Here’s a difficult problem to answer: ‘How lots of support accounts do you have in your setting?’. A tougher a single is: ‘Do you know what these accounts are performing?’. And the hardest is possibly: ‘If any of your support account was compromised and utilized to access resources would you be able to detect and end that in real-time?’.
Due to the fact most identity and security teams would give a destructive reply, it’s no speculate that one particular of the rapid steps modern attackers are doing pursuing an preliminary endpoint compromised is looking down unwatched service accounts. And it’s even less of a marvel that in most conditions, they would succeed in getting one particular and leveraging it to distribute in the whole setting, acquiring noticed only when it truly is far too late – following workstations and server obtained encrypted by ransomware or sensitive data was stolen.
In this write-up, we unfold the causes that have prompted assistance accounts to turn out to be 1 of the most perilous weaknesses in an Energetic Directory natural environment, describe how this weak point energy fuels ransomware attacks, and at last, get to know how Silverfort’s unified identification security platform allows corporations to prevail over what was until eventually now an insolvable security problem.
Assistance Accounts: User Accounts That Are Not Involved With Any True Person And Are Applied For Machine-To-Device Interaction
Consumer accounts are one particular of the important creating blocks in the enterprise setting. Intuitively, we affiliate person accounts with actual people today. Nevertheless, there are also person accounts that are not connected with any human becoming. These accounts are produced for equipment-to-machine communication, automation of repetitive duties, and other assignments that are meant to choose put in the background devoid of human intervention. They are usually recognized as ‘service accounts’ and apart from their dissociation from a serious individual, are similar in all elements to the other, ‘people-associated’ user accounts.
These service accounts are designed in two major techniques. The first, is an IT personnel that determines that a selected cleanliness, monitoring, or any other endeavor would be much better done in an automated method, instead than guide method. The next, is in the training course of setting up an business program on-prem. In that case, some services accounts are produced per the instruction of the certain software – in the system of the set up itself – and are tasked with scanning, distributing updates and comparable upkeep assignments.
Support Account Security Worries: Invisible, Highly Privileged, And Particularly Really hard To Safeguard
Let us recognize what can make service accounts an unattended attack surface:
- Absence of visibility: As bizarre as it could seem, there is no utility inside the id infrastructure that can quickly filter out company accounts from the overall pool of consumers. Nor is there any automated documentation system in put that suggests a services account’s creation.
- Large accessibility privileges: Given that provider accounts are developed for machine-to-device interaction, it goes with out saying that they ought to have the demanded privileges to entry all these machines, indicating that they are an administrative consumer, no diverse than any IT admin.
- No PAM safety: The popular follow is to secure administrative accounts by putting them in a PAM solution’s vault and rotate their passwords. Even so, this method can’t be used to provider accounts for the reason that their passwords are hardcoded in the scripts that run their responsibilities. As this sort of, any password rotation would invalidate the password in the scripts, stopping the support account from accessing its focus on source, and subsequently split any approach that relies on the service accounts’ endeavor.
4 Techniques For Extensive Company Account Security
There are innumerable service accounts in any supplied business. These accounts can grow to be superior-risk belongings that, if still left unchecked, could enable threats to propagate through the network undetected. Check out out this Book to find out 4 very simple techniques to enable retain your assistance accounts protected.
Down load E-book
How Attackers Leverage The Low-Hanging Fruit Of Provider Accounts For Lateral Motion And Ransomware Spread
Let us think that a ransomware actor has correctly compromised an endpoint (workstation or server are the similar for that issue). This, of class, is just the very first step. The future stage is to start scanning the natural environment to uncover user accounts to compromise that would allow the adversary to laterally move within just the environment and plant the ransomware payload in as numerous equipment as probable.
But what account to pick? The adversary desires an account which is privileged adequate to entry other servers and workstations. But it ought to also be an account that can be made use of below the radar without having drawing undesired consideration.
This is why support accounts are the best compromise concentrate on. Attackers know that there is a excellent possibility, that no 1 is on the lookout on this account, or even far better – that nobody even knows that this account exists. It may well have been established decades in the past by an admin that has considering that remaining the corporation without bothering to delete the company accounts he established.
