A malicious extension for Chromium-dependent web browsers has been observed to be distributed via a lengthy-standing Windows facts stealer referred to as ViperSoftX.
Czech-dependent cybersecurity corporation dubbed the rogue browser incorporate-on VenomSoftX owing to its standalone capabilities that enable it to entry website visits, steal qualifications and clipboard data, and even swap cryptocurrency addresses by using an adversary-in-the-center (AiTM) attack.
ViperSoftX, which to start with arrived to mild in February 2020, was characterized by Fortinet as a JavaScript-based mostly distant obtain trojan and cryptocurrency stealer. The malware’s use of a browser extension to advance its facts-accumulating goals was documented by Sophos menace analyst Colin Cowie before this year.
“This multi-phase stealer displays fascinating hiding abilities, concealed as modest PowerShell scripts on a one line in the middle of normally harmless-seeking substantial log information, among the some others,” Avast researcher Jan Rubín reported in a complex create-up.
“ViperSoftX focuses on thieving cryptocurrencies, clipboard swapping, fingerprinting the contaminated device, as effectively as downloading and executing arbitrary added payloads, or executing commands.”
The distribution vector used to propagate ViperSoftX is commonly accomplished by means of cracked application for Adobe Illustrator and Microsoft Workplace that are hosted on file-sharing websites.
The downloaded executable file will come with a thoroughly clean model of cracked software alongside with added information that established up persistence on the host and harbor the ViperSoftX PowerShell script.
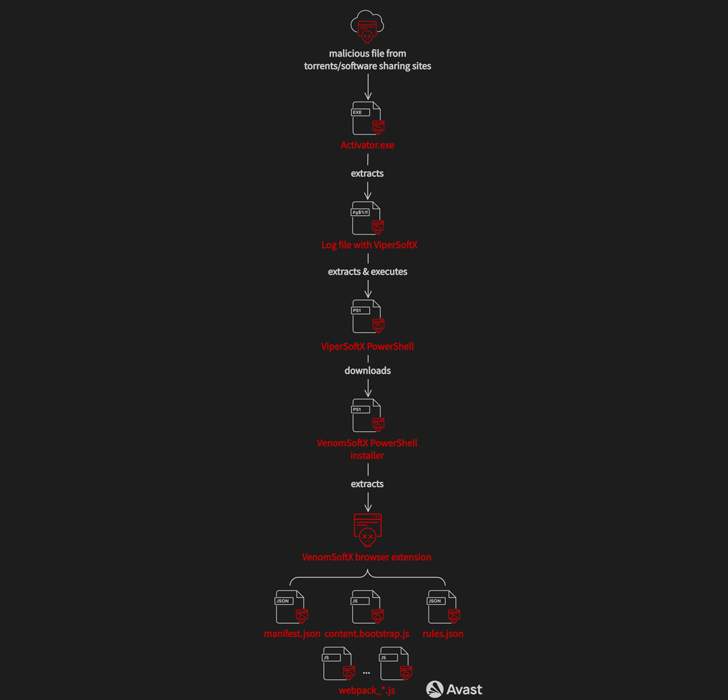
Newer variants of the malware are also able of loading the VenomSoftX add-on, which is retrieved from a distant server, to Chromium-based mostly browsers these kinds of as Google Chrome, Microsoft Edge, Opera, Brave, and Vivaldi.
This is accomplished by seeking for LNK data files for the browser apps and modifying the shortcuts with a “–load-extension” command line switch that factors to the path in which the unpacked extension is saved.
“The extension tries to disguise by itself as well recognised and frequent browser extensions this kind of as Google Sheets,” Rubín spelled out. “In fact, the VenomSoftX is still another data stealer deployed on to the unsuspecting sufferer with full obtain permissions to each site the person visits from the infected browser.”
It is really worth noting that the –load-extension tactic has also been set to use by one more browser-centered info stealer referred to as ChromeLoader (aka Choziosi Loader or ChromeBack).
VenomSoftX, like ViperSoftX, is also orchestrated to steal cryptocurrencies from its victims. But not like the latter, which functions as a clipper to reroute fund transfers to an attacker-controlled wallet, VenomSoftX tampers with API requests to crypto exchanges to drain the electronic belongings.
Providers targeted by the extension include things like Blockchain.com, Binance, Coinbase, Gate.io, and Kucoin.
The progress marks a new level of escalation to classic clipboard swapping, when also not boosting any instant suspicion as the wallet handle is changed at a substantially more essential degree.
Avast claimed it has detected and blocked in excess of 93,000 infections because the start of 2022, with a the greater part of the impacted consumers positioned in India, the U.S., Italy, Brazil, the U.K., Canada, France, Pakistan, and South Africa.
An examination of the really hard-coded wallet addresses in the samples reveals that the procedure has netted its authors a sum overall of about $130,421 as of November 8, 2022, in many cryptocurrencies. The collective monetary achieve has given that dropped to $104,500.
“Considering the fact that the transactions on blockchains/ledgers are inherently irreversible, when the person checks the transaction historical past of payments afterward, it is by now also late,” Rubín said.
Located this report appealing? Observe THN on Fb, Twitter and LinkedIn to study far more special written content we article.
Some parts of this article are sourced from:
thehackernews.com


 Firms Spend $1197 Per Employee Yearly to Address Cyber-Attacks
Firms Spend $1197 Per Employee Yearly to Address Cyber-Attacks