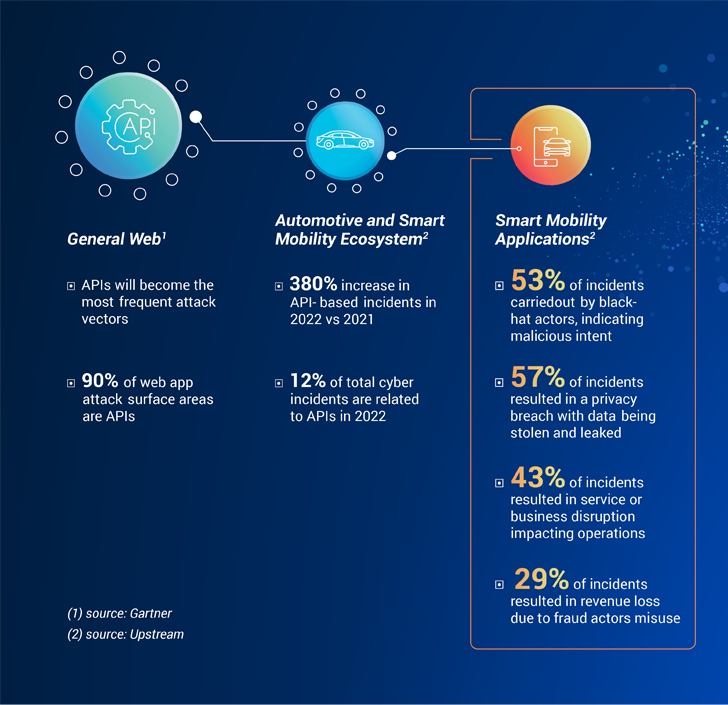
The emergence of good mobility companies and purposes has led to a sharp increase in the use of APIs in the automotive field. Even so, this improved reliance on APIs has also manufactured them 1 of the most popular attack vectors. According to Gartner, APIs account for 90% of the web application attack surface area spots.
With no shock, identical traits are emerging also in the clever mobility space. A new Automotive and Good Mobility Cybersecurity Report by Upstream Security implies that the automotive and sensible mobility ecosystem has viewed a 380% boost in API-primarily based incidents in 2022, when compared to 2021. Moreover, APIs accounted for 12% of total cyber incidents in 2022, up from only 2% in 2021.
When analyzing wise mobility applications and solutions, Upstream’s menace intelligence workforce noted that black-hat actors have been discovered to be guiding 53% of incidents, indicating destructive intent as the driving drive of the the vast majority of API-relevant assaults. The affect of these incidents goes properly past facts and PII breaches, often causing services disruptions, fraudulent functions, have confidence in problems and likely earnings reduction.
Knowledge-pushed mobility solutions reshape standard automotive revenue products
In the latest many years, motor vehicle connectivity has developed considerably, introducing progressive data-driven income possibilities for conventional automotive stakeholders as nicely as new players. Mobility over-all has turn out to be far more related, with ridesharing, auto rental providers, and even fleet management expert services all utilizing mobile applications to deliver effortless access and increased experience to individuals. Modern-day facts use scenarios supply continual monitoring and assistance stakeholders introduce new functions and prospects. In accordance to investigate by McKinsey, 30% of automotive earnings will be attributed to facts-pushed and good mobility products and services by 2030. But contrary to IT-based applications, these progressive and details-pushed purposes greatly make use of APIs that have a direct effects on vehicles on the road.
Huge targeted visitors jams triggered by manipulated API transactions
In 2022, we observed an progressively complex use of APIs in automotive and smart mobility cyberattacks. As an attack vector, APIs attract the attention of researchers and destructive actors as they involve a somewhat minimal threshold of know-how and automotive know-how. Primarily cutting down the barrier of entry of threat actors to a minimum. A solitary vulnerability in an API can pose a immediate affect on millions of cars, across different fleets. A powerful illustration of the relieve of attack and the important impression can be observed in a the latest incident in Europe: back again in mid-2022 central Moscow was gridlocked when a journey-hailing services was maliciously manipulated to ship all accessible taxis to a single locale, creating hrs-very long targeted visitors jams, impeding people’s freedom of motion, and placing community infrastructure and security at risk. In this circumstance, attackers failed to will need any knowing of how autos work or purpose, all they needed to do was to detect API vulnerabilities and exploit them.
