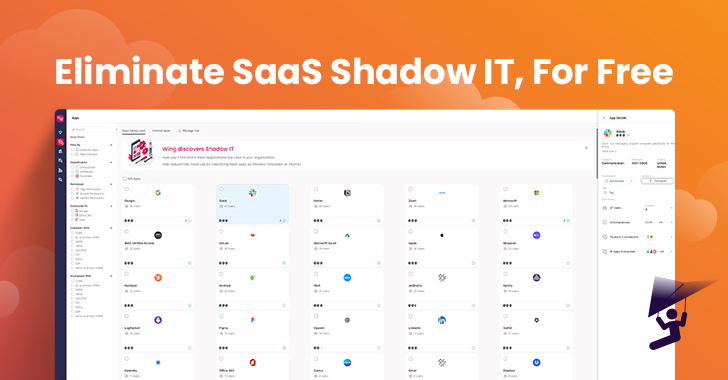
This past January, a SaaS Security Posture Management (SSPM) firm named Wing Security (Wing) made waves with the launch of its free of charge SaaS-Shadow IT discovery alternative. Cloud-dependent businesses had been invited to gain insight into their employees’ SaaS utilization by means of a wholly free of charge, self-service merchandise that operates on a “freemium” product. If a person is amazed with the answer and wants to attain additional insights or just take remediation motion, they can order the organization alternative.
“In today’s economic truth, security budgets have not always been slice down, but purchasers are considerably much more mindful in their purchasing conclusions and rightfully so. We think that you cannot secure what you do not know, so being aware of really should be a simple commodity. When you have an understanding of the magnitude of your SaaS attack layer, you can make an educated decision as to how you are heading to solve it. Discovery is the natural and basic to start with move and it must be obtainable to anybody.” stated Galit Lubetzky Sharon, Wing’s Co-Founder and CTO
The business claimed that inside of the first handful of months of launching, in excess of 200 organizations enrolled in their self-service absolutely free discovery instrument, adding to the company’s present buyer foundation. They not long ago produced a shorter report on the conclusions from hundreds of organizations that unveiled SaaS utilization, and the quantities are unsettling.
The Tangible Risks of Escalating SaaS Utilization
In 71.4% of corporations, personnel use an normal of 2.4 SaaS purposes that have been breached in the previous three months. On ordinary, 58% of SaaS applications are applied by only just one employee. A quarter of organizations’ SaaS consumers are external. These quantities, together with other interesting facts, are uncovered in the firm’s report, along with explanations as to why they think this is the scenario and the threats that must be taken into thought.
SaaS use is normally decentralized and hard to govern, and its benefits can also pose security hazards when ungoverned. Even though IAM/IM programs enable corporations get back management more than a portion of their employees’ SaaS utilization, this manage is confined to the sanctioned SaaS purposes that IT/Security knows about. The challenge is that SaaS purposes are typically onboarded by workers without involving IT or security teams. In other words, this is SaaS Shadow IT. This is in particular real for a lot of SaaS programs that do not have to have a credit history card or offer you a totally free model.
The widespread scenario is that of an worker, normally remote, on the lookout for a swift alternative to a business challenge. The remedy is usually an software that the personnel located online, granted permissions to (these can be read and generate permissions, or even execute), and then entirely forgot about. This can lead to numerous security hazards.
SaaS similar challenges can be classified into three diverse sorts:
Programs relevant
Examples incorporate risky apps with a very low security rating, indicating a higher chance that these applications are vulnerable. And programs that have just lately been compromised but have permissions into the organization’s details, right away compromising that information. In its totally free answer, Wing attaches a security rating to every single software located and alerts people to the risky applications in their SaaS stack.
Other illustrations of the risks that SaaS apps inherently convey include 3rd occasion SaaS programs, those people that “piggyback” off the identified and accepted SaaS. Or purposes that were granted significant permissions that are not often provided: In accordance to Wing, 73.3% of all permissions that have been given to purposes by the end users were not in use in more than 30 days. This begs the concern, why go away open doorways into your organization’s info when you might be not even working with the application that is asking for them?
Users Related
One particular can not overlook the human factor. Afterall, SaaS is normally onboarded specifically by the employee applying it. They are the types granting permissions, not usually knowledgeable of the this means behind these permissions. In this article far too Wing’s free of charge alternative offers some help: For the initial 100 applications discovered, Wing offers a list of the buyers who use them. For full details as to who the customers are, exterior buyers and user inconsistent behavior throughout apps, Wing provides its enterprise edition.
Info Connected
The hazards linked with data security are vast and have a full classification of products that offer with them, such as DLPs and DSPMs. However, when it will come to the SaaS purposes that workers use, data linked issues can span from delicate information getting shared on apps that are not intended for file sharing, strategies shared on community channels (Slack is a typical illustration) and even the substantial volume of files that employees share externally and then ignore about, leaving that exterior link extensive open up. Trying to keep a clean up SaaS-setting consists not only of keeping the purposes and buyers, but also controlling the data that resides in and amongst these programs.
In summary, SaaS-Shadow IT discovery has grow to be a critical region of concern for IT and security groups, as the use of SaaS apps carries on to expand promptly. Even though SaaS purposes present several rewards to firms, they also pose substantial security challenges when ungoverned. These challenges include things like the use of breached applications, granting excessive permissions, person inconsistencies, and details security issues.
It is crucial for organizations to have visibility into their employees’ SaaS utilization to make informed conclusions and just take remedial steps to mitigate these risks. In 2023, the expectation is that basic SaaS-Shadow IT discovery should really no for a longer period arrive at a charge, as it should really be a fundamental commodity for organizations aiming to safe their SaaS surroundings.
Uncovered this post fascinating? Comply with us on Twitter and LinkedIn to read additional distinctive material we publish.
Some parts of this article are sourced from:
thehackernews.com

 New FiXS ATM Malware Targeting Mexican Banks
New FiXS ATM Malware Targeting Mexican Banks