The Russia-joined APT29 (aka Cozy Bear) threat actor has been attributed to an ongoing cyber espionage marketing campaign focusing on international ministries and diplomatic entities located in NATO member states, the European Union, and Africa.
According to Poland’s Navy Counterintelligence Service and the CERT Polska workforce, the observed activity shares tactical overlaps with a cluster tracked by Microsoft as Nobelium, which is regarded for its significant-profile attack on SolarWinds in 2020.
Nobelium’s functions have been attributed to Russia’s Foreign Intelligence Provider (SVR), an business that’s tasked with guarding “people today, society, and the condition from overseas threats.”
That mentioned, the marketing campaign represents an evolution of the Kremlin-backed hacking group’s tactics, indicating persistent makes an attempt at bettering its cyber weaponry to infiltrate victim programs for intelligence accumulating.
“New resources had been utilized at the exact same time and independently of each and every other, or replacing those whose performance experienced declined, permitting the actor to manage a continual, significant operational tempo,” the organizations reported.
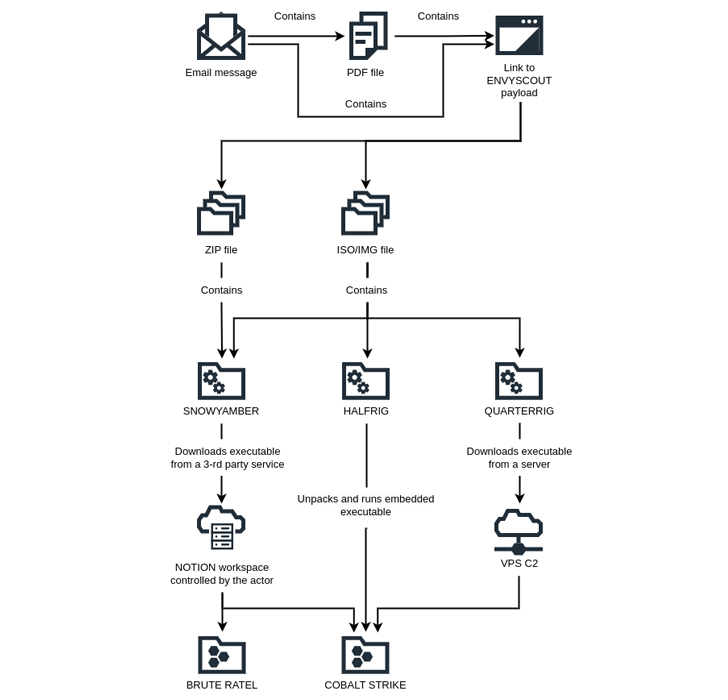
The assaults commence with spear-phishing email messages impersonating European embassies that goal to entice targeted diplomats into opening malware-laced attachments under the guise of an invitation or a meeting.
Embedded within the PDF attachment is a booby-trapped URL that sales opportunities to the deployment of an HTML dropper identified as EnvyScout (aka ROOTSAW), which is then utilized as a conduit to provide three formerly unfamiliar strains SNOWYAMBER, HALFRIG, and QUARTERRIG.
Upcoming WEBINARMaster the Art of Dark Web Intelligence Accumulating
Study the art of extracting risk intelligence from the dark web – Sign up for this professional-led webinar!
Help save My Seat!
SNOWYAMBER, also referred to as GraphicalNeutrino by Recorded Upcoming, leverages the Idea observe-getting assistance for command-and-control (C2) and downloading extra payloads these as Brute Ratel.
QUARTERRIG also functions as a downloader able of retrieving an executable from an actor-controlled server. HALFRIG, on the other hand, functions as a loader to launch the Cobalt Strike publish-exploitation toolkit contained inside of it.
It’s value noting that the disclosure dovetails with modern results from BlackBerry, which specific a Nobelium campaign targeting European Union countries, with a precise emphasis on companies that are “aiding Ukrainian citizens fleeing the country, and supplying help to the authorities of Ukraine.”
Located this report attention-grabbing? Observe us on Twitter and LinkedIn to read through extra exceptional content material we put up.
Some parts of this article are sourced from:
thehackernews.com


 UK Education Sector Suffered Most from Ransomware in 2022
UK Education Sector Suffered Most from Ransomware in 2022