The risk actors powering RTM Locker have made a ransomware pressure that’s capable of targeting Linux machines, marking the group’s 1st foray into the open up source functioning process.
“Its locker ransomware infects Linux, NAS, and ESXi hosts and appears to be motivated by Babuk ransomware’s leaked supply code,” Uptycs mentioned in a new report published Wednesday. “It uses a combination of ECDH on Curve25519 (asymmetric encryption) and Chacha20 (symmetric encryption) to encrypt files.”
RTM Locker was 1st documented by Trellix earlier this month, describing the adversary as a personal ransomware-as-a-provider (RaaS) service provider. It has its roots in a cybercrime team identified as Study The Guide (RTM) that is regarded to be energetic due to the fact at minimum 2015.
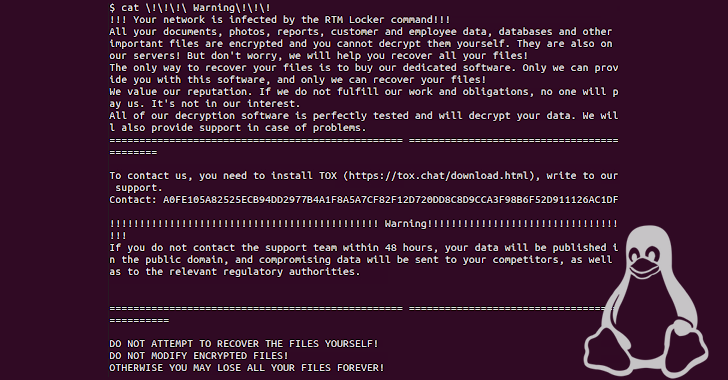
The group is notable for deliberately steering clear of higher-profile targets this kind of as critical infrastructure, legislation enforcement, and hospitals so as to draw as minor awareness as attainable. It also leverages affiliate marketers to ransom victims, in addition to leaking stolen information need to they refuse to pay out up.
The Linux taste is specifically geared to single out ESXi hosts by terminating all digital equipment operating on a compromised host prior to commencing the encryption method. The specific first infector utilized to supply the ransomware is now mysterious.
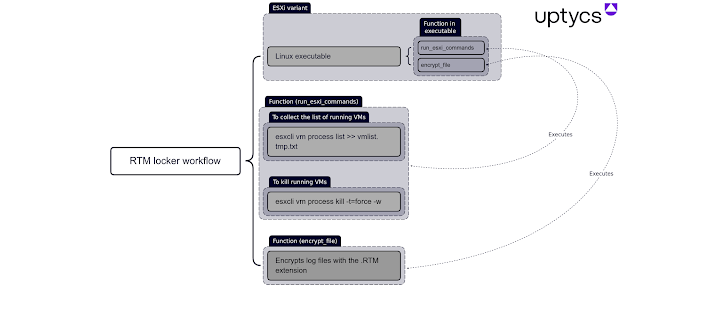
“It is statically compiled and stripped, making reverse engineering much more difficult and allowing the binary to operate on additional techniques,” Uptycs explained. “The encryption perform also uses pthreads (aka POSIX threads) to speed up execution.”
Upcoming WEBINARZero Belief + Deception: Learn How to Outsmart Attackers!
Explore how Deception can detect state-of-the-art threats, halt lateral motion, and improve your Zero Belief approach. Join our insightful webinar!
Help you save My Seat!
Pursuing successful encryption, victims are urged to get hold of the assist group inside of 48 hrs by way of Tox or risk obtaining their details published. Decrypting a file locked with RTM Locker calls for the public key appended to the stop of the encrypted file and the attacker’s non-public essential.
The advancement arrives as Microsoft exposed that vulnerable PaperCut servers are becoming actively focused by menace actors to deploy Cl0p and LockBit ransomware.
Located this write-up intriguing? Adhere to us on Twitter and LinkedIn to go through a lot more distinctive information we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Man Arrested for Selling Data on 300 Million Victims to Russians
Man Arrested for Selling Data on 300 Million Victims to Russians