Cybersecurity researchers took the wraps off a novel supply chain attack in South Korea that abuses legitimate security application and stolen electronic certificates to distribute distant administration instruments (RATs) on goal techniques.
Attributing the procedure to the Lazarus Group, also recognised as Hidden Cobra, Slovak internet security company ESET claimed the point out-sponsored risk actor leveraged the required necessity that internet customers in the country ought to put in additional security computer software in buy to avail Internet banking and necessary authorities products and services.
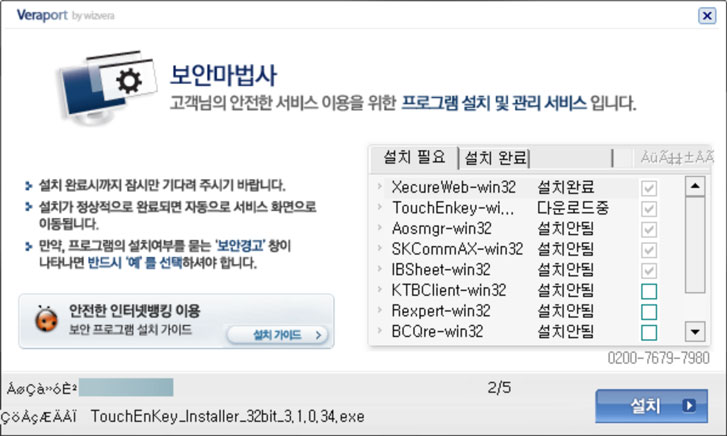
The attack, even though minimal in scope, exploits WIZVERA VeraPort, which is billed as a “plan created to combine and regulate internet banking-associated set up programs,” this kind of as electronic certificates issued by the banking institutions to men and women and businesses to protected all transactions and course of action payments.
The enhancement is the hottest in a long record of espionage assaults towards victims in South Korea, together with Procedure Troy, DDoS attacks in 2011, and versus banking institutions and cryptocurrency exchanges around the final ten years.
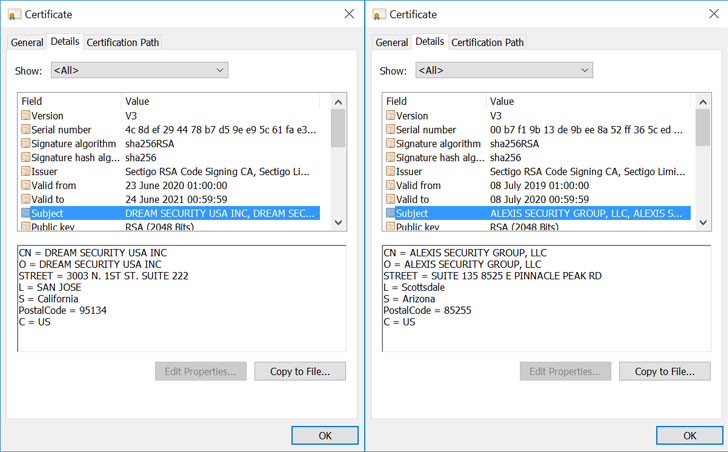
Aside from applying the aforementioned technique of installing security application in order to supply the malware from a respectable but compromised internet site, the attackers utilised illegally received code-signing certificates in purchase to signal the malware samples, one particular of which was issued to the US branch of a South Korean security company named Desire Security United states of america.
“The attackers camouflaged the Lazarus malware samples as reputable computer software. These samples have related file names, icons and methods as authentic South Korean software,” ESET researcher Peter Kálnai said. “It truly is the mix of compromised internet sites with WIZVERA VeraPort guidance and particular VeraPort configuration possibilities that permits attackers to execute this attack.”
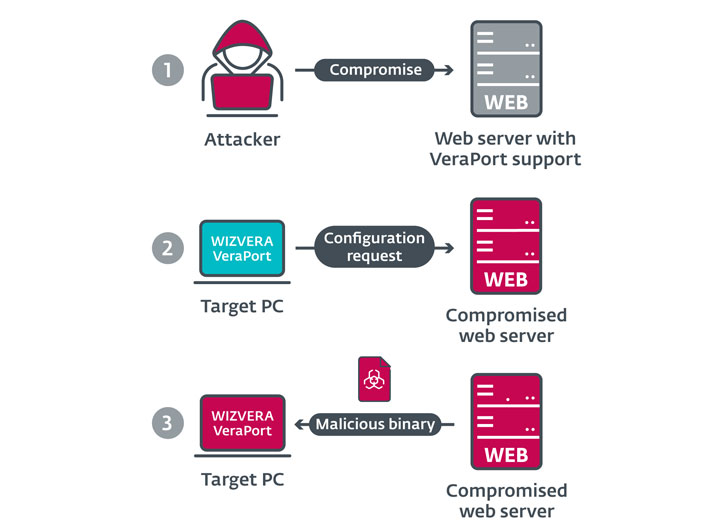
Stating that the attacks goal sites that use VeraPort — which also arrives with a foundation64-encoded XML configuration file that contains a list of software program to put in and their associated obtain URLs — ESET researchers mentioned the adversaries changed the program to be shipped to VeraPort buyers by compromising a legitimate web site with malicious binaries that were being then signed with illicitly obtained code-signing certificates to provide the payloads.
“WIZVERA VeraPort configurations include an option to verify the digital signature of downloaded binaries just before they are executed, and in most scenarios this possibility is enabled by default,” the researchers pointed out. “On the other hand, VeraPort only verifies that the electronic signature is legitimate, with out examining to whom it belongs.”
The binary then proceeds to download a malware dropper that extracts two additional elements — a loader and a downloader — the latter of which is injected into just one of the Windows procedures (“svchost.exe”) by the loader. The remaining-phase payload fetched by the downloader can take the kind of a RAT that will come equipped with instructions allowing for the malware to carry out operations on the victim’s filesystem and obtain and execute auxiliary instruments from the attacker’s arsenal.
What is more, the marketing campaign seems to be what is actually a continuation of a different Lazarus-mounted attack called Procedure BookCodes comprehensive by the Korea Internet & Security Company earlier this April, with important overlaps in TTPs and command-and-handle (C2) infrastructure.
“Attackers are specially fascinated in provide-chain assaults, since they permit them to covertly deploy malware on numerous pcs at the same time,” the scientists concluded.
“Owners of [websites with VeraPort support] could reduce the probability of this kind of attacks, even if their web sites are compromised, by enabling precise possibilities (e.g. by specifying hashes of binaries in the VeraPort configuration).”
Found this article interesting? Abide by THN on Facebook, Twitter and LinkedIn to browse additional unique material we put up.
Some parts of this article are sourced from:
thehackernews.com


 Samsung Galaxy Buds Beyond certified at 3C, battery capacity revealed
Samsung Galaxy Buds Beyond certified at 3C, battery capacity revealed