Gcore Radar is a quarterly report ready by Gcore that offers insights into the current condition of the DDoS safety industry and cybersecurity tendencies. This report gives you an understanding of the evolving threat landscape and highlights the steps expected to protect versus assaults successfully. It serves as an perception for businesses and people searching for to keep educated about the newest developments in cybersecurity.
As we entered 2023, the cybersecurity landscape witnessed an enhance in complex, significant-quantity attacks. Listed here, we current the present state of the DDoS defense market based mostly on Gcore’s studies.
Vital Highlights from Q1–Q2
- The greatest attack electrical power rose from 600 to 800 Gbps.
- UDP flood assaults ended up most frequent and amounted to 52% of complete assaults, although SYN flood accounted for 24%. In third spot was TCP flood.
- The most-attacked company sectors are gaming, telecom, and money.
- The longest attack period in the year’s 1st 50 % was seven days, 16 hrs, and 22 minutes.
- Most attacks lasted considerably less than 4 hrs.
Higher-Volume Attacks: An Escalating Menace
There has been a sizeable maximize in the electrical power and quantity of DDoS assaults above the very last two many years:
- In 2021, the ability of DDoS attacks was up to 300 Gbps.
- In 2022, the attack potential was about 650 Gbps.
- In Q1–Q2 of 2023, we see a capacity of about 800 Gbps.
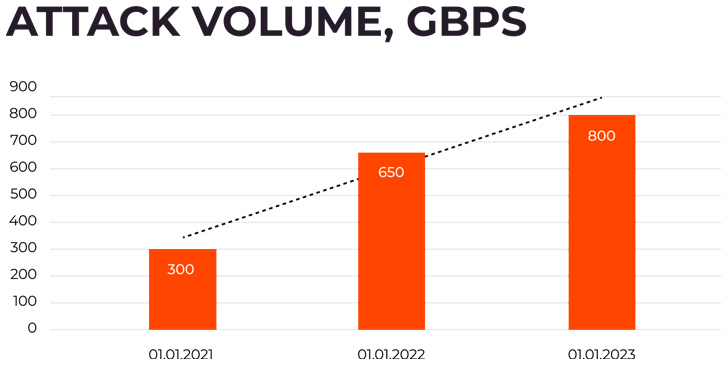 Figure 1. Attack intrensity 2021–2023, Gbps
Figure 1. Attack intrensity 2021–2023, Gbps
Alt Text: Illustration of attack boosting from 300 Gbps in 2021 and 650 Gbps in 2021 to 800 Gbps in 2023
The alarming 50–100% annual enhance in DDoS attack volume highlights the developing sophistication of cyber attackers and their utilization of ever more effective tools. This means that businesses have to have to make investments in DDoS mitigation strategies and options to secure their networks, methods, and client info. Failure to deal with these evolving threats can result in expensive disruptions, reputational harm, decline of buyer trust, and security breaches.
DDoS Attack Approaches
In accordance to Gcore’s statistics, in Q1–Q2 of 2023:
- UDP flood became far more common between attackers and is the most frequent approach
- SYN flood is in 2nd spot
- In third position is TCP flood
- All other methods put together accounted for just 5% of attack varieties
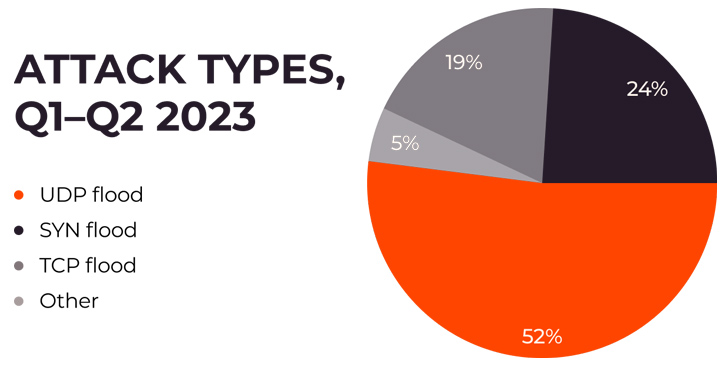 Determine 2. Attack style distribute, Q1–Q2 2023
Determine 2. Attack style distribute, Q1–Q2 2023
Alt Text: Attack types illustrated: 52% – UDP, 24% – SYN flood, 19% – TCP flood, 5% – other website traffic
In accordance to Andrey Slastenov, Head of Web Security at Gcore, there has been an maximize in the frequency of intricate, multi-vector assaults by attackers. Attackers are now employing adaptive techniques, these kinds of as combining superior-quantity UDP assaults with a substantial selection of TCP packets, and shifting from focusing on the software layer with a substantial volume of site visitors to making use of a higher volume of compact packets. These changes in strategies suggest a deliberate energy to intensify the DDoS assault by too much to handle the network infrastructure and probably bypassing mitigation actions. The supreme objective is to optimize the effects of the attack and disrupt services.
