Security researchers have warned about an “simply exploitable” flaw in the Microsoft Visual Studio installer that could be abused by a malicious actor to impersonate a reputable publisher and distribute malicious extensions.
“A danger actor could impersonate a popular publisher and issue a destructive extension to compromise a focused procedure,” Varonis researcher Dolev Taler mentioned. “Destructive extensions have been made use of to steal delicate information and facts, silently entry and improve code, or choose whole manage of a process.”
The vulnerability, which is tracked as CVE-2023-28299 (CVSS score: 5.5), was dealt with by Microsoft as component of its Patch Tuesday updates for April 2023, describing it as a spoofing flaw.

The bug discovered by Varonis has to do with the Visible Studio person interface, which will allow for spoofed publisher digital signatures.
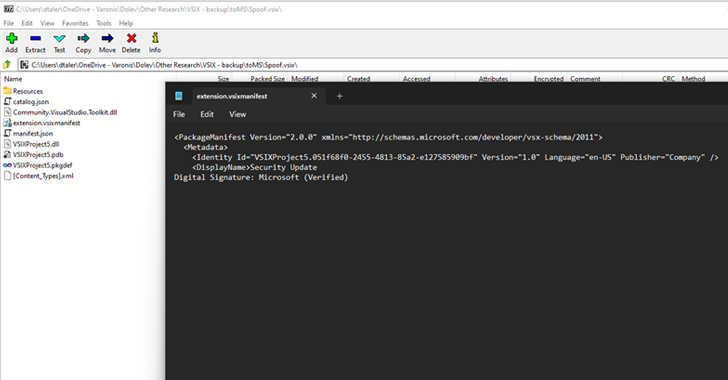
Specifically, it trivially bypasses a restriction that helps prevent buyers from moving into info in the “products identify” extension house by opening a Visual Studio Extension (VSIX) package deal as a .ZIP file and then manually introducing newline figures to the “DisplayName” tag in the “extension.vsixmanifest” file.
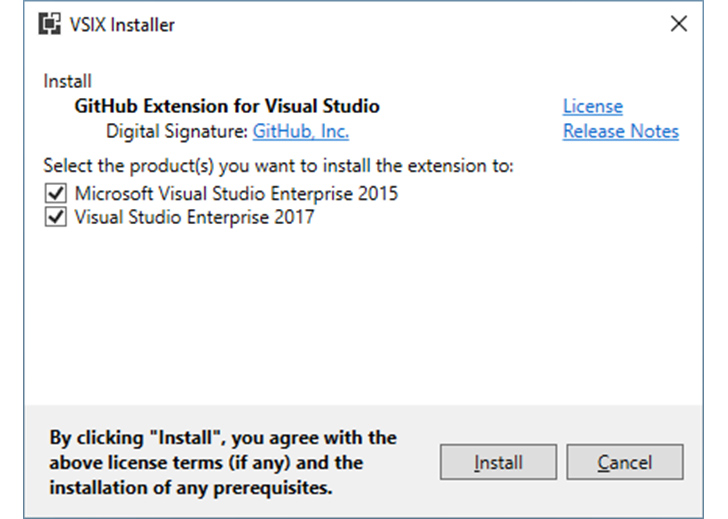
By introducing sufficient newline characters in the vsixmanifest file and including pretend “Electronic Signature” text, it was located that warnings about the extension not being digitally signed could be quickly suppressed, therefore tricking a developer into setting up it.
Upcoming WEBINAR🔐 Mastering API Security: Being familiar with Your Legitimate Attack Floor
Uncover the untapped vulnerabilities in your API ecosystem and get proactive techniques to ironclad security. Join our insightful webinar!
Sign up for the Session.wn-button,.wn-label,.wn-label:just afterscreen:inline-block.test_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px strong #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-prime-remaining-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-suitable-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-dimension:13pxmargin:20px 0font-body weight:600letter-spacing:.6pxcolor:#596cec.wn-label:right afterwidth:50pxheight:6pxcontent:”border-best:2px good #d9deffmargin: 8px.wn-titlefont-measurement:21pxpadding:10px 0font-pounds:900text-align:leftline-peak:33px.wn-descriptiontext-align:leftfont-measurement:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-shade:#4469f5font-measurement:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-pounds:500letter-spacing:.2px
In a hypothetical attack state of affairs, a bad actor could mail a phishing email bearing the spoofed VSIX extension by camouflaging it as a authentic software program update and, submit-set up, acquire a foothold into the qualified device.
The unauthorized accessibility could then be applied as a launchpad to achieve deeper manage of the network and facilitate the theft of sensitive details.
“The very low complexity and privileges expected make this exploit uncomplicated to weaponize,” Taler reported. “Threat actors could use this vulnerability to issue spoofed malicious extensions with the intention of compromising techniques.”
Identified this report intriguing? Stick to us on Twitter and LinkedIn to browse much more exclusive material we put up.
Some parts of this article are sourced from:
thehackernews.com


 Swiss Government Targeted by Series of Cyber-Attacks
Swiss Government Targeted by Series of Cyber-Attacks