A China-based mostly advanced persistent danger (APT) team is maybe deploying small-lived ransomware households as a decoy to deal with up the accurate operational and tactical objectives behind its strategies.
The action cluster, attributed to a hacking group dubbed Bronze Starlight by Secureworks, includes the deployment of publish-intrusion ransomware such as LockFile, Atom Silo, Rook, Night Sky, Pandora, and LockBit 2..
“The ransomware could distract incident responders from figuring out the danger actors’ correct intent and cut down the likelihood of attributing the destructive activity to a authorities-sponsored Chinese threat team,” the scientists explained in a new report. “In each individual circumstance, the ransomware targets a compact selection of victims above a reasonably quick interval of time ahead of it ceases operations, seemingly completely.”
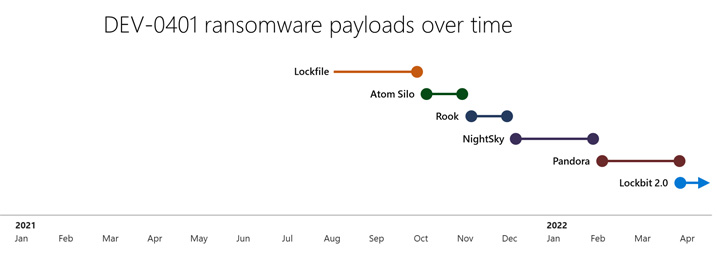
Bronze Starlight, energetic since mid-2021, is also tracked by Microsoft beneath the rising threat cluster moniker DEV-0401, with the tech large emphasizing its involvement in all stages of the ransomware attack cycle ideal from original obtain to the payload deployment.
Compared with other RaaS teams that acquire obtain from initial obtain brokers (IABs) to enter a network, attacks mounted by the actor are characterized by the use of unpatched vulnerabilities affecting Trade Server, Zoho ManageEngine ADSelfService Additionally, Atlassian Confluence (which include the newly disclosed flaw), and Apache Log4j.
Given that August 2021, the group is explained to have cycled through as numerous as six different ransomware strains these as LockFile (August), Atom Silo (Oct), Rook (November), Night time Sky (December), Pandora (February 2022), and most not long ago LockBit 2. (April).
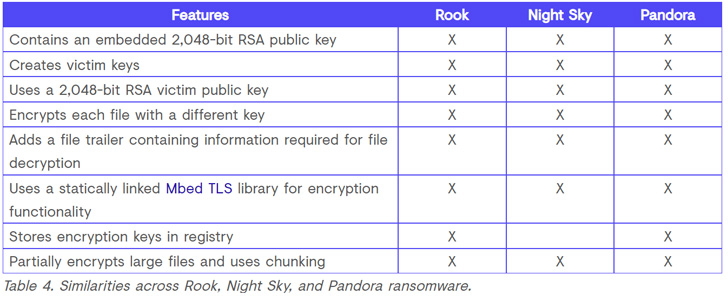
What is actually much more, similarities have been uncovered between LockFile and Atom Silo as nicely as between Rook, Evening Sky, and Pandora — the latter a few derived from Babuk ransomware, whose supply code leaked in September 2021 — indicating the perform of a frequent actor.
“Because DEV-0401 maintains and frequently rebrands their very own ransomware payloads, they can surface as different teams in payload-driven reporting and evade detections and steps against them,” Microsoft mentioned final month.
On getting a foothold within a network, Bronze Starlight is recognized to rely on techniques like working with Cobalt Strike and Windows Management Instrumentation (WMI) for lateral motion, even though starting off this month, the team has started replacing Cobalt Strike with the Sliver framework in their attacks.
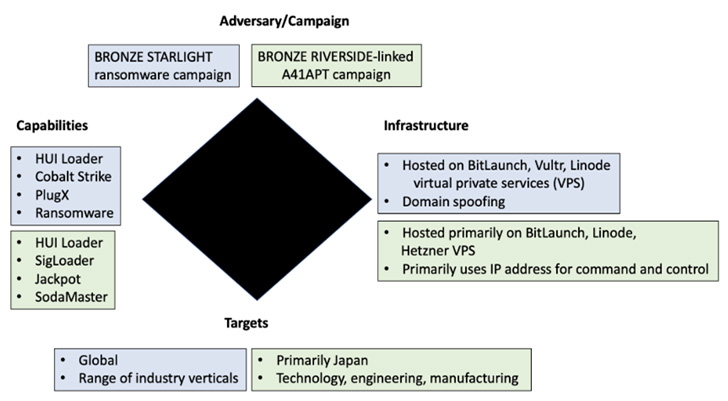
Other noticed tradecraft relates to the use of HUI Loader to start upcoming-phase encrypted payloads such as PlugX and Cobalt Strike Beacons, the latter of which is employed to deliver the ransomware, but not in advance of obtaining privileged Area Administrator qualifications.
“The use of HUI Loader to load Cobalt Strike Beacon, the Cobalt Strike Beacon configuration details, the C2 infrastructure, and the code overlap propose that the similar threat group is affiliated with these five ransomware households,” the researchers described.

It can be well worth pointing out that equally HUI Loader and PlugX, together with ShadowPad, are malware historically set to use by Chinese country-point out adversarial collectives, lending credence to the likelihood that Bronze Starlight is extra geared towards espionage than instant monetary positive aspects.
On top rated of that, the victimology sample spanning throughout the distinctive ransomware strains exhibits that a the greater part of the targets are likely to be of extra desire to Chinese govt-sponsored teams concentrated on extensive-phrase intelligence accumulating.
The crucial victims encompass pharmaceutical providers in Brazil and the U.S., a U.S.-primarily based media business with workplaces in China and Hong Kong, electronic ingredient designers and manufacturers in Lithuania and Japan, a regulation firm in the U.S., and an aerospace and defense division of an Indian conglomerate.
To that finish, the ransomware functions, besides supplying a suggests to exfiltrate information as element of the double extortion “identify-and-disgrace” plan, also offer you twin benefits in that it allows the risk actor to destroy forensic proof of their malicious actions and act as a distraction from information theft.
“It is plausible that Bronze Starlight deploys ransomware as a smokescreen relatively than for financial gain, with the underlying motivation of thieving mental home or conducting espionage,” the researchers explained.
Found this short article attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to read through more special information we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Twitter brings its closed caption toggle to Android and iOS
Twitter brings its closed caption toggle to Android and iOS