Company Account Attack Case in point #1: Ransomware Attack Sample Applying Compromised Microsoft Trade Server’s Company Account
The diagram under shows a sample attack – just one of lots of we’ve analyzed in the latest year – in which the adversary has utilized a compromised Trade Server’s assistance account for the very first portion its lateral movement, followed by an more compromise of an admin credentials.
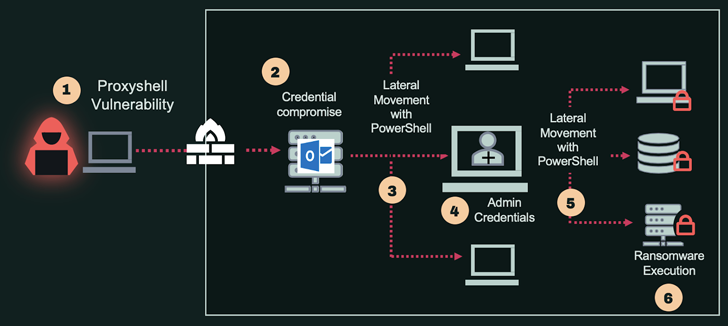
See the specifics of each stage underneath:
Company Account Attack Case in point #2: Lateral Movement in Uber’s Hybrid Surroundings
The famous attack on Uber that took put a several months back included a substantial use of compromise and use of services account. In that circumstance, it was a assistance account that has obtain to the PAM in spot. The attackers uncovered the script with the assistance account credentials in a shared network push and used it to extract passwords to several resources from the PAM’s vault.
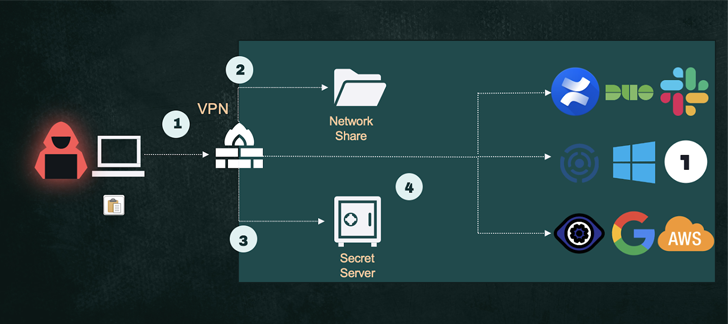
See the information of every stage below:
Silverfort Automatic Discovery, Monitoring And Safety For Assistance Accounts
Silverfort’s unified id protection system is the first alternative that completely automates the security lifecycle of assistance account with near-zero work from the user’s side:
Discovery of all assistance accounts and mapping of their activity
Silverfort’s native integration with Active Listing enables it to analyze each incoming authentication and access endeavor of all user accounts, and quickly detect if an account options the predictable and repetitive actions that differentiates company accounts from regular end users. Based on this analysis, Silverfort generates an output of all the support accounts in just the natural environment. Additionally, this discovery goes further than just a checklist of accounts to also show the account’s privileges, it is really sources and destinations, activity stage and other behavioral options.
Constant risk assessment to disclose if a services account shows indications of compromise
Silverfort identifies the baseline habits of every support account and repeatedly displays its exercise. For a support account, the clearest indication of compromise is a deviation from its fixed actions, so every time a deviation occurs – such as accessing a new workstation or server, or quickly raising the exercise quantity – Silverfort’s motor will elevate the account’s risk score.
Energetic protection with vehicle-established procedures, activated in a one click
Silverfort automates the creation of an entry coverage for each and every of the provider accounts it discovers. This coverage is activated every time the services account deviates from its regular habits (as previously spelled out) or when its risk level enhanced thanks to detected identity threats (Move-the-Hash, Kerberoasting, Pass-the-Ticket and so on.). The policy can induce both an notify or precise blocking of the services account entry, per the user’s configuration. The only conversation required from the user aspect is click on the policy activation button.
On the lookout for a way to secure your support accounts? Agenda a phone with 1 of our industry experts to master how Silverfort can guide.
Identified this write-up fascinating? Follow us on Twitter and LinkedIn to read far more exceptional material we article.
Some parts of this article are sourced from:
thehackernews.com


 Microsoft Fixes Zero-Day Bug This Patch Tuesday
Microsoft Fixes Zero-Day Bug This Patch Tuesday