DDoS Assaults by Enterprise Sector
DDoS attacks across different organization sectors have revealed precise tendencies and impacts. According to Gcore’s report, gaming, telecom, and economical industries were the most attacked sectors in Q1–Q2 of 2023.
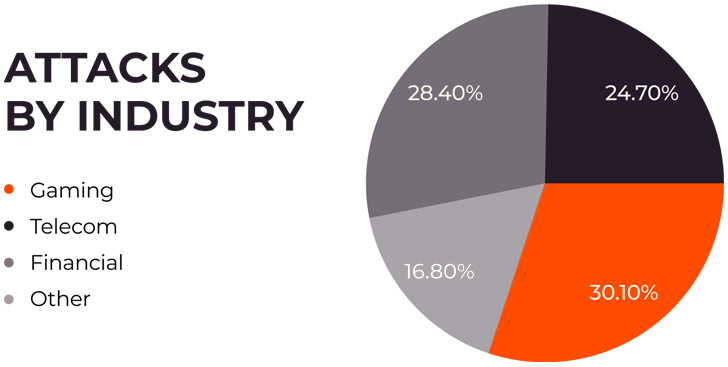 Figure 3. Most attacked industries based mostly on Gcore’s figures.
Figure 3. Most attacked industries based mostly on Gcore’s figures.
Alt Text: Attack sorts illustrated: 30.1% – Gaming, 24.7% – Telecom, 16.8% – Money, 28.4% – Other
The gaming business was the most specific sector, accounting for a substantial proportion of the DDoS attacks. Gaming platforms, functioning in real-time and catering to thousands and thousands of energetic people, practical experience detrimental penalties from even short intervals of downtime. Attackers goal to disrupt products and services, undermine player experiences, and likely obtain a aggressive advantage. The fiscal implications are significant, with gaming corporations often incurring a price of $25,000 to $40,000 for every hour of downtime.
The telecommunication sector faces a significant volume of DDoS attacks, influencing internet company companies (ISPs) and other telecom expert services. These attacks can end result in prevalent internet outages, impacting not only the telecom providers on their own but also companies and people relying on their services. The disruptive character of such assaults on critical infrastructure can have significantly-achieving consequences, disrupting communications and a variety of aspects of every day everyday living and company operations for shoppers.
The financial sector, encompassing banking companies and economical technology (FinTech) companies, stays consistently threatened by DDoS assaults. The increase in electronic banking and on-line economical products and services adoption has greater the probable for disruptive assaults that can deliver economic operations to a finish halt.
DDoS Protection from Gcore
Gcore can protect you from DDoS assaults with protection from threats at L3, L4, and L7 wielding more than 1 Tbps of filtering potential. Its serious-time targeted visitors filtering selectively blocks destructive periods, enabling typical enterprise procedures to go on for the duration of assaults. All Gcore DDoS Defense servers are geared up with significant-functionality 3rd generation Intel® Xeon® Scalable processors, enabling quickly processing so we can answer to attacks as speedily as achievable. Discover how Gcore repelled a 650 Gbps attack in January 2023.
Discovered this article appealing? Follow us on Twitter and LinkedIn to browse far more exceptional information we post.
Some parts of this article are sourced from:
thehackernews.com


 Researchers Uncover New Linux Kernel ‘StackRot’ Privilege Escalation Vulnerability
Researchers Uncover New Linux Kernel ‘StackRot’ Privilege Escalation Vulnerability