A nascent Go-dependent malware known as Aurora Stealer is remaining ever more deployed as aspect of campaigns made to steal sensitive info from compromised hosts.
“These infection chains leveraged phishing web pages impersonating obtain webpages of respectable software program, together with cryptocurrency wallets or distant obtain instruments, and the 911 process earning use of YouTube films and Search engine optimisation-poised pretend cracked application download websites,” cybersecurity firm SEKOIA claimed.
To start with marketed on Russian cybercrime discussion boards in April 2022, Aurora was made available as a commodity malware for other threat actors, describing it as a “multi-objective botnet with thieving, downloading and remote accessibility abilities.”
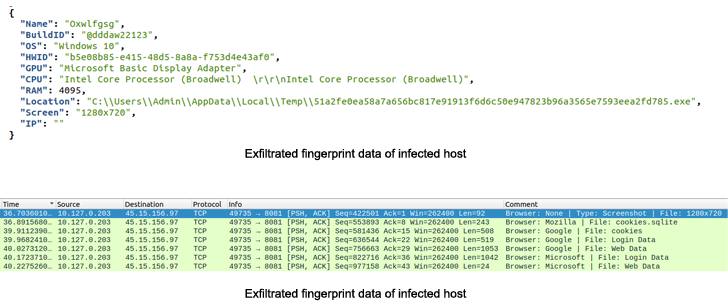
In the intervening months, the malware has been scaled down to a stealer that can harvest information of desire, data from 40 cryptocurrency wallets, and purposes like Telegram.
Aurora also will come with a loader that can deploy a subsequent-stage payloading working with a PowerShell command.
The cybersecurity corporation explained at the very least distinctive cybercrime teams, identified as traffers, who are liable for redirecting user’s website traffic to malicious content operated by other actors, have added Aurora to their toolset, either exclusively or along with RedLine and Raccoon.
“Aurora is a different infostealer concentrating on knowledge from browsers, cryptocurrency wallets, local methods, and acting as a loader,” SEKOIA claimed. “Marketed at a higher rate on industry areas, gathered knowledge is of distinct fascination to cybercriminals, permitting them to have out comply with-up valuable campaigns, together with Significant Match Looking functions.”
The advancement also arrives as researchers from Palo Alto Networks Unit 42 specific an improved edition of an additional stealer known as Typhon Stealer.
The new variant, dubbed Typhon Reborn, is designed to steal from cryptocurrency wallets, web browsers, and other process data, though getting rid of formerly existing characteristics like keylogging and cryptocurrency mining in a possible try to decrease detection.
“Typhon Stealer offered menace actors with an easy to use, configurable builder for employ the service of,” Unit 42 researchers Riley Porter and Uday Pratap Singh said.
“Typhon Reborn’s new anti-examination methods are evolving along field traces, turning into extra successful in the evasion strategies when broadening their toolset for stealing target information.”
Uncovered this report intriguing? Observe THN on Fb, Twitter and LinkedIn to study a lot more unique articles we article.
Some parts of this article are sourced from:
thehackernews.com


 The best gifts for gamers in 2022
The best gifts for gamers in 2022