WAF is not (generally) ample: building a contextual framework for intelligent mobility API security
Wise mobility providers have usually been checking and securing API transactions to stay away from income reduction because of to fraud, service downtime, and compromising organizational or end users personal knowledge. But, standard API security solutions have a significant “blindspot” when it will come to smart mobility. They generally fail to detect complex assaults that affect mobility purposes, belongings, and buyers owing to the lack of contextual assessment of the effect of API transactions on going vehicles.
Making certain a powerful cybersecurity posture in the smart mobility ecosystem requires growing the scope to include things like a contextual investigation of the genuine-lifestyle effect of APIs on mobility property, like vehicles on the highway. API security is little by little evolving to also integrate OT (Operational Technology) factors that correlate amongst API targeted traffic, transactions, and the contextual state of mobility assets to present a robust cybersecurity posture. The intention is to layer API discovery, profiling and checking with deep assessment of the behavior of mobility property and the impression of the unique API transaction on security. When you just take into account how OT belongings behave otherwise to IT property, be it their ignition standing, site, or speed, you can begin to solution securing them in a contextual way.
Clever mobility players are adopting a new method to securing intelligent mobility API transactions, which includes 4 key actions:
- Map the likely attack area
- Repeatedly check API traffic
- Utilize contextual anomaly detection
- Mitigate and answer to cyber threats
The to start with step is to realize the opportunity attack floor as it relates to APIs. This needs inventorying APIs utilised by services, purposes, and 3rd events, from documentation sources like Swagger as very well as the examination of live, real-time API traffic and transactions. This assessment features both equally documented, undocumented or even the depreciated-but-dwell APIs that could possibly be a “perfect” accessibility issue for danger actors.
When the attack surface area is understood, checking API visitors can help raise the cybersecurity posture by guaranteeing that any changes are documented and detected, as perfectly as any misuse of misconfigurations. When checking mobility API site visitors in serious-time, it really is important to look at the ability to take care of the scale and complexity of these transactions and identify any deviations from the usual state of the asset. When a solitary API call can get started the engine of a automobile or report back again the place of a driver – cybersecurity becomes exceptionally important.
Since intelligent mobility assets are OT in nature, the context that they are in – their condition at a supplied minute in time – can be used in securing them. Any key deviations or anomalies in their conduct can indicate potential misuse or attack. By correlating the property condition with the API traffic, cyber groups can realize the contextual implications and the effect on purposes or users. Seemingly legitimate requests can often be an indicator of destructive intent. For case in point, a solitary IP, though not suspicious originally, that sends requests to numerous autos or mobility purposes should bring about immediate suspicion and investigation.
Upstream Security has not long ago taken a move more in the contextual examination of API transactions. It relies on a sturdy digital twin, which is a dwell electronic representation of the asset’s condition, designed on facts streams from programs, backend servers, telematics providers, and a lot more. As a outcome, it offers a complete view of all mobility assets and buyers impacted. Once the attack or misconfiguration has been detected using the exclusive context delivered by being familiar with the condition of the asset, cyber groups can proficiently and immediately reply and mitigate possible risks.
This unique mobility–driven approach opens a new scope of API security pursuits in the intelligent mobility ecosystem. As innovation in this room is going so quick, introducing new transportation designs, autonomous services and experience-sharing options, getting rid of “blindspots” will continue on to be a leading priority obstacle.
Observed this write-up fascinating? Comply with us on Twitter and LinkedIn to go through additional distinctive material we write-up.
Some parts of this article are sourced from:
thehackernews.com


 ChatGPT Vulnerability May Have Exposed Users’ Payment Information
ChatGPT Vulnerability May Have Exposed Users’ Payment Information