States (CIS) countries. It, however, notably excludes Ukraine and Georgia from the record.

Moreover incorporating additional anti-examination and anti-virtualization checks, Typhon Reborn V2 removes its persistence capabilities, instead opting to terminate by itself right after exfiltrating the knowledge.
The malware in the end transmits the gathered information in a compressed archive by means of HTTPS utilizing the Telegram API, marking continued abuse of the messaging platform.
“At the time the facts has been efficiently transmitted to the attacker, the archive is then deleted from the infected process,” Brumaghin explained. “The malware then calls [a self-delete function] to terminate execution.”
Upcoming WEBINARLearn to Secure the Identity Perimeter – Proven Methods
Strengthen your organization security with our upcoming pro-led cybersecurity webinar: Investigate Id Perimeter procedures!
Never Pass up Out – Help you save Your Seat!
The results come as Cyble disclosed a new Python-based mostly stealer malware named Creal that targets cryptocurrency users by way of phishing sites mimicking legitimate crypto mining products and services like Kryptex.
The malware is no various from Typhon Reborn in that it can be equipped to siphon cookies and passwords from Chromium-primarily based web browsers as well as information from instantaneous messaging, gaming, and crypto wallet applications.
That reported, the malware’s source code is available on GitHub, therefore allowing for other menace actors to alter the malware to fit their wants and generating it a powerful danger.
“Creal Stealer is capable of exfiltrating information working with Discord webhooks and multiple file-hosting and sharing platforms this sort of as Anonfiles and Gofile,” Cyble explained in a report printed previous week.
“The development of making use of open supply code in malware is expanding among the cybercriminals, because it lets them to generate sophisticated and tailored attacks with minimum costs.”
Located this posting intriguing? Abide by us on Twitter and LinkedIn to browse far more unique written content we publish.
Some parts of this article are sourced from:
thehackernews.com

 Mind-control robots a reality?
Mind-control robots a reality?