Corporations all-around the globe – which features Travelex – have been despatched letters threatening to start DDoS assaults on their network unless of course a $230K ransom is compensated.
Businesses throughout the planet have ongoing to get extortion e-mails threatening to start a dispersed denial-of-services (DDoS) attack on their network, other than they devote up – with British abroad-exchange firm Travelex reportedly getting just a single new excellent-profile risk receiver.
Researchers noted that due to the fact mid-August, quite a few suppliers have been despatched email messages that alert that their business network will be hit by a DDoS attack in about a 7 times. The unique ransom demand from clients is established at 20 BTC – which interprets to about $230,000 at the time of composing – and cybercriminals threaten to raise that ransom by 10 BTC for every person operating working day not paid out, discussed experts.
While a sizeable sum of exercise was 1st tracked in August, that training then slowed down in the in the beginning 50 percent of September – only to “grow significantly” in the conclude of September and commencing of Oct, Radware researchers described to Threatpost.
Travelex (which has absent by its honest share of security woes a lot more than the past 12 months, commencing with a New Year’s ransomware attack) was one these forms of org threatened with a DDoS attack, except if it compensated 20 bitcoins (BTC), Intel471 scientists described on Tuesday. A bitcoin wallet take care of in the email reveals that Travelex did not shell out the attackers at any issue, they pointed out.
“Following the extortion email, the risk actor carried out a volumetric attack on a tailor made port of 4 IP addresses serving the company’s subdomains,” in accordance to Intel471 researchers. “Two periods later on on, the attackers carried out one more DNS amplification attack against Travelex applying Google DNS servers.”
Threatpost has arrived at out to Travelex for even more remark on the DDoS extortion menace.
Ongoing DDoS Extortion Threats
Whilst the ransom DDoS marketing and advertising campaign has been ongoing due to the fact August and has acquired preferred security, scientists with Radware claimed in a Wednesday set up that they are continuing to see organizations all through the earth get the extortion email messages – and that attackers are turning into far additional refined.
“There is no way to connect with the blackmailers, so there is no range to negotiate and the only way to get a information as a end result of is by sending BTC to the bitcoin manage talked about in the letter,” scientists claimed.
The extortion email messages assert that the menace team has by now released a tiny DDoS attack on the victim’s IPs (of the ASN assortment pointed out in the letter) to give the danger legitimacy. The attackers also assert that they have the indicates to complete volumetric assaults that peak at 2Tbps – really considerably achieving the levels of the 2.3Tbps attack concentrating on an Amazon Web Specialist solutions purchaser in February that was the most significant volumetric DDoS attack on heritage.
“These threats are not hoaxes, and the actors have adopted up with assaults,” Pascal Geenens, director of risk intelligence at Radware, explained to Threatpost. “While we have not observed the 2TBps attack threatened in the letter supplied the report, corporations have found assaults ranging up to 300GBps and combining several attack vectors. These assaults can be devastating for a lot of firms.”
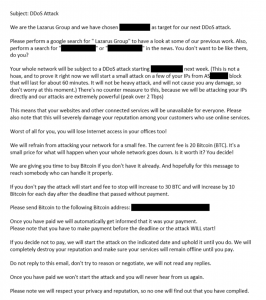
A sample DDoS ransom letter. Credit: Radware
Of note, the extortion threats were sent to generic email addresses in just just the companies, which did not usually access the proper distinct human being in the firm – and were becoming even usually obtained by subsidiaries of businesses in the mistaken condition. Possessing claimed that, even though beforehand iterations of the ransom take note ended up elementary, experts recognized the menace actor raising their sophistication.
“The letters have been improved thinking of the actuality that the commence off of the advertising campaign by correcting some typos, rephrasing some techniques for better clarity, and press security of before DDoS assaults that impacted economic companies has been extra to instill a large amount much more panic,” claimed scientists.
The risk actor purports to be various APTs, posing as Extravagant Bear, Armada Collective and Lazarus Staff. The actors look to be to have a choice of APT based on the vertical they are striving to impact to pay back a ransom: The cybercriminals purport to be Lazarus Staff when concentrating on monetary providers, (this variety of as in Travelex’s circumstance, for occasion), despite the fact that they fake to be Fancy Bear when focusing on technology and production orgs.
Nevertheless, scientists pointed to discrepencies that show that the danger actors are essentially posing as these APTs as opposed to acquiring the genuine deal: “Based on what we know about the common approaches, processes and processes of these APT groups, the menace motion that we are viewing does not match up,” Geenens explained to Threatpost. “Attribution is generally guesswork, and it is unattainable to make an comprehensive assertion a single distinct way or 1 extra. Even if an APT group had been remaining to confess to these threats, it would be unattainable to ensure regardless of whether or not they are even telling the reality.”
It is truly value noting that these ransom threats are completely practically nothing new. In 2019, cybercriminals posing as Extravagant Bear launched DDoS assaults versus businesses in the financial sector and demanded ransom payments. And back in 2016, a group (who also referred to as by on their own the Armada Collective) sent extortion e-mail to distinct on the internet companies threatening to start DDoS assaults if they weren’t compensated out in Bitcoin. All the way yet again in 2015, the FBI claimed that it was viewing an optimize in the wide variety of organizations keeping qualified by scammers threatening to launch DDoS assaults if they really do not fork out a ransom.
In their ransom letters, attackers assert there are no counter-measures to defend in opposition to their attacks. Researchers noted this is not the case, and recommended businesses to not fork out the ransom wish: “There is no guarantee blackmailers will honor the phrases of their letter,” they mentioned. “Paying only funds long term operations, allows them to maximize their talents and motivates them to carry on on the internet marketing campaign.”
Some items of this report are sourced from:
threatpost.com


 India Witnessed Spike in Cyber Attacks Amidst Covid-19 – Here’s Why?
India Witnessed Spike in Cyber Attacks Amidst Covid-19 – Here’s